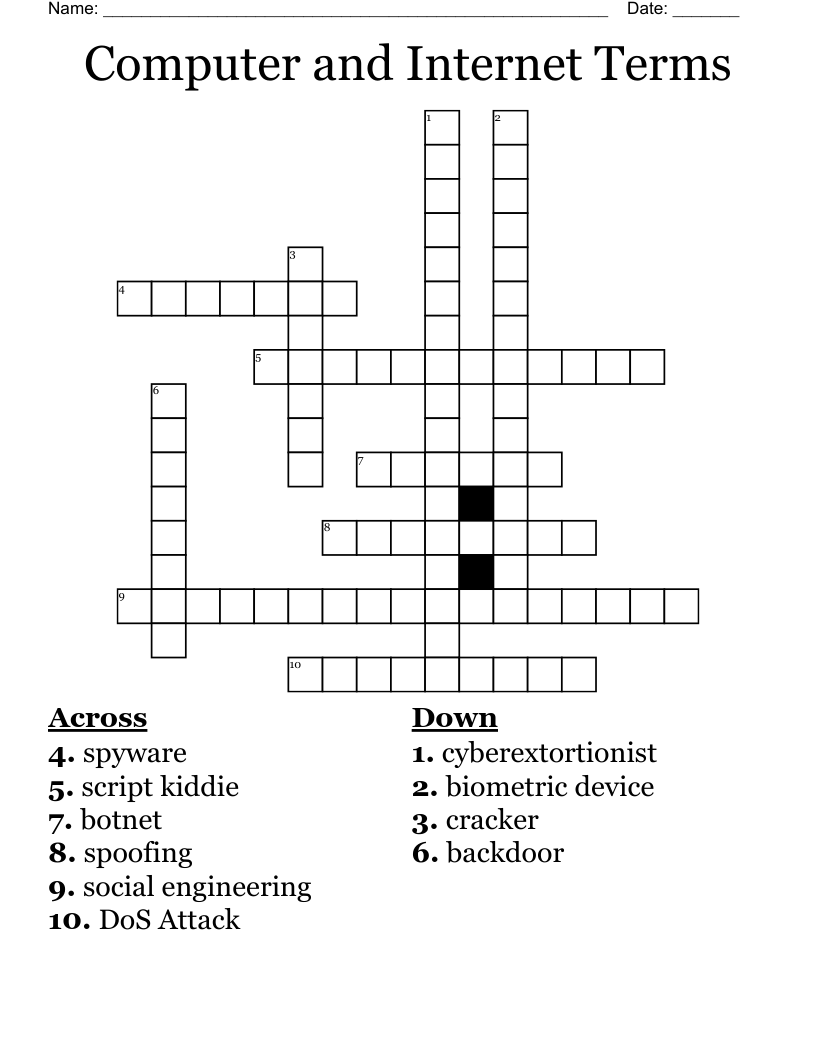
Computer and Internet Terms Crossword
This printable crossword puzzle on the topic of Computer Science & Technology has 10 clues. Answers range from 6 to 17 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
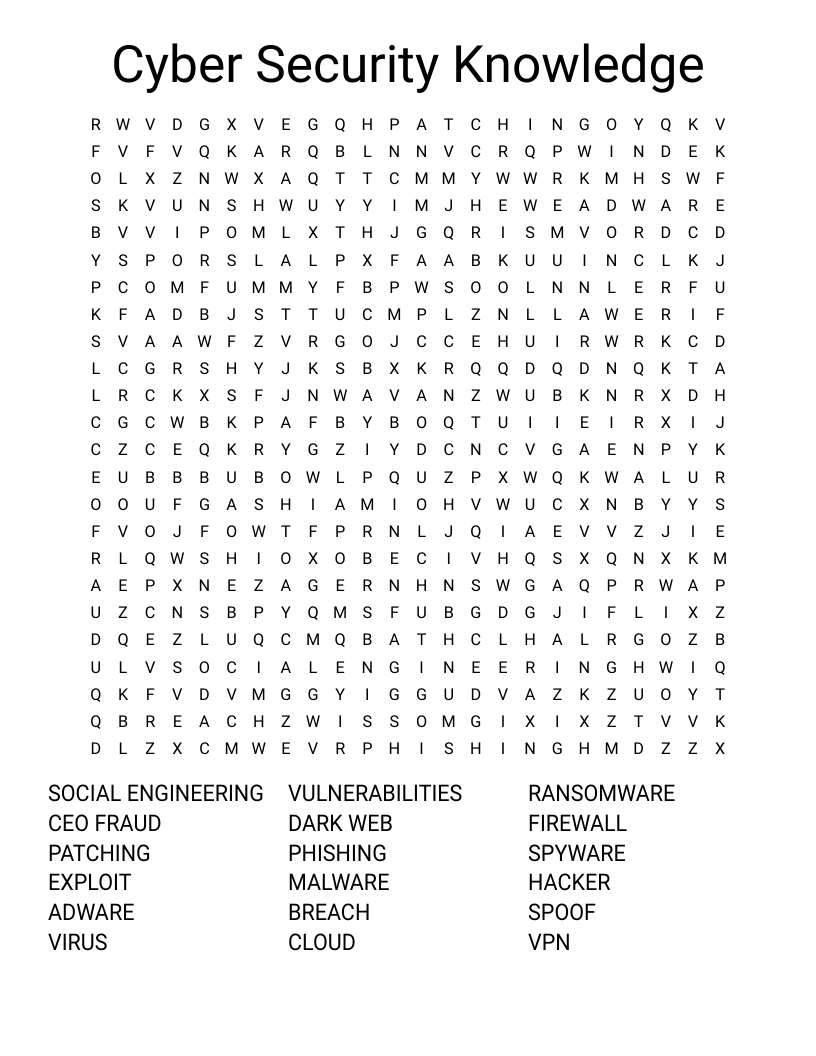
spyware
spoofing
social engineering
script kiddie
DoS Attack
cyberextortionist
cracker
botnet
biometric device
backdoor
Customize
Add, edit, delete clues, and customize this puzzle. Print copies for an entire class.