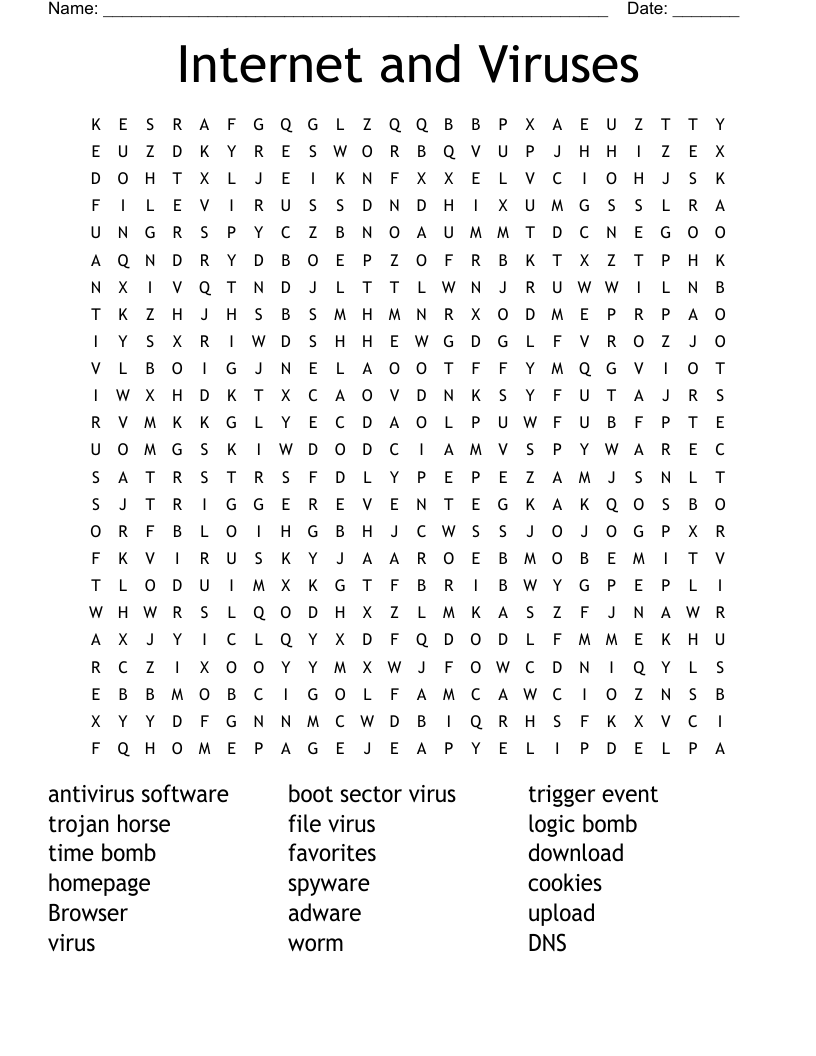
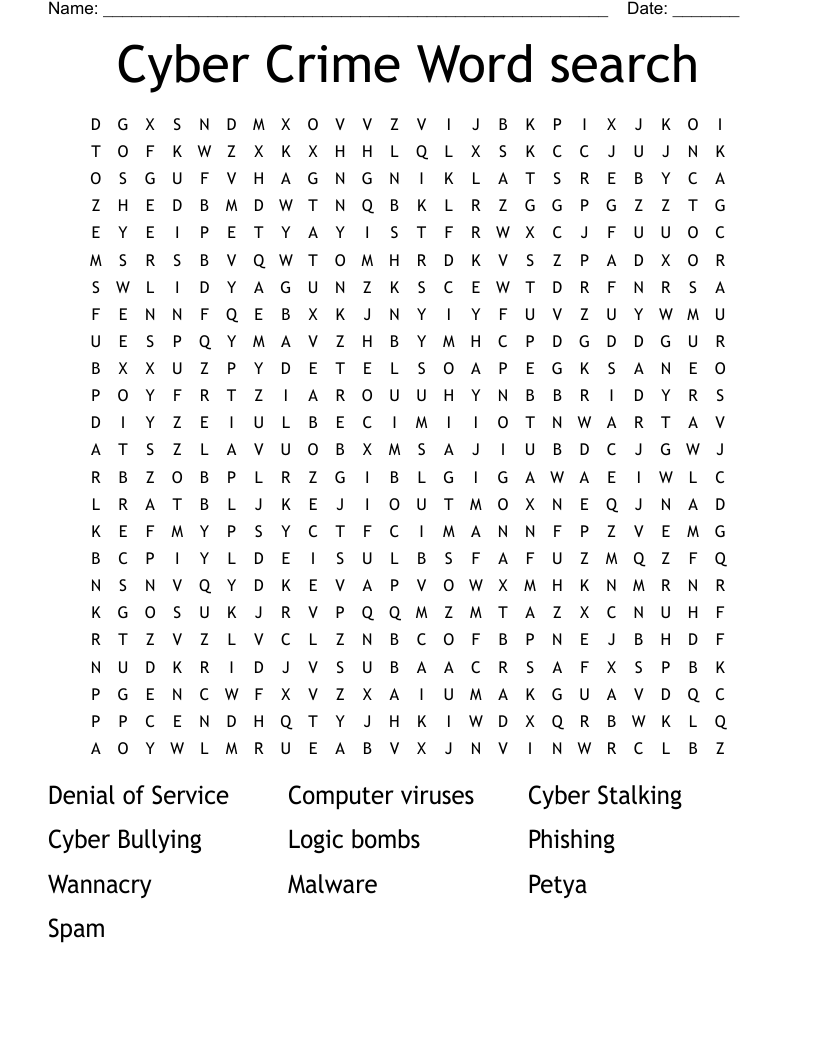
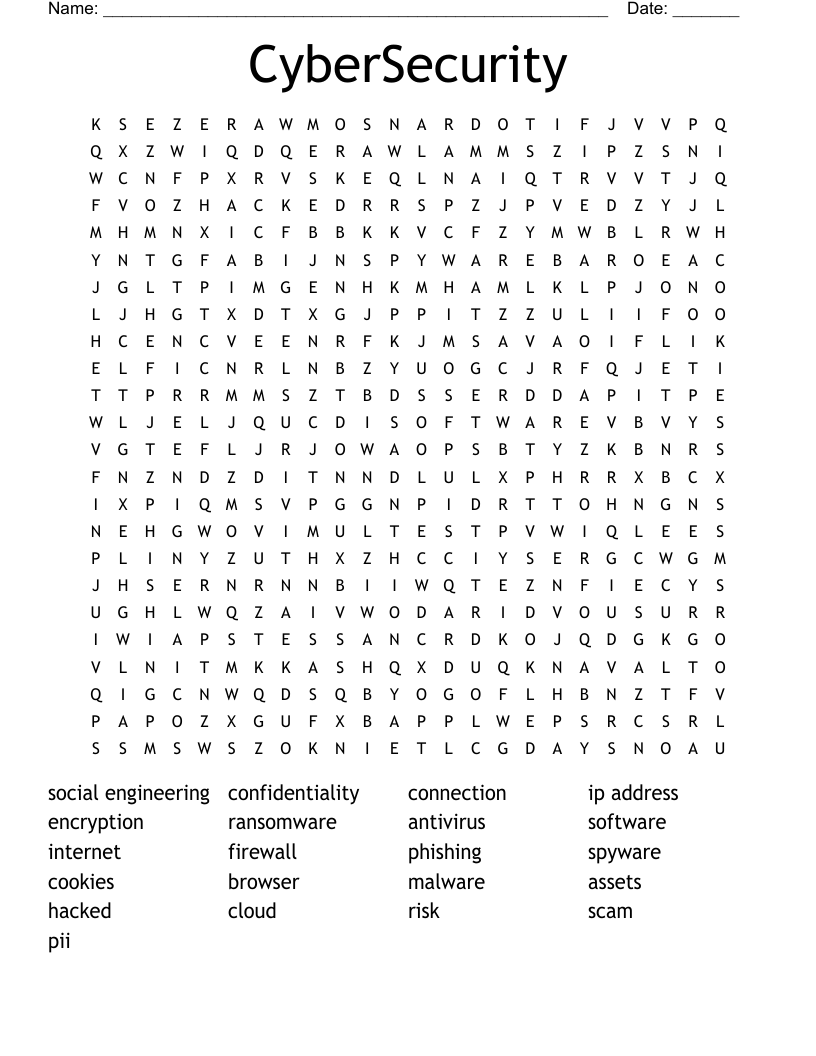
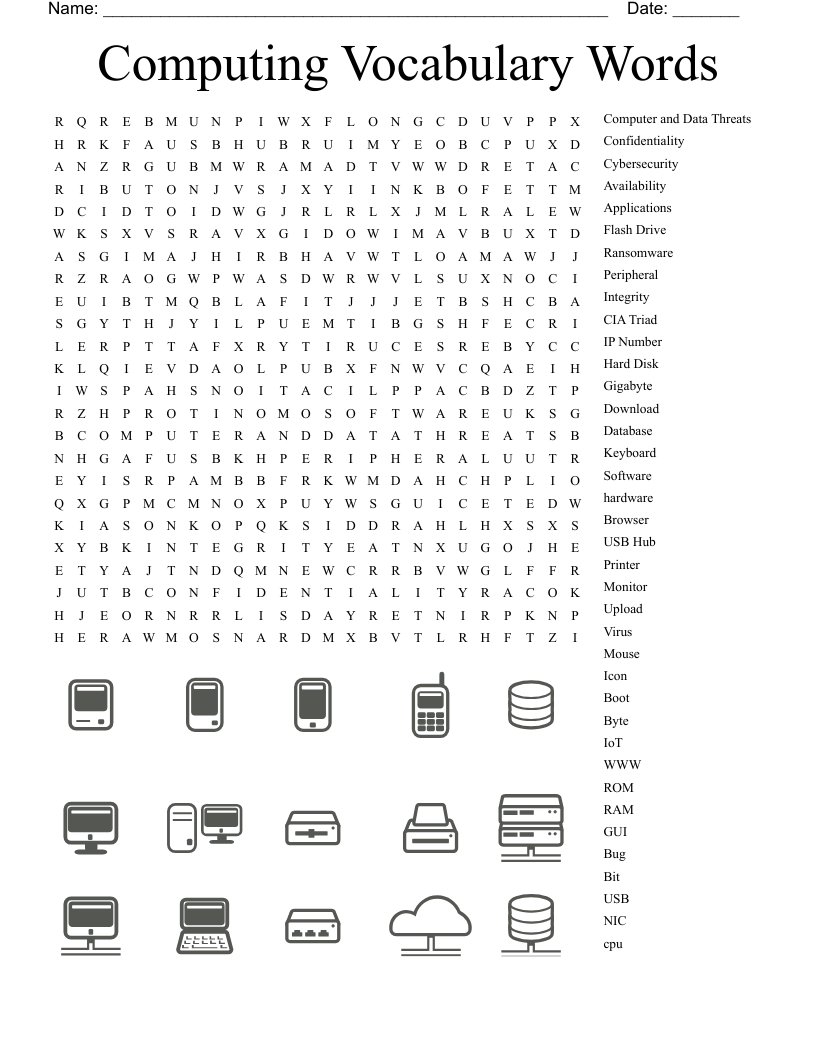
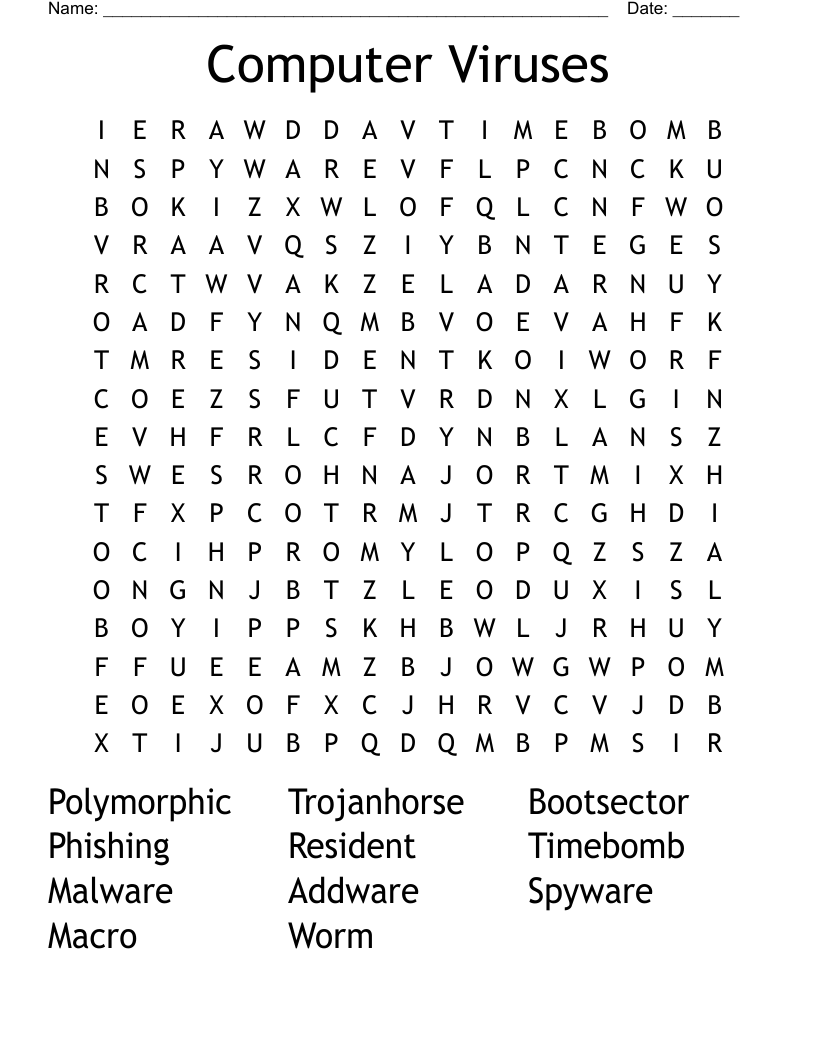
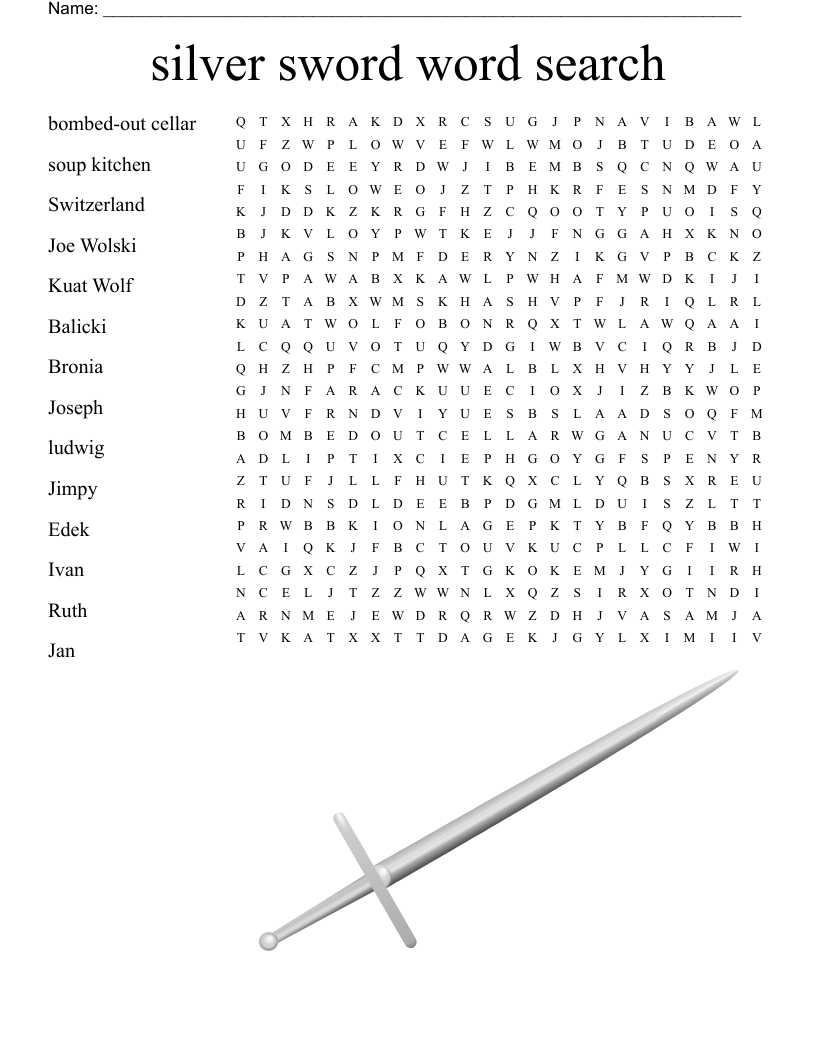
Internet and Viruses Word Search
This printable word search puzzle on the topic of Computer Science & Technology contains 18 hidden words in a 24x24 letter grid. Words go horizontally, vertically, backwards, and diagonally. This word search is also available to download as a Microsoft Word document or a PDF.
Description
antivirus software
boot sector virus
trigger event
trojan horse
file virus
logic bomb
time bomb
favorites
download
homepage
spyware
cookies
Browser
adware
upload
virus
worm
DNS
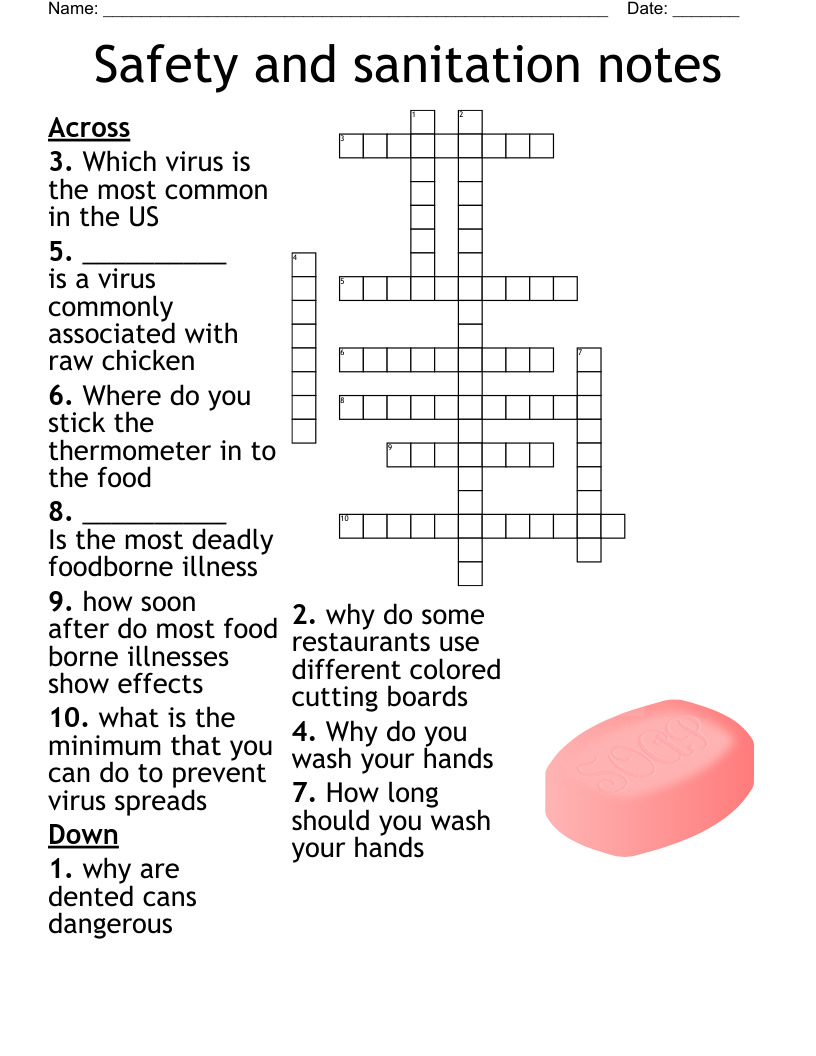
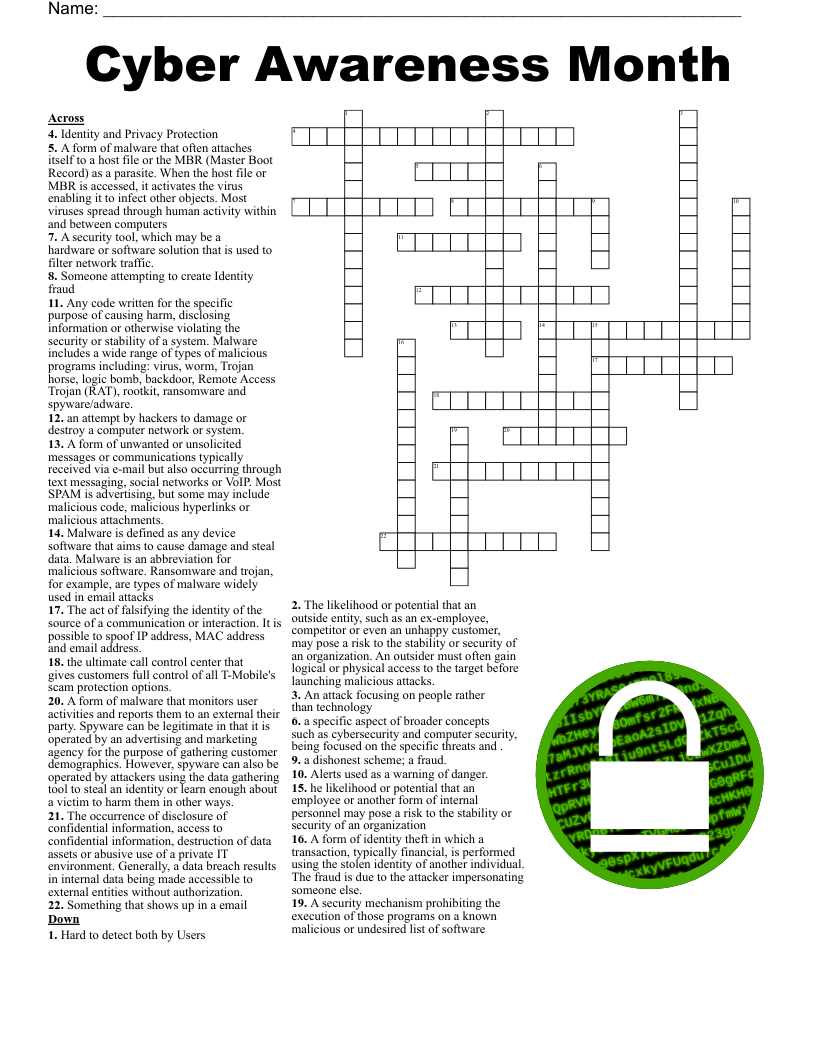
Customize
Add, edit, delete clues, and customize this puzzle. Print copies for an entire class.