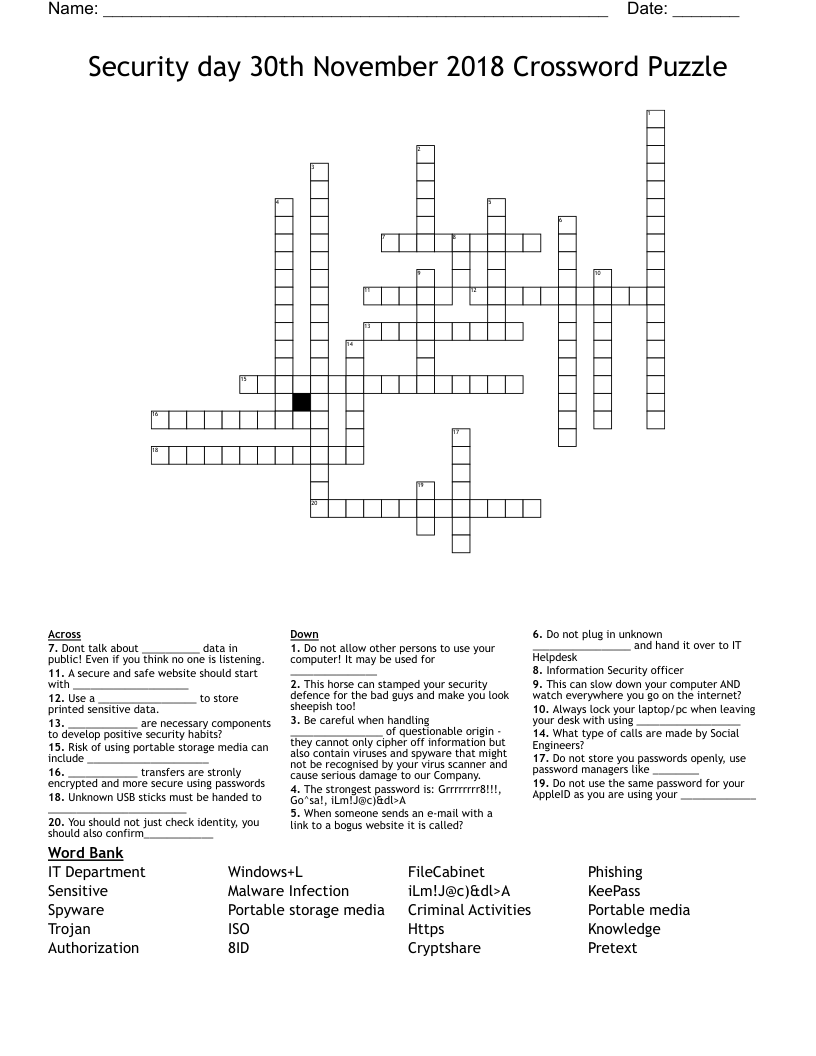
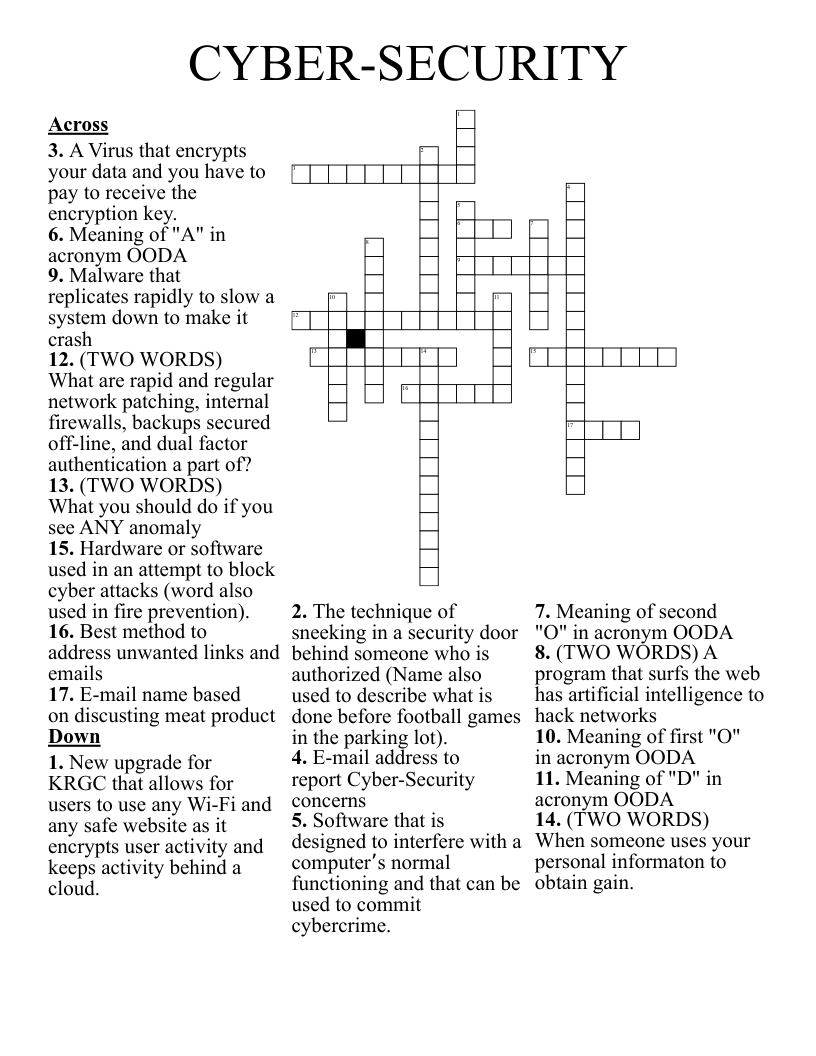
Security day 30th November 2018 Crossword Puzzle
This printable crossword puzzle on the topic of Computer Science & Technology has 20 clues. Answers range from 3 to 20 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
Do not store you passwords openly, use password managers like ________
The strongest password is: Grrrrrrrr8!!!, Go^sa!, iLm!J@c)&dl>A
A secure and safe website should start with ____________________
____________ are necessary components to develop positive security habits?
When someone sends an e-mail with a link to a bogus website it is called?
This can slow down your computer AND watch everywhere you go on the internet?
What type of calls are made by Social Engineers?
Information Security officer
This horse can stamped your security defence for the bad guys and make you look sheepish too!
You should not just check identity, you should also confirm____________
Do not plug in unknown _________________ and hand it over to IT Helpdesk
Use a _________________ to store printed sensitive data.
Do not use the same password for your AppleID as you are using your _____________
Always lock your laptop/pc when leaving your desk with using __________________
Do not allow other persons to use your computer! It may be used for _______________
Dont talk about __________ data in public! Even if you think no one is listening.
____________ transfers are stronly encrypted and more secure using passwords
Unknown USB sticks must be handed to ________________________
Be careful when handling ________________ of questionable origin - they cannot only cipher off information but also contain viruses and spyware that might not be recognised by your virus scanner and cause serious damage to our Company.
Risk of using portable storage media can include _____________________