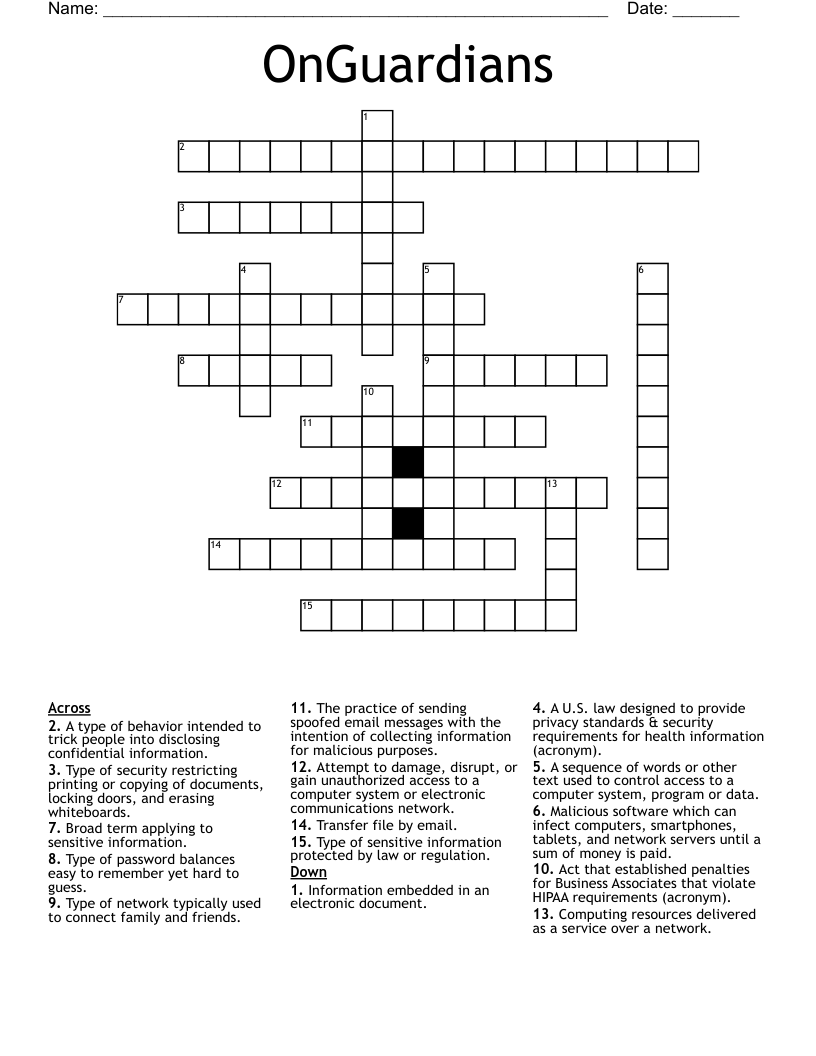
OnGuardians Crossword
This printable crossword puzzle on the topic of Computer Science & Technology has 15 clues. Answers range from 5 to 17 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
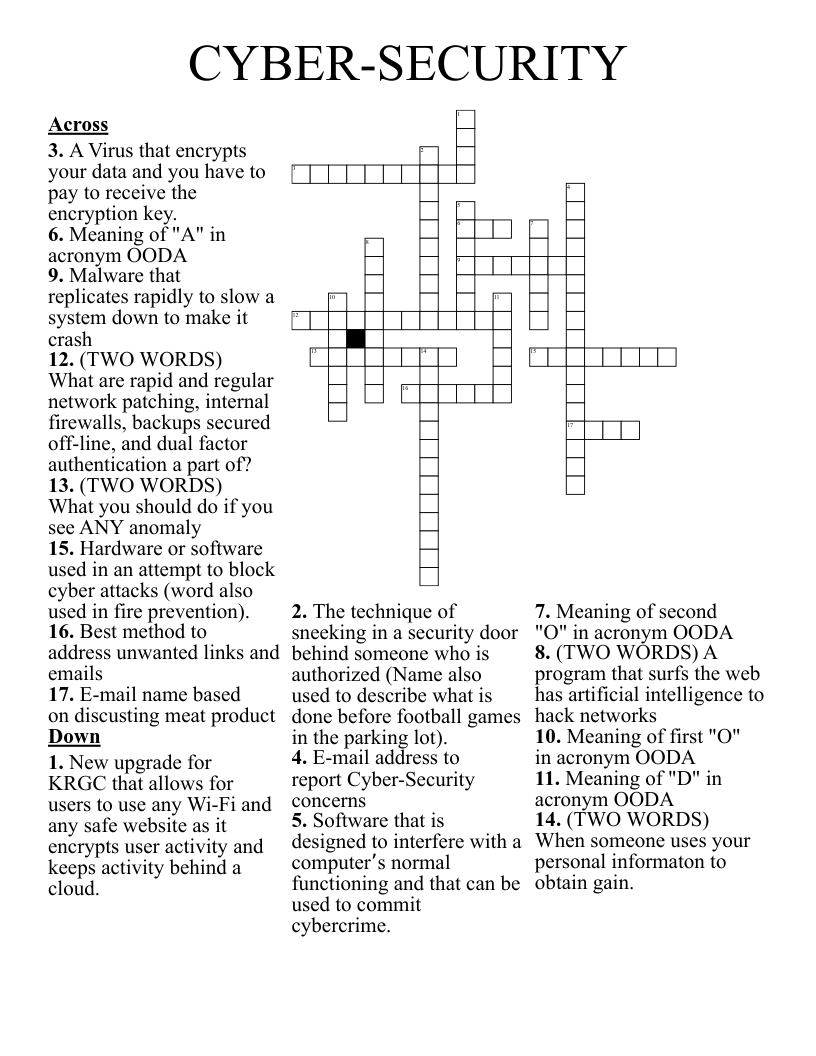
Attempt to damage, disrupt, or gain unauthorized access to a computer system or electronic communications network.
Broad term applying to sensitive information.
Type of sensitive information protected by law or regulation.
Malicious software which can infect computers, smartphones, tablets, and network servers until a sum of money is paid.
Transfer file by email.
Computing resources delivered as a service over a network.
Type of network typically used to connect family and friends.
Type of password balances easy to remember yet hard to guess.
A sequence of words or other text used to control access to a computer system, program or data.
Information embedded in an electronic document.
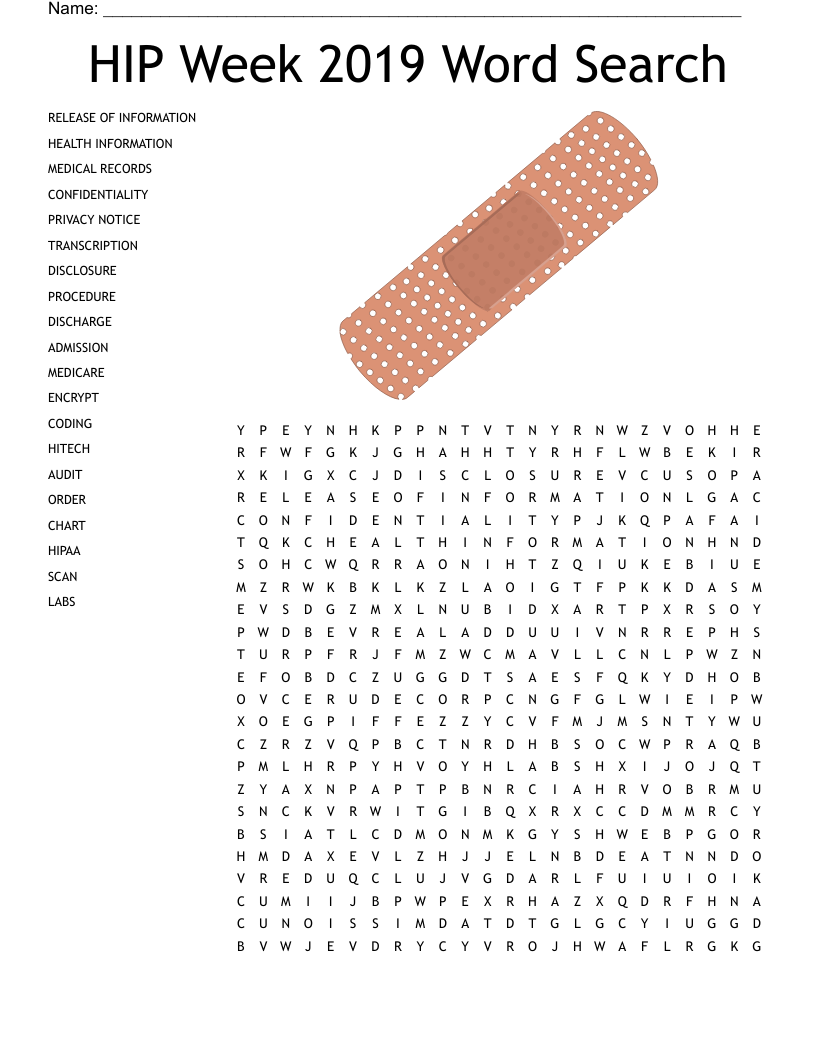
A U.S. law designed to provide privacy standards & security requirements for health information (acronym).
Act that established penalties for Business Associates that violate HIPAA requirements (acronym).
The practice of sending spoofed email messages with the intention of collecting information for malicious purposes.
Type of security restricting printing or copying of documents, locking doors, and erasing whiteboards.
A type of behavior intended to trick people into disclosing confidential information.