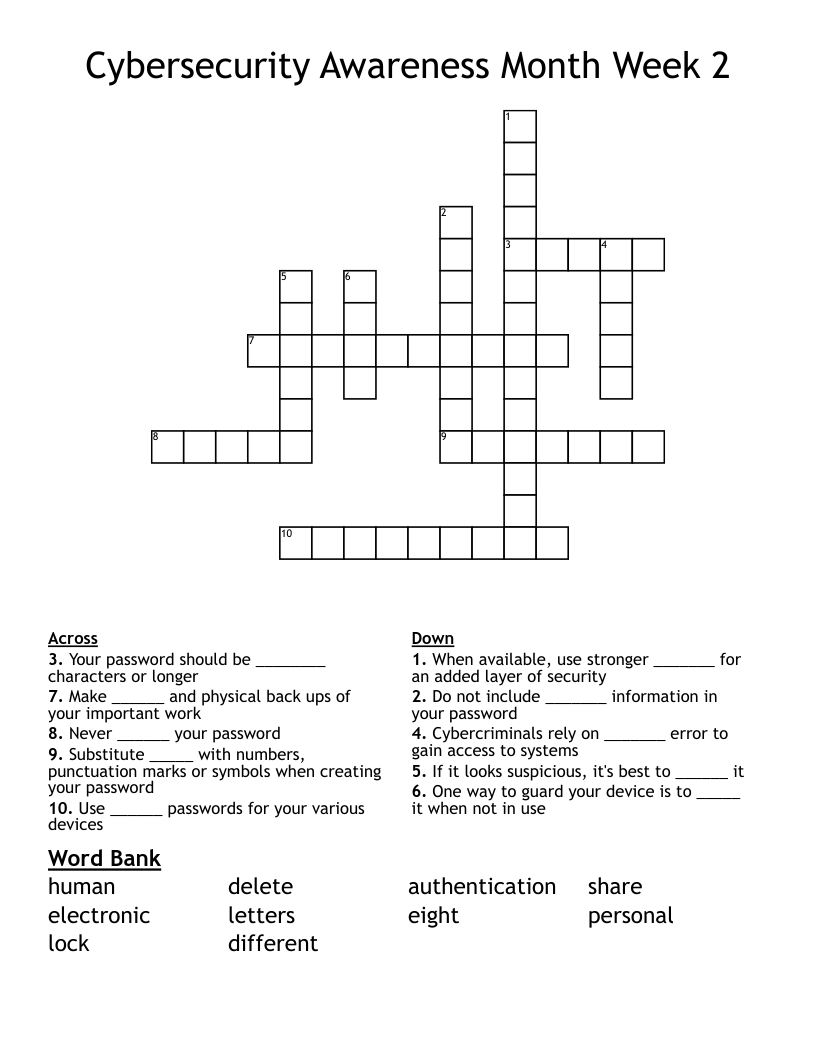
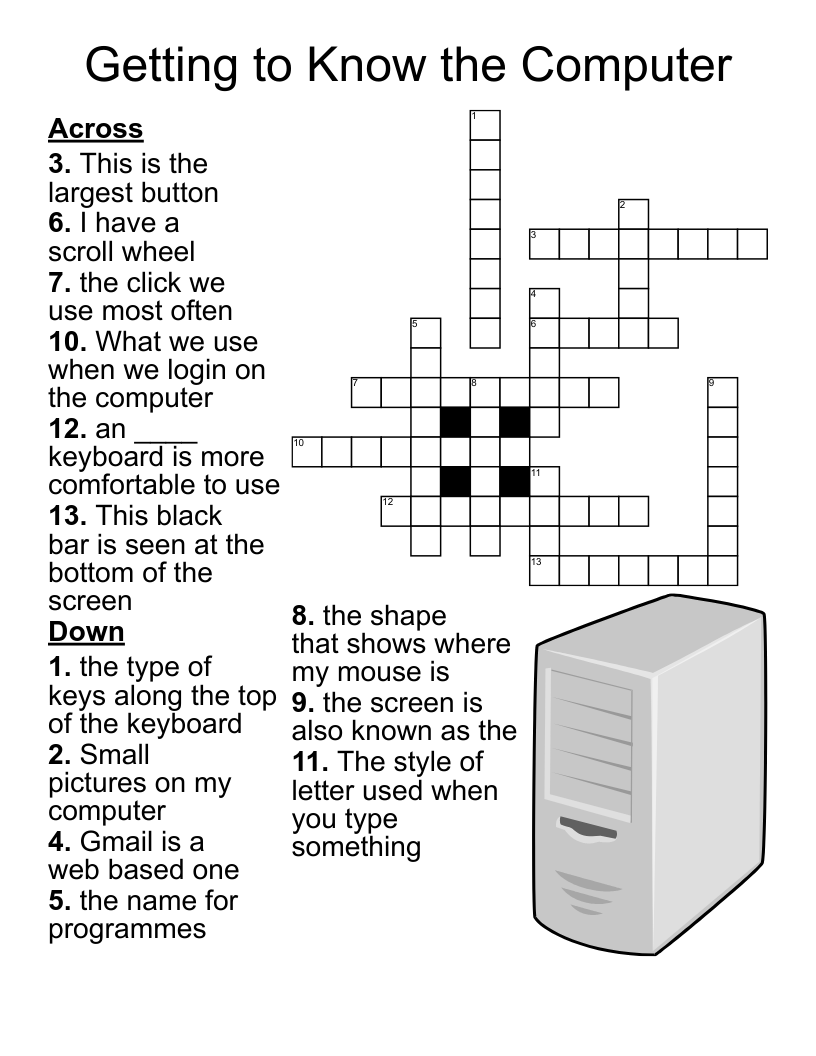
Cybersecurity Awareness Month Week 2 Crossword
This printable crossword puzzle on the topic of Computer Science & Technology has 10 clues. Answers range from 4 to 14 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
Cybercriminals rely on _______ error to gain access to systems
Your password should be ________ characters or longer
If it looks suspicious, it's best to ______ it
Do not include _______ information in your password
One way to guard your device is to _____ it when not in use
Never ______ your password
Use ______ passwords for your various devices
When available, use stronger _______ for an added layer of security
Substitute _____ with numbers, punctuation marks or symbols when creating your password
Make ______ and physical back ups of your important work