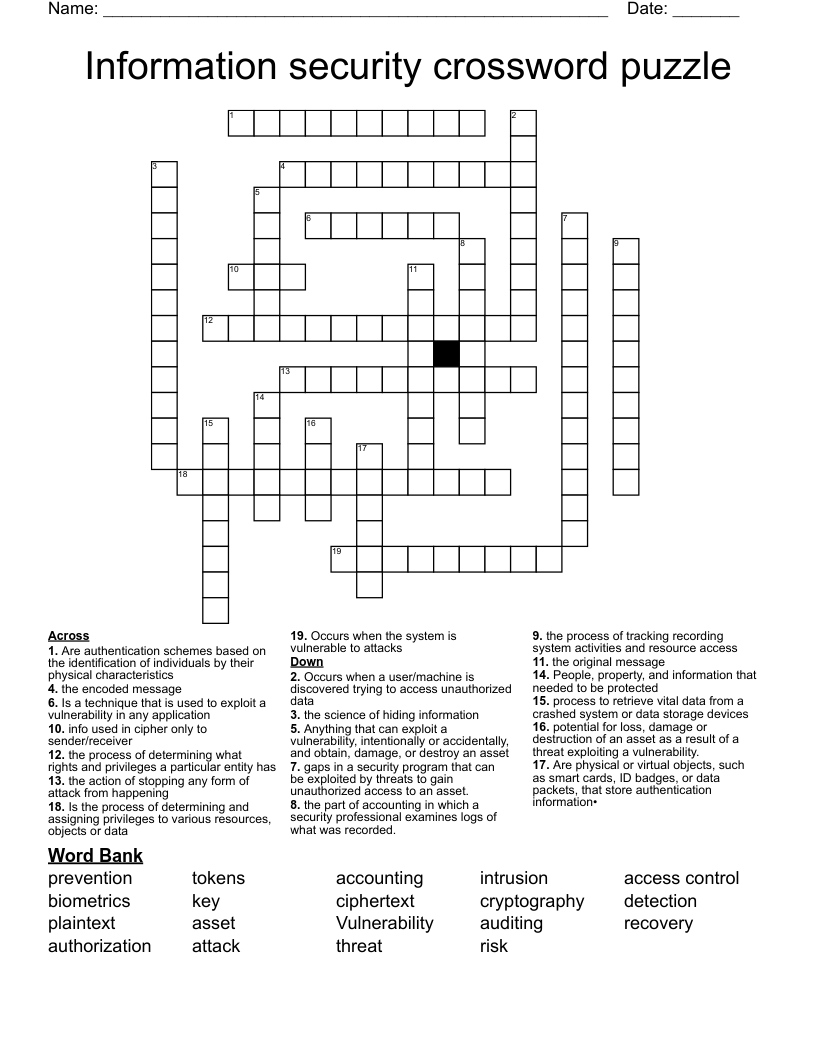
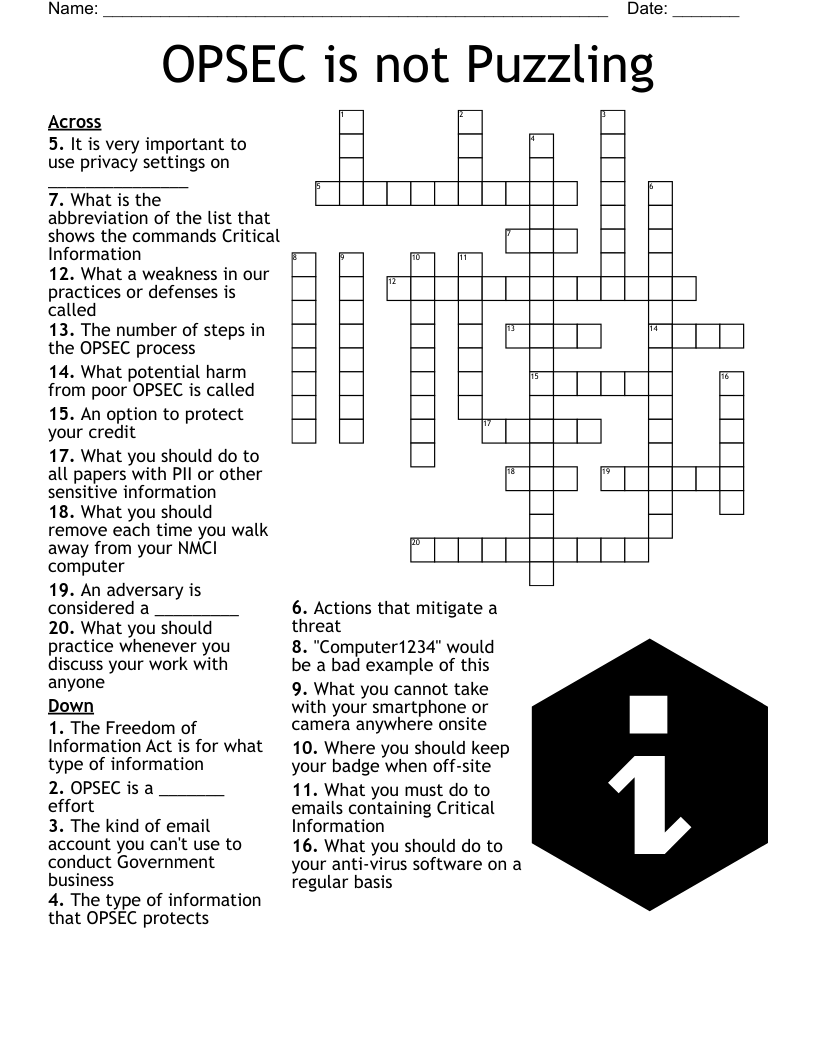
Information security crossword puzzle
This printable crossword puzzle on the topic of Computer Science & Technology has 19 clues. Answers range from 3 to 13 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
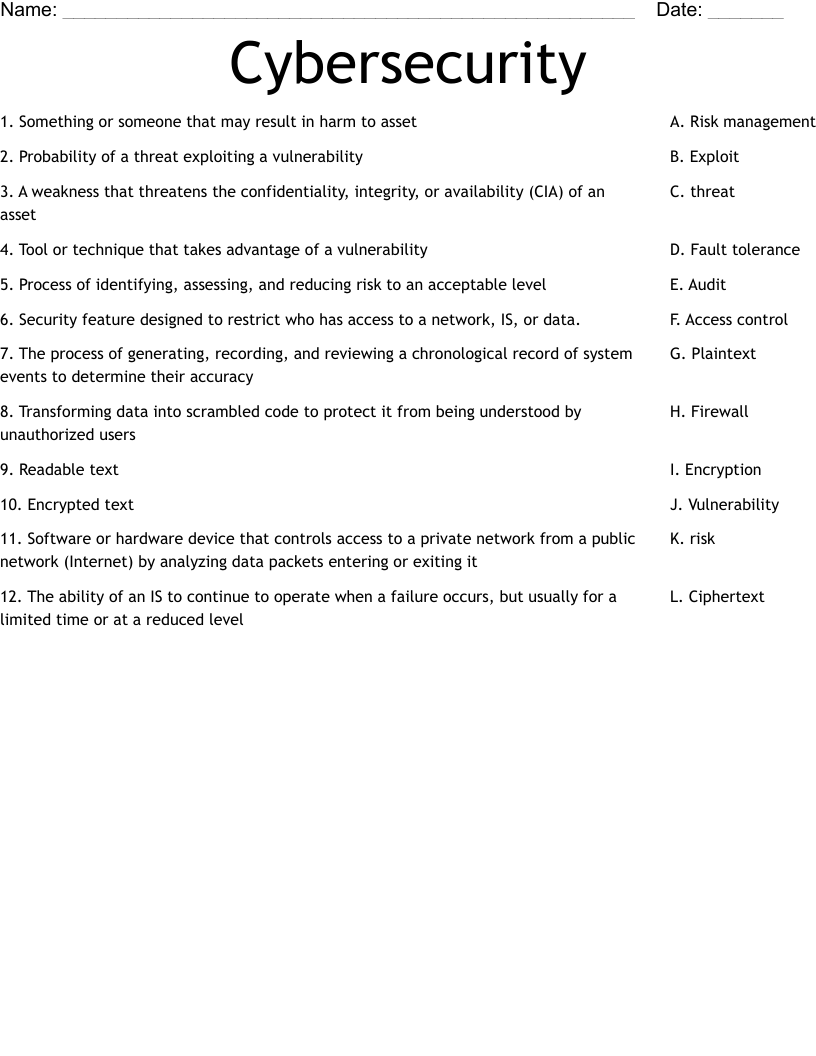
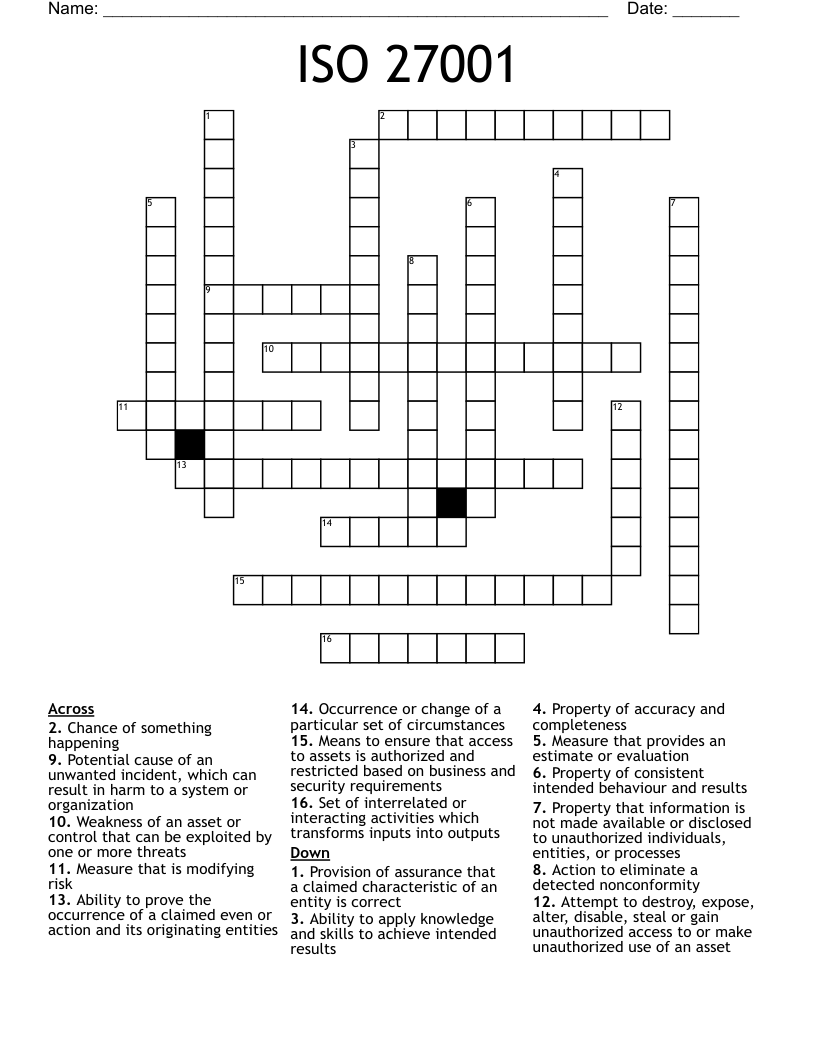
Is a technique that is used to exploit a vulnerability in any application
gaps in a security program that can be exploited by threats to gain unauthorized access to an asset.
potential for loss, damage or destruction of an asset as a result of a threat exploiting a vulnerability.
People, property, and information that needed to be protected
Anything that can exploit a vulnerability, intentionally or accidentally, and obtain, damage, or destroy an asset
Occurs when the system is vulnerable to attacks
process to retrieve vital data from a crashed system or data storage devices
Occurs when a user/machine is discovered trying to access unauthorized data
the action of stopping any form of attack from happening
the process of determining what rights and privileges a particular entity has
Is the process of determining and assigning privileges to various resources, objects or data
the process of tracking recording system activities and resource access
the part of accounting in which a security professional examines logs of what was recorded.
Are physical or virtual objects, such as smart cards, ID badges, or data packets, that store authentication information•
Are authentication schemes based on the identification of individuals by their physical characteristics
the science of hiding information
the original message
the encoded message
info used in cipher only to sender/receiver