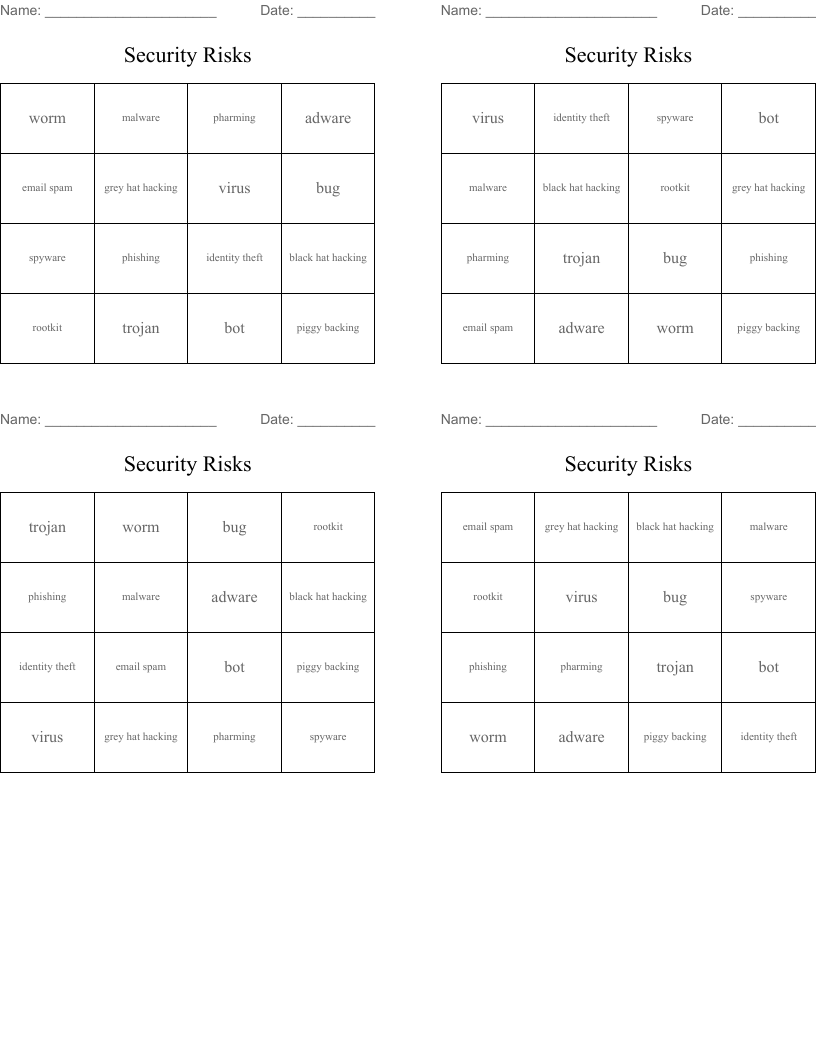
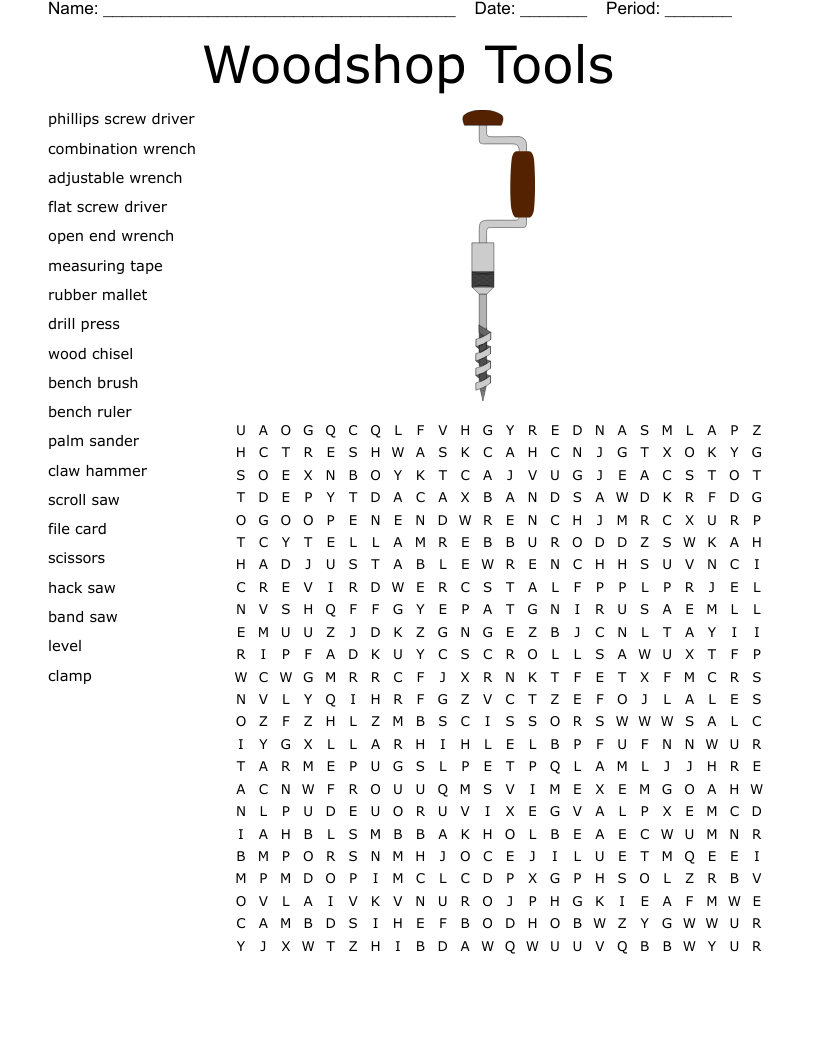
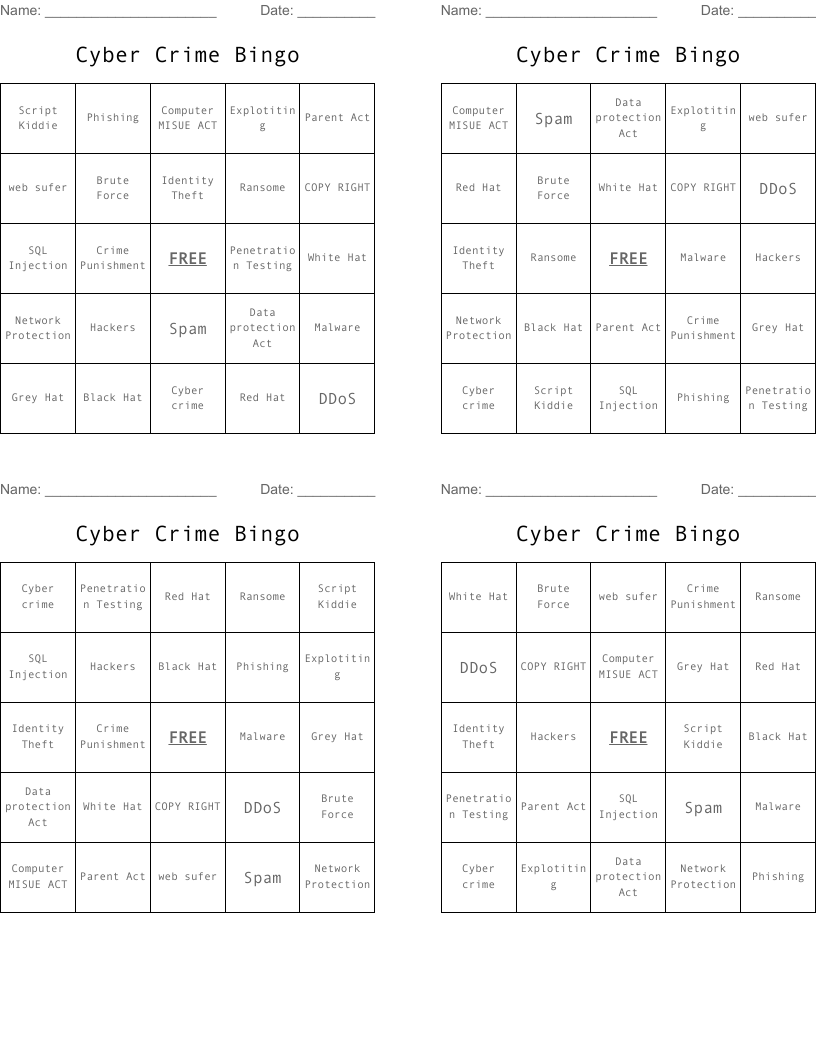
Security Risks Bingo Cards
This printable bingo card set has 16 unique items on a 4x4 grid. Each card is randomized so every player gets a different arrangement.
Description
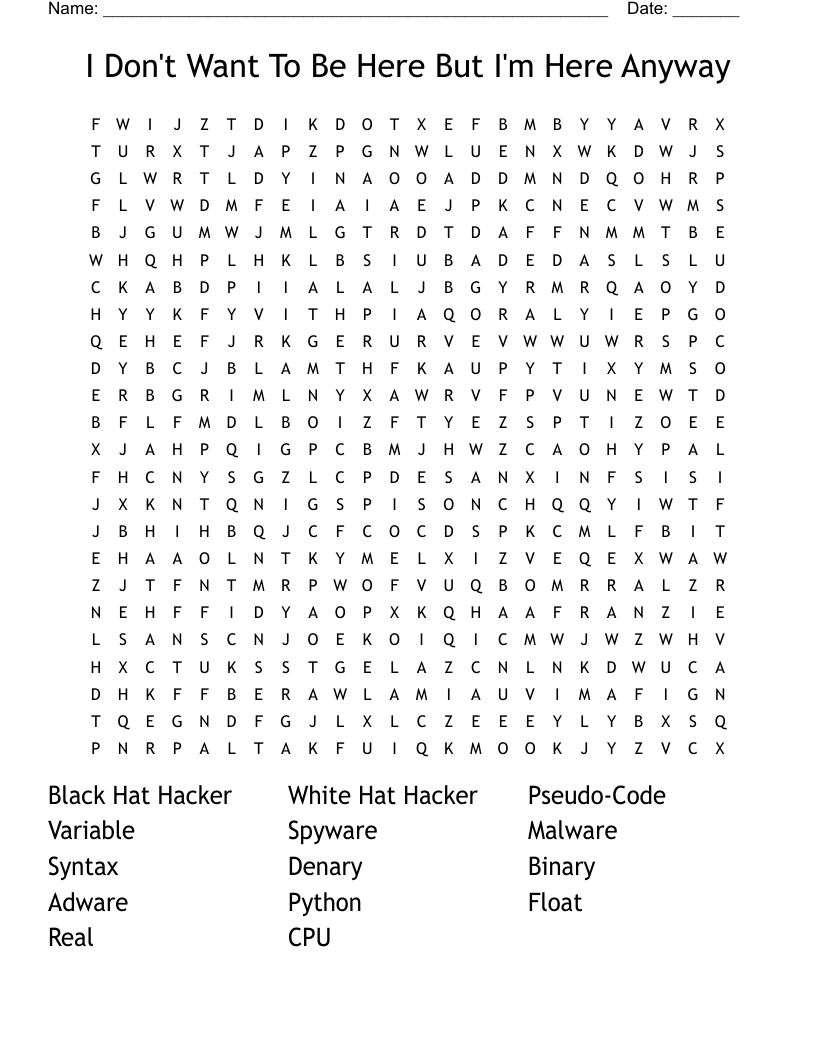
adware
malware
grey hat hacking
black hat hacking
phishing
pharming
identity theft
spyware
email spam
bug
bot
virus
worm
trojan
rootkit
piggy backing
Customize
Add, edit, delete clues, and customize this puzzle. Print copies for an entire class.