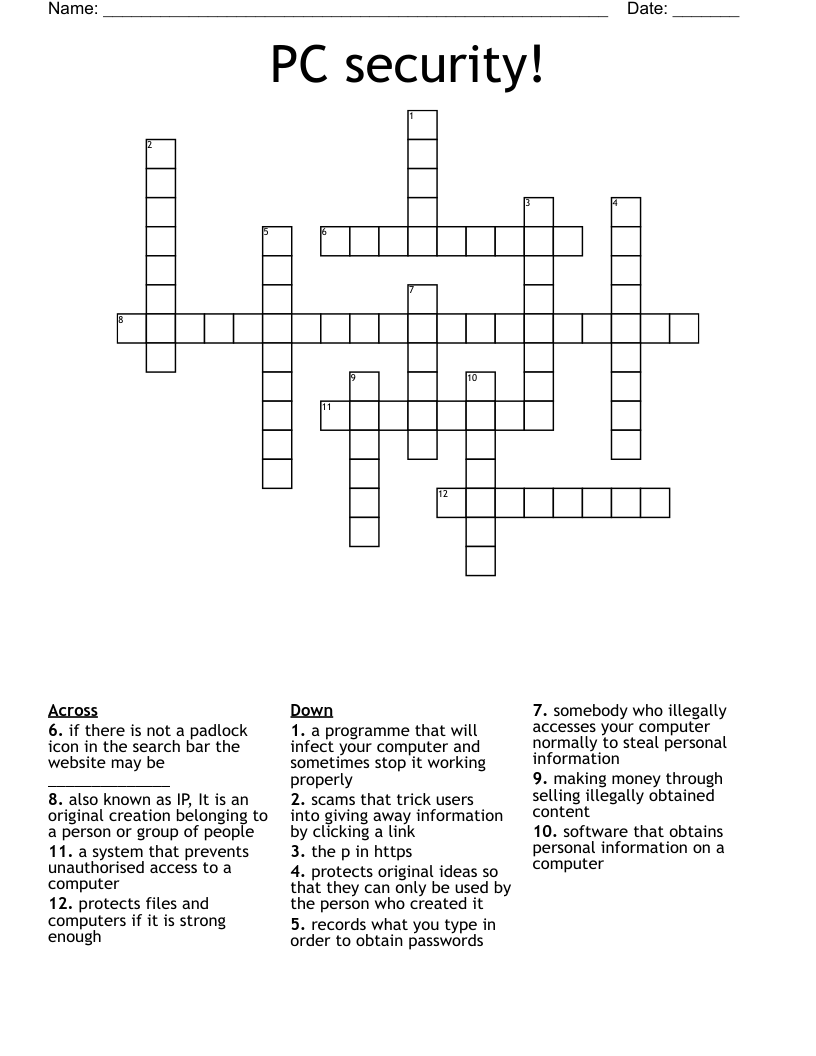
PC security! Crossword
This printable crossword puzzle has 12 clues. Answers range from 5 to 20 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
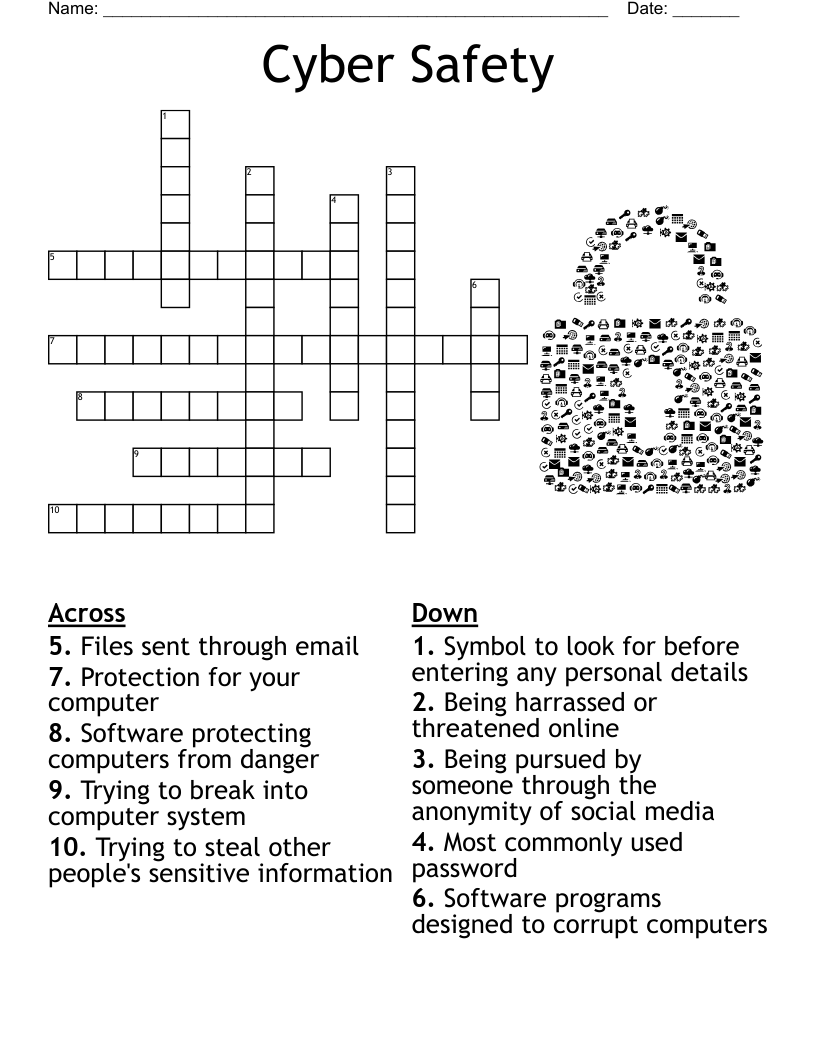
protects original ideas so that they can only be used by the person who created it
somebody who illegally accesses your computer normally to steal personal information
also known as IP, It is an original creation belonging to a person or group of people
software that obtains personal information on a computer
making money through selling illegally obtained content
a programme that will infect your computer and sometimes stop it working properly
records what you type in order to obtain passwords
protects files and computers if it is strong enough
the p in https
a system that prevents unauthorised access to a computer
scams that trick users into giving away information by clicking a link
if there is not a padlock icon in the search bar the website may be ______________