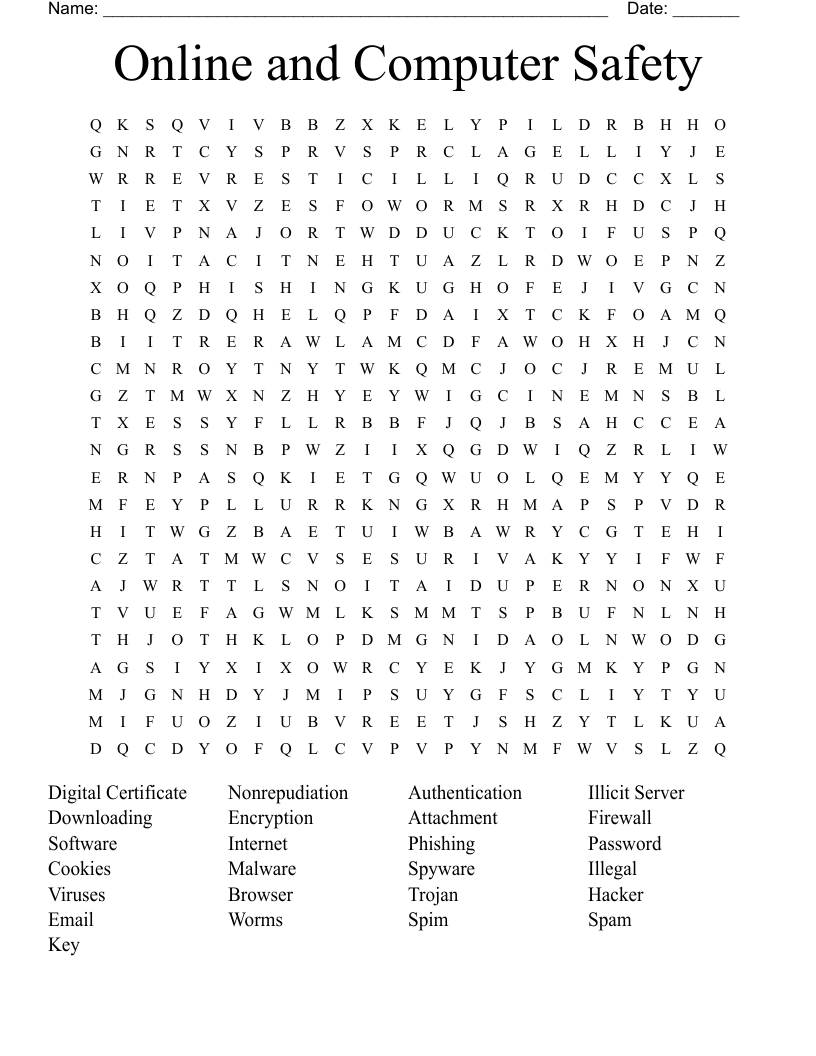
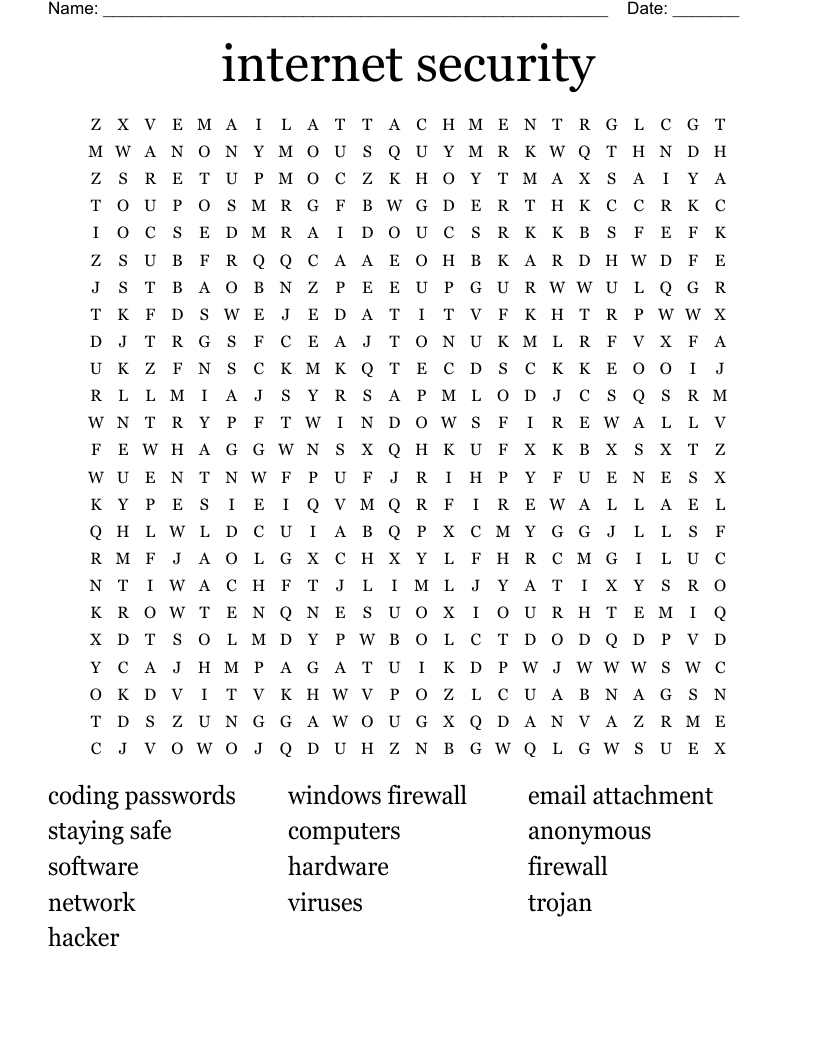
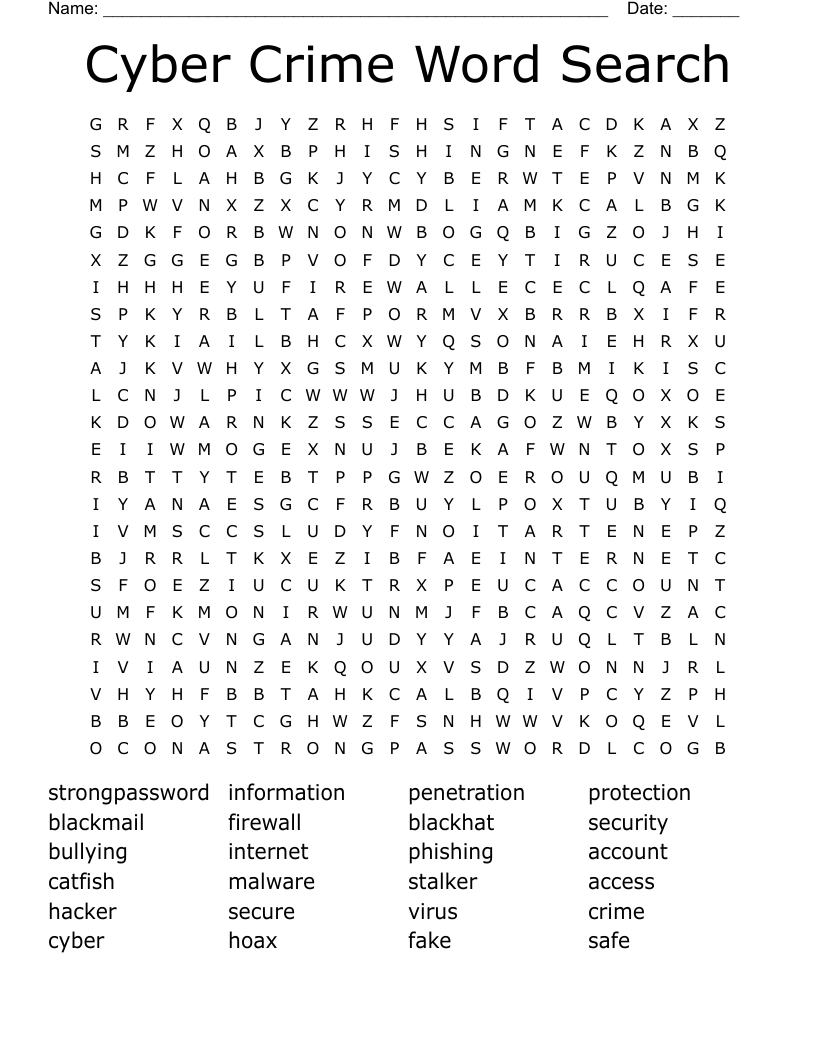
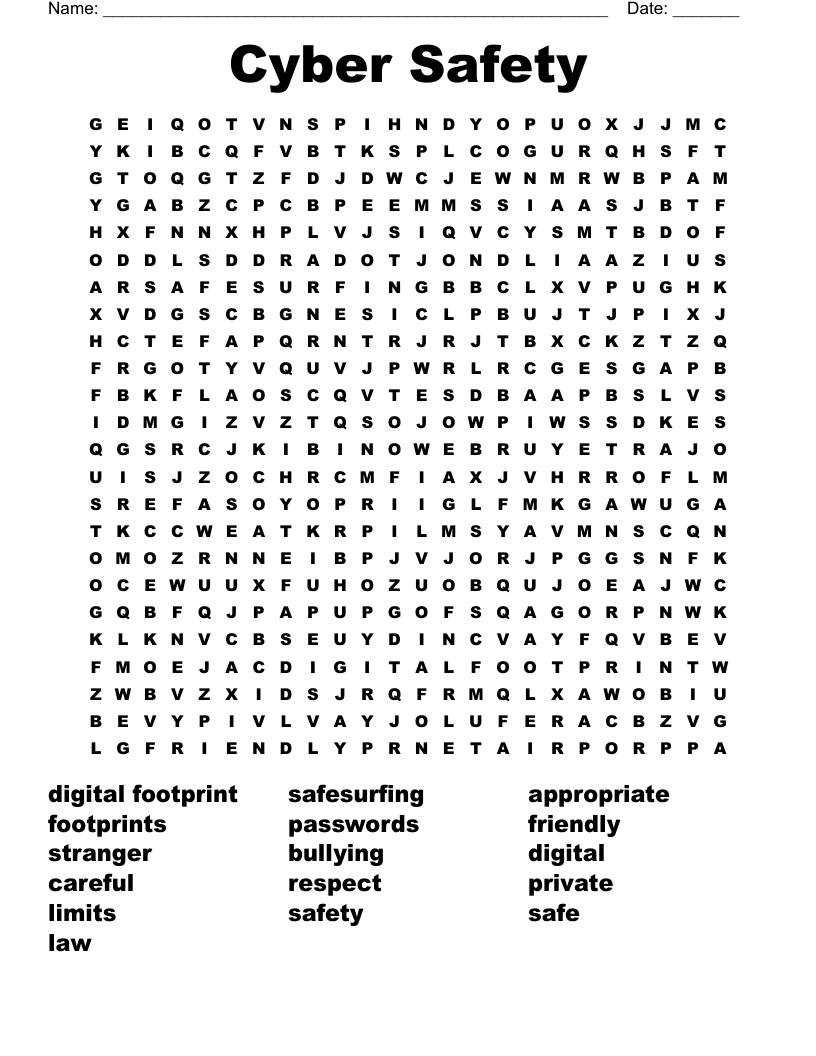
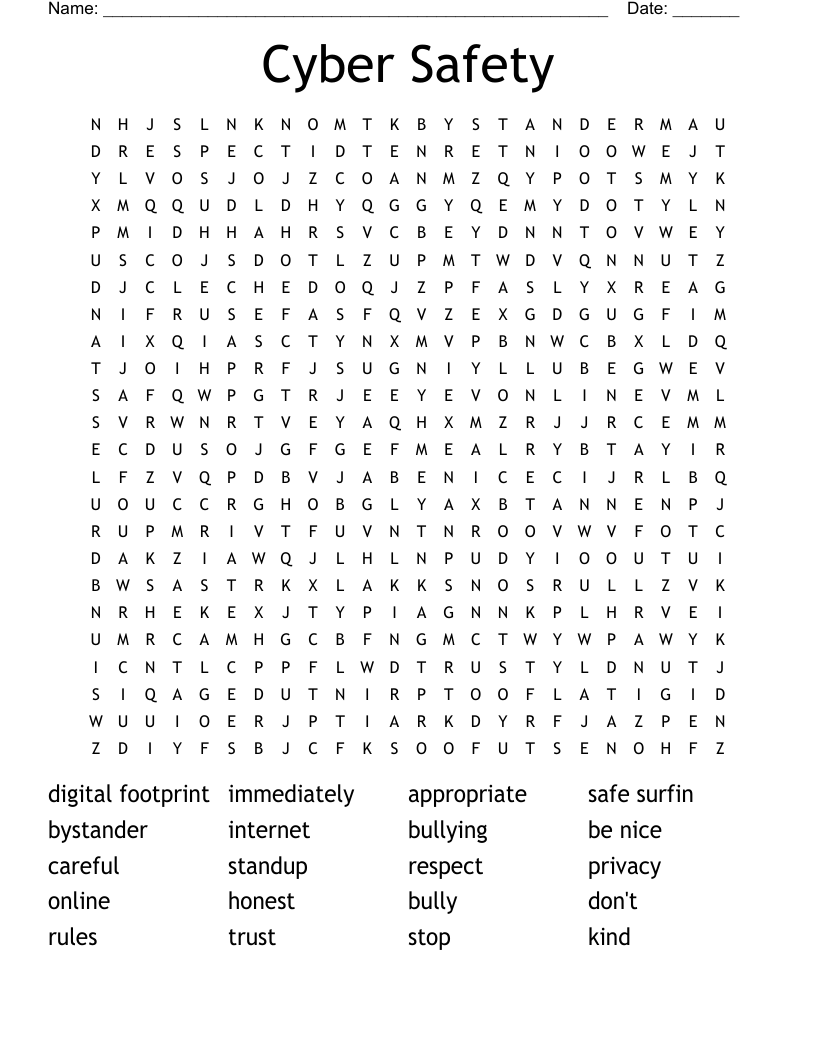
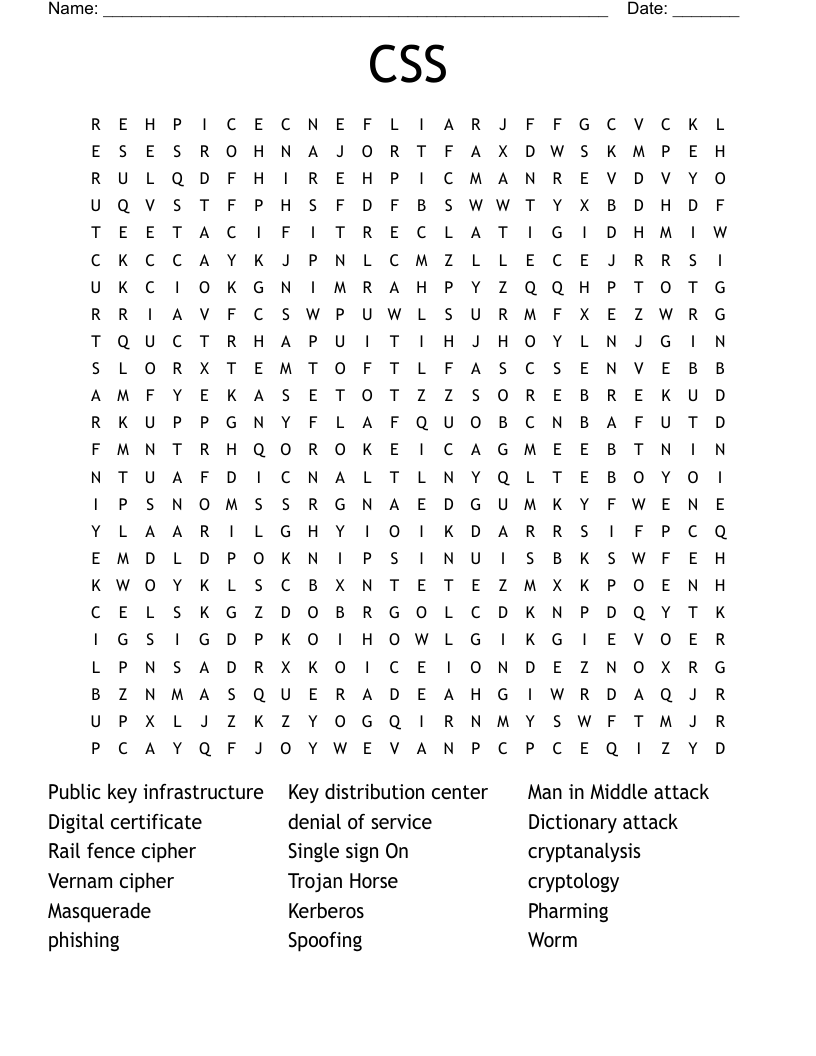
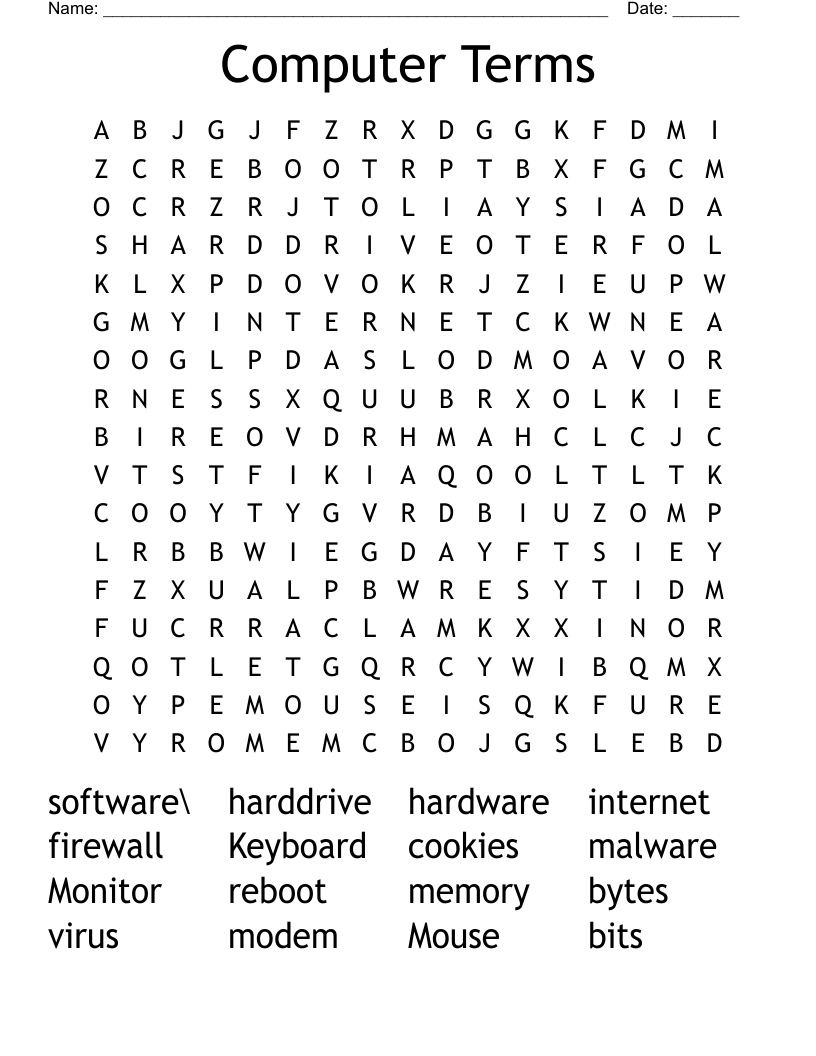
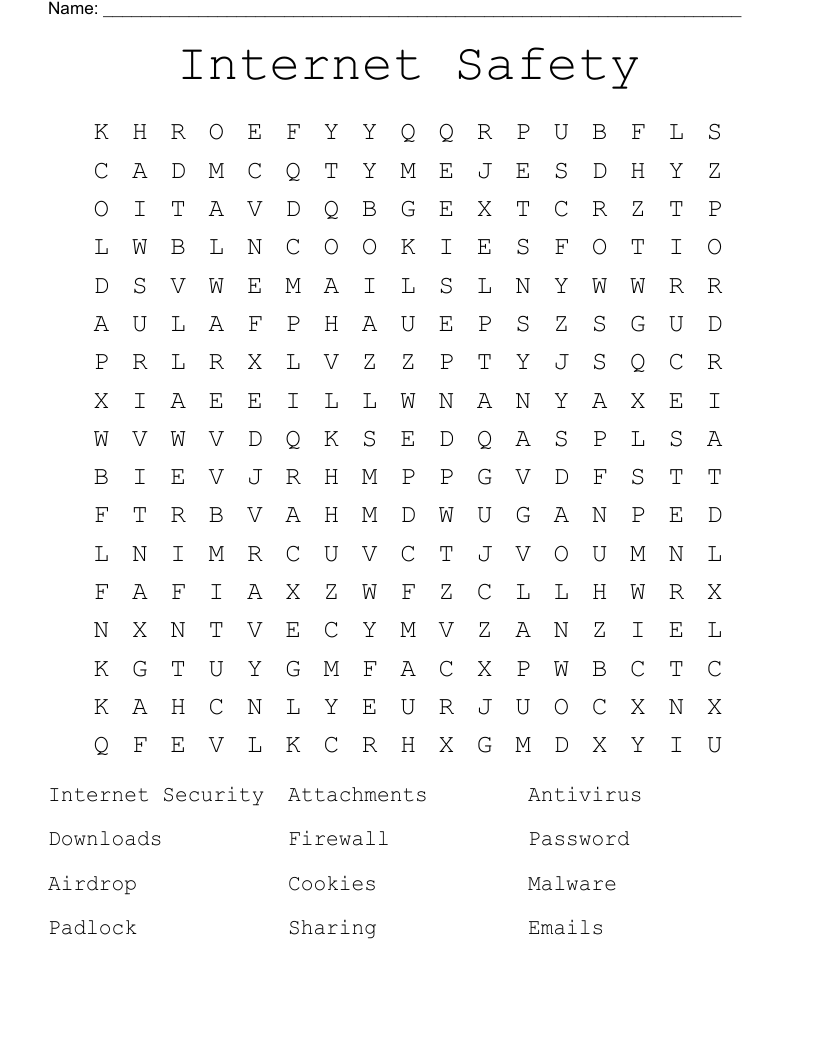
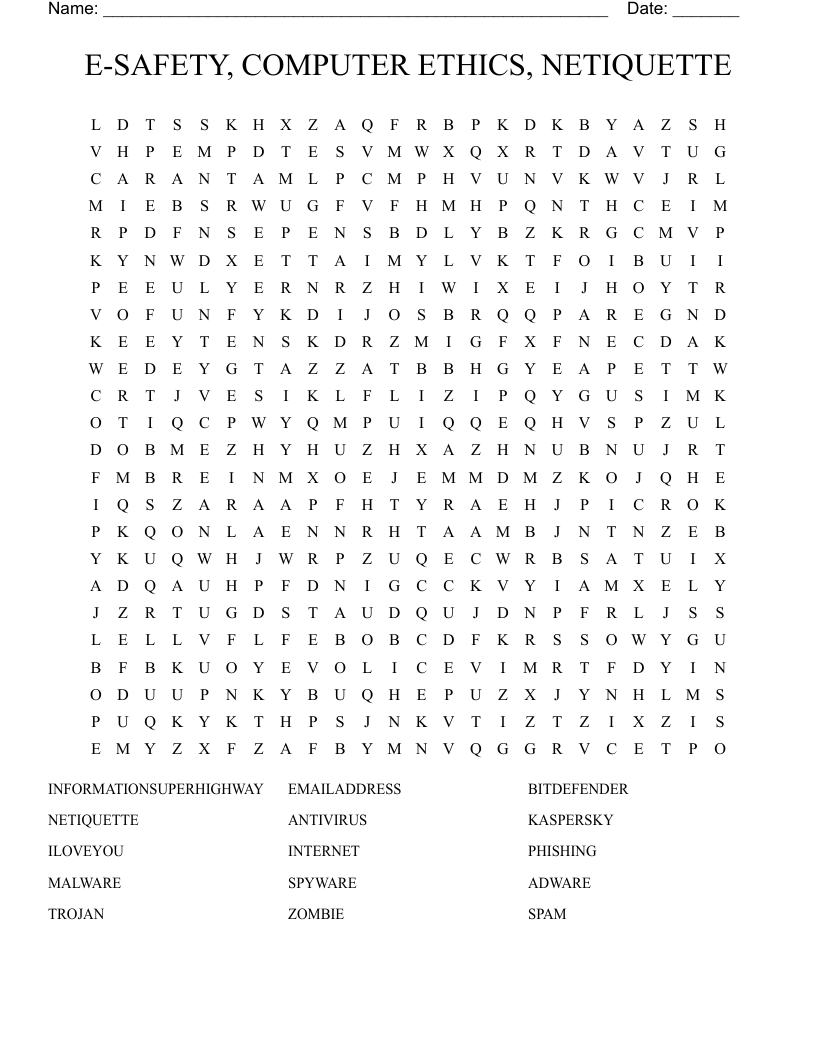
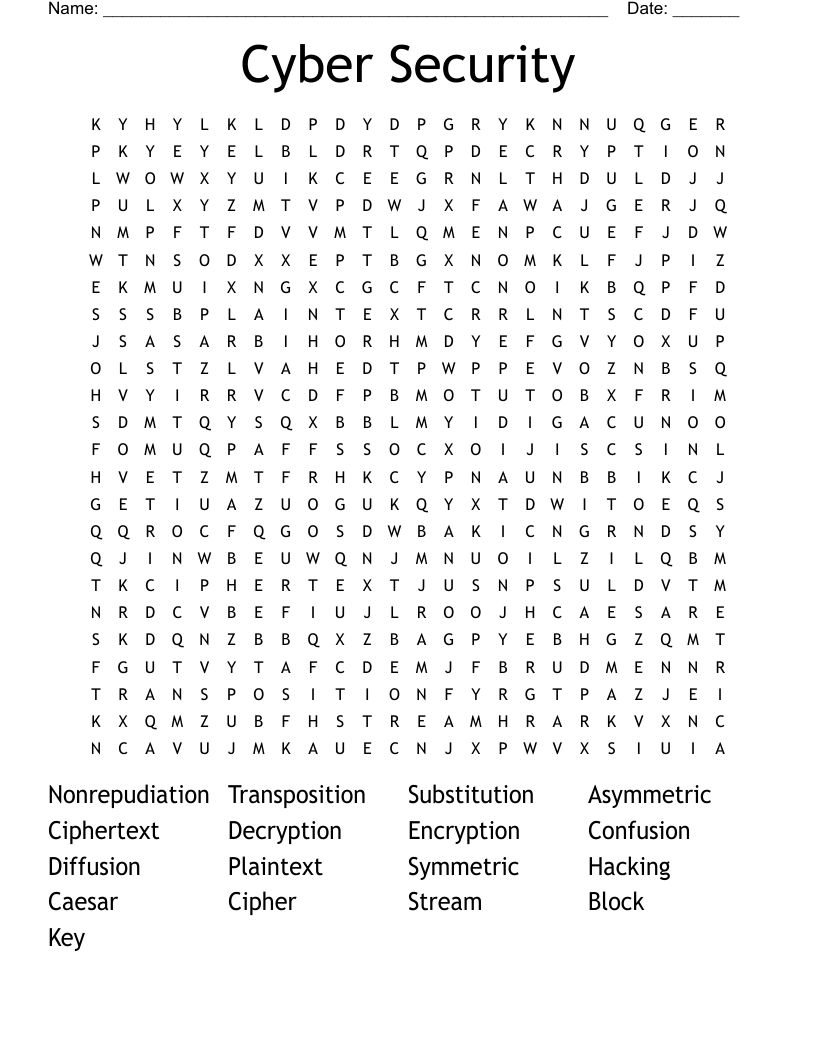
Online and Computer Safety Word Search
This printable word search puzzle contains 25 hidden words in a 24x24 letter grid. Words go horizontally, vertically, backwards, and diagonally. This word search is also available to download as a Microsoft Word document or a PDF.
Description
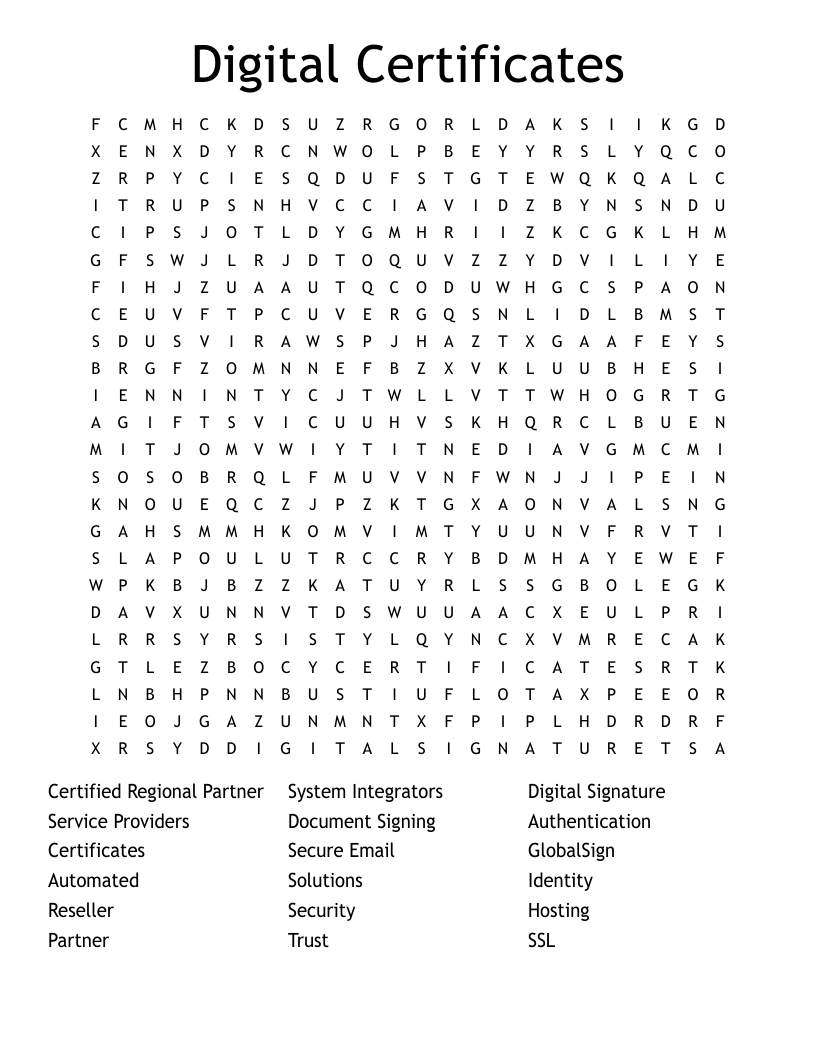
Digital Certificate
Nonrepudiation
Authentication
Illicit Server
Downloading
Encryption
Attachment
Firewall
Software
Internet
Phishing
Password
Cookies
Malware
Spyware
Illegal
Viruses
Browser
Trojan
Hacker
Email
Worms
Spim
Spam
Key
Customize
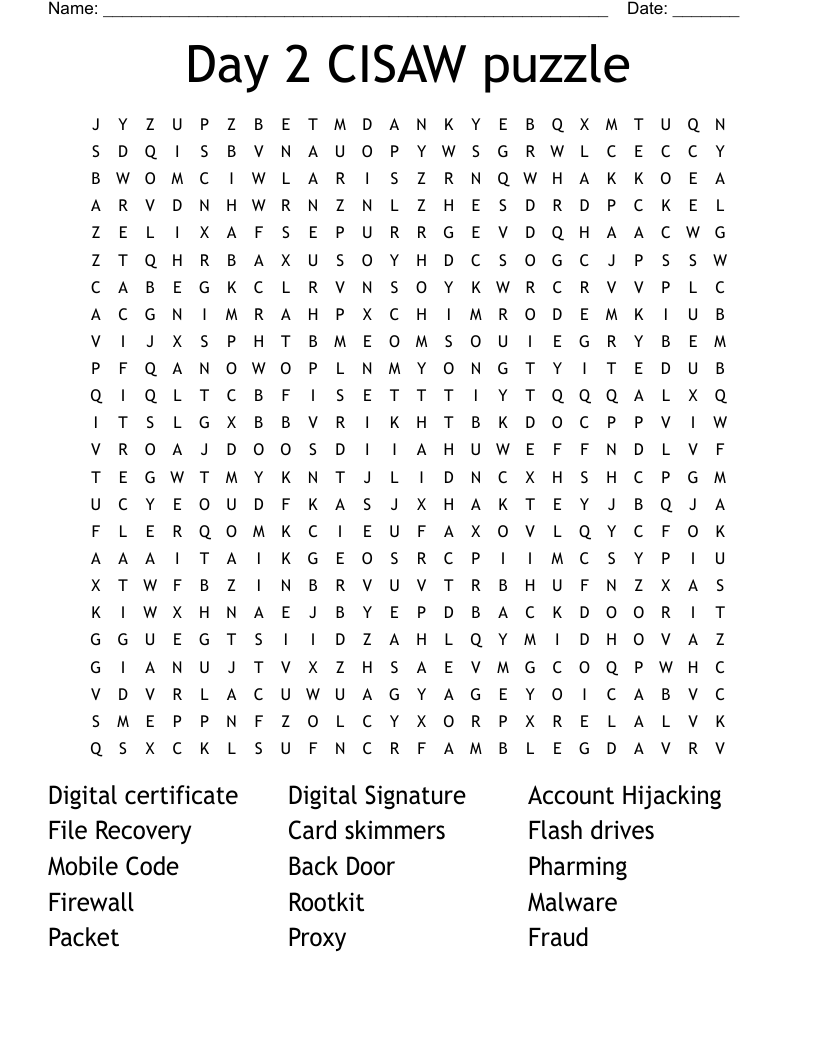
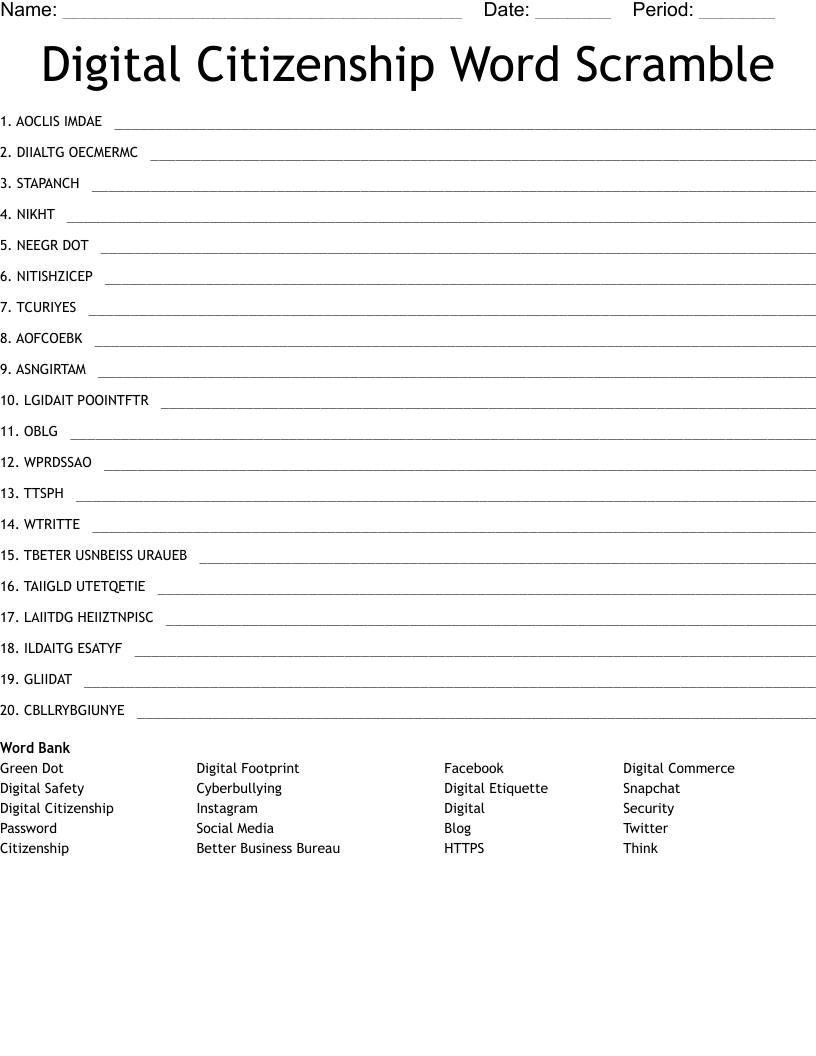
Add, edit, delete clues, and customize this puzzle. Print copies for an entire class.