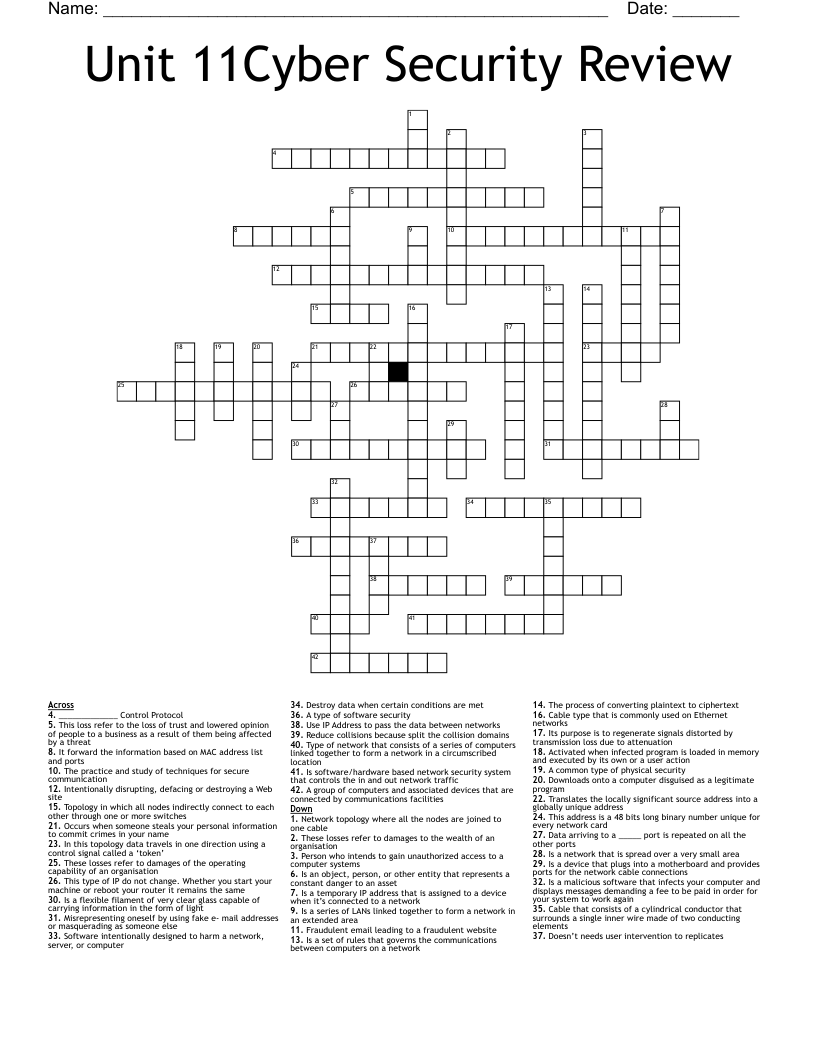
Unit 11Cyber Security Review Crossword
This printable crossword puzzle on the topic of Computer Science & Technology has 42 clues. Answers range from 3 to 14 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
Is an object, person, or other entity that represents a constant danger to an asset
Activated when infected program is loaded in memory and executed by its own or a user action
Doesn’t needs user intervention to replicates
Destroy data when certain conditions are met
Downloads onto a computer disguised as a legitimate program
Software intentionally designed to harm a network, server, or computer
Fraudulent email leading to a fraudulent website
Person who intends to gain unauthorized access to a computer systems
Intentionally disrupting, defacing or destroying a Web site
Misrepresenting oneself by using fake e- mail addresses or masquerading as someone else
Occurs when someone steals your personal information to commit crimes in your name
The process of converting plaintext to ciphertext
The practice and study of techniques for secure communication
Is software/hardware based network security system that controls the in and out network traffic
These losses refer to damages of the operating capability of an organisation
These losses refer to damages to the wealth of an organisation
This loss refer to the loss of trust and lowered opinion of people to a business as a result of them being affected by a threat
A common type of physical security
A type of software security
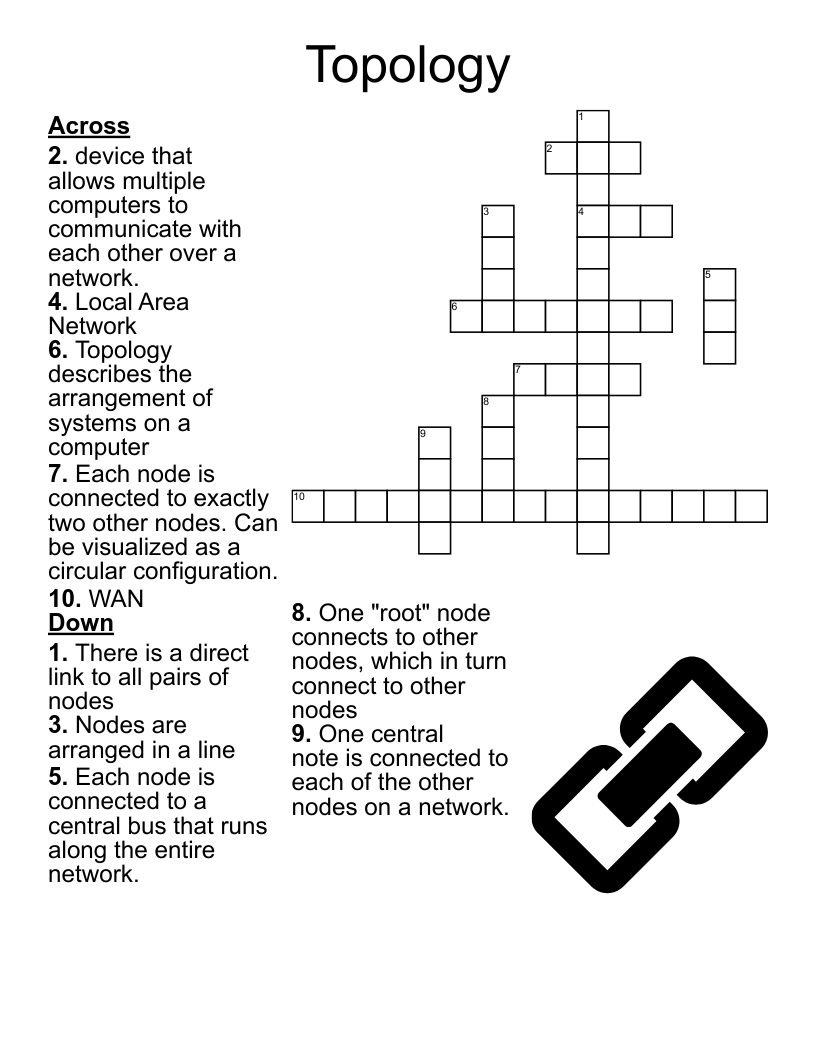
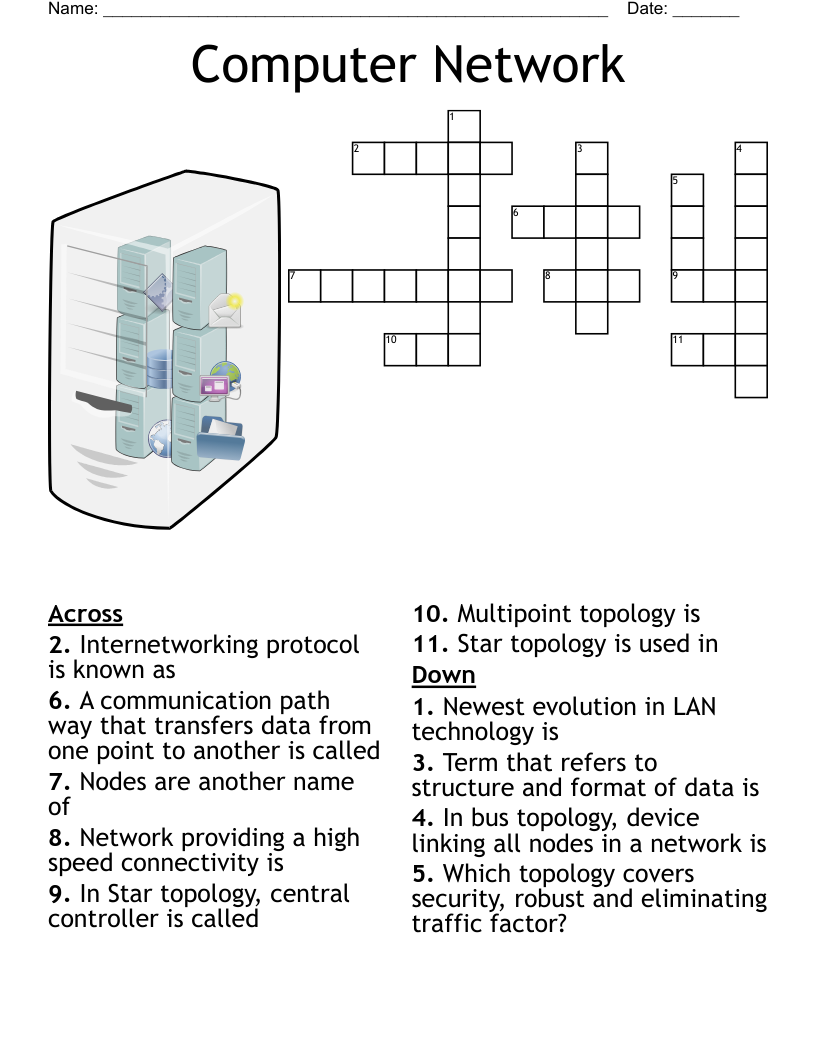
Type of network that consists of a series of computers linked together to form a network in a circumscribed location
Is a series of LANs linked together to form a network in an extended area
In this topology data travels in one direction using a control signal called a ‘token’
Network topology where all the nodes are joined to one cable
Topology in which all nodes indirectly connect to each other through one or more switches
Cable that consists of a cylindrical conductor that surrounds a single inner wire made of two conducting elements
This type of IP do not change. Whether you start your machine or reboot your router it remains the same
Cable type that is commonly used on Ethernet networks
Is a flexible filament of very clear glass capable of carrying information in the form of light
A group of computers and associated devices that are connected by communications facilities
Is a network that is spread over a very small area
Is a device that plugs into a motherboard and provides ports for the network cable connections
This address is a 48 bits long binary number unique for every network card
Its purpose is to regenerate signals distorted by transmission loss due to attenuation
Data arriving to a _____ port is repeated on all the other ports
Reduce collisions because split the collision domains
It forward the information based on MAC address list and ports
Use IP Address to pass the data between networks
Is a set of rules that governs the communications between computers on a network
_____________ Control Protocol
Is a temporary IP address that is assigned to a device when it’s connected to a network
Translates the locally significant source address into a globally unique address
Is a malicious software that infects your computer and displays messages demanding a fee to be paid in order for your system to work again