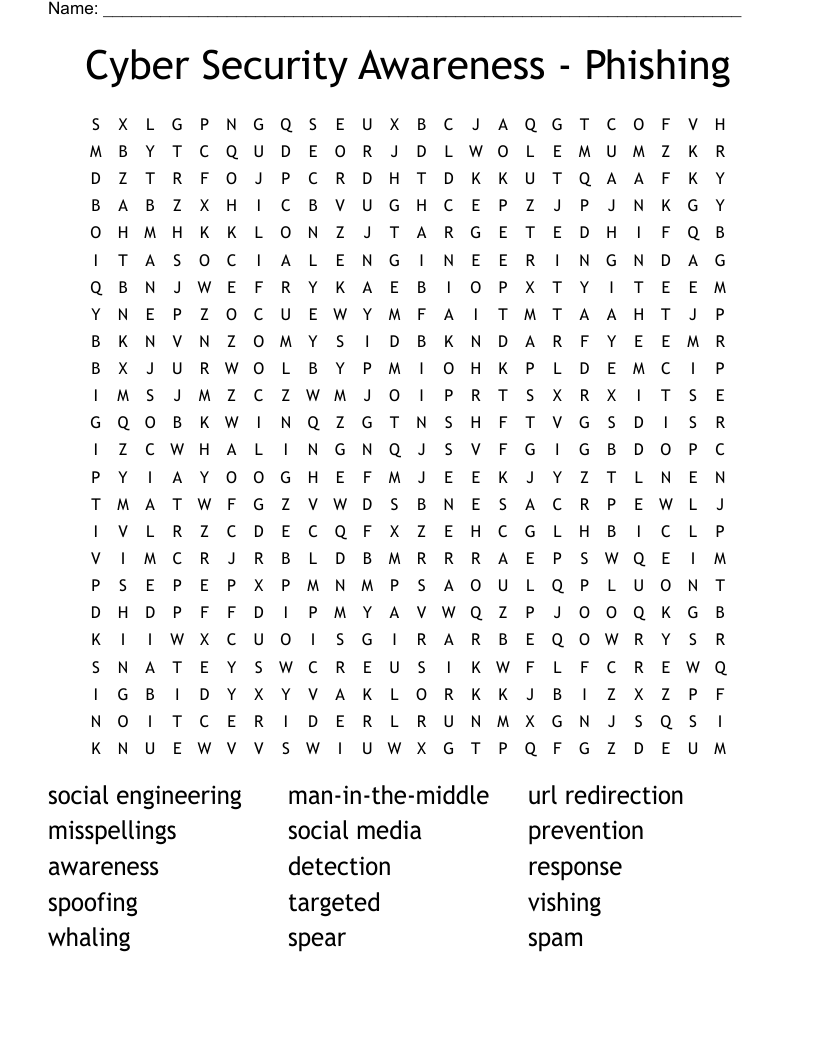
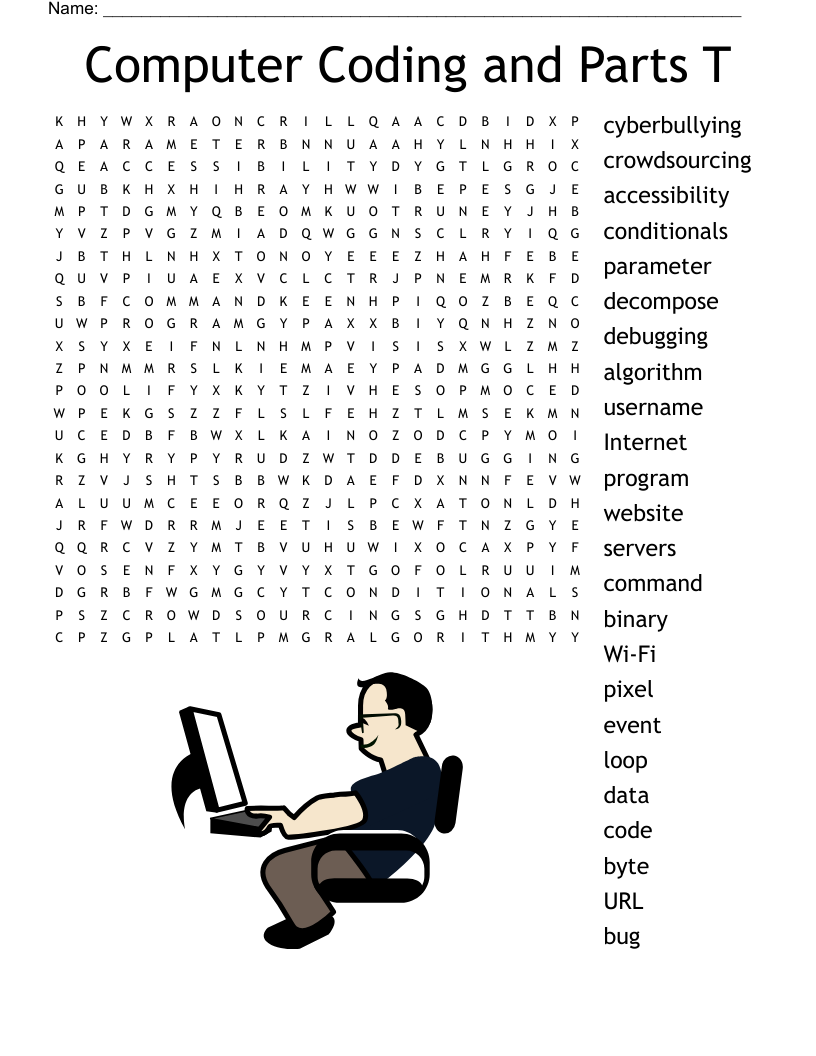
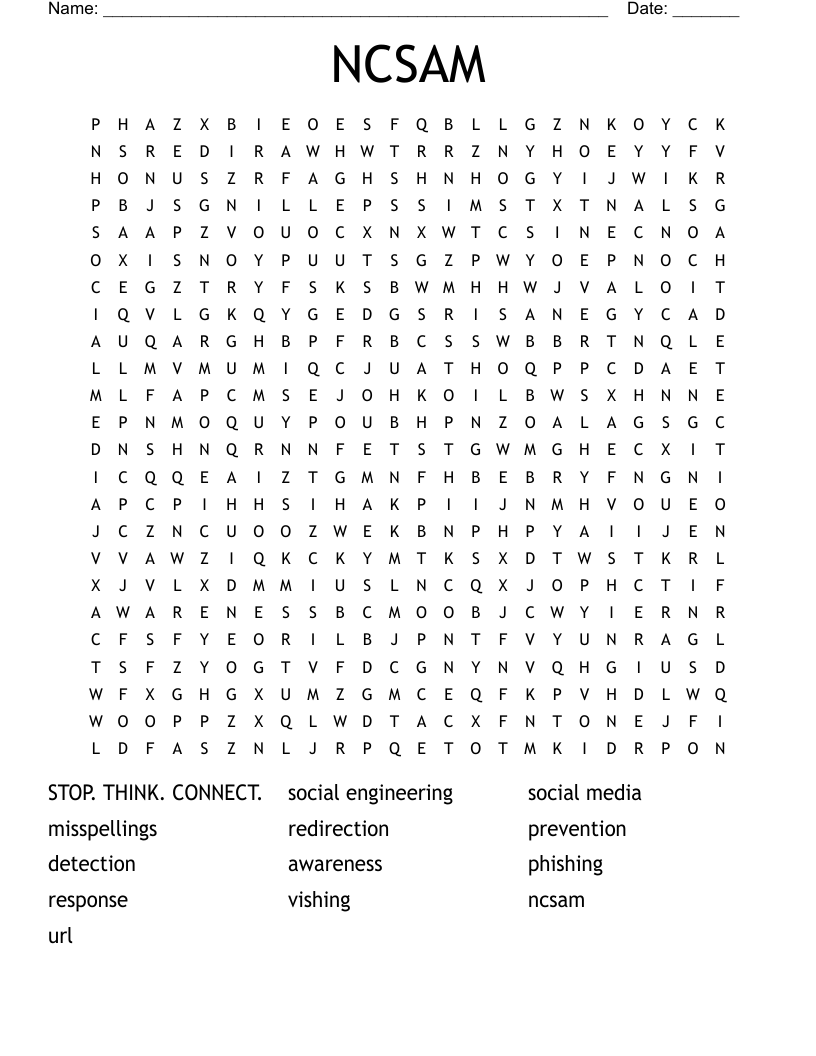
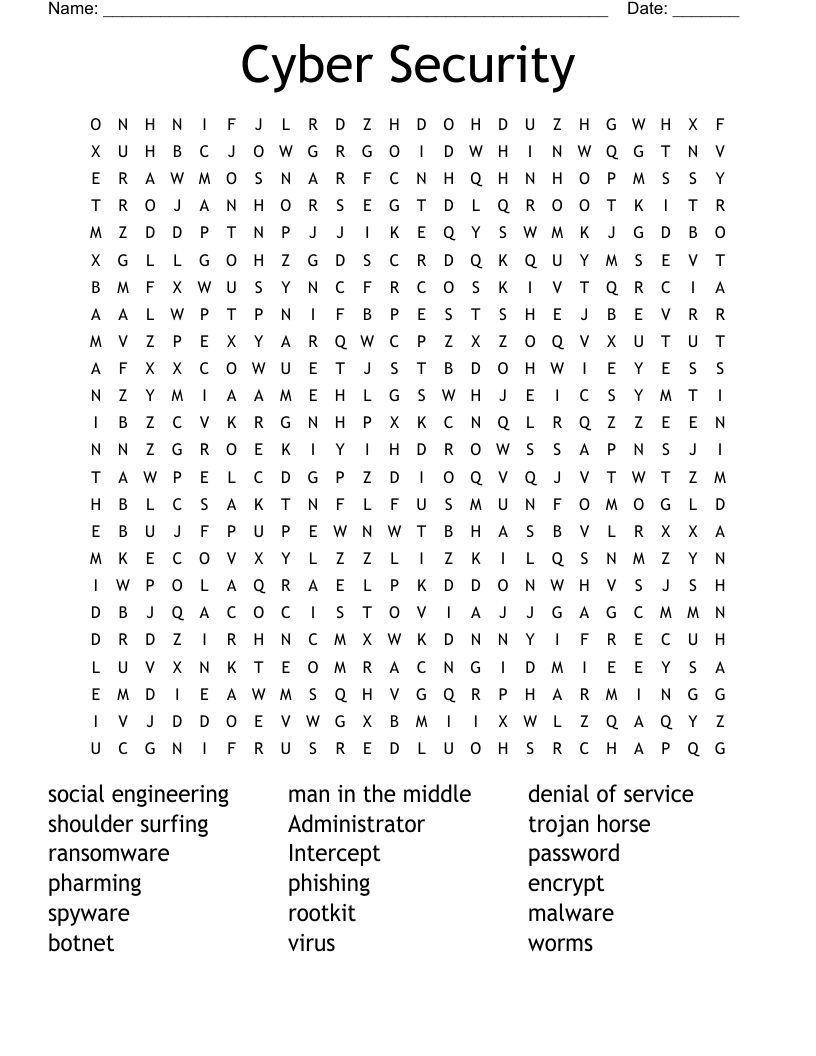
Cyber Security Awareness - Phishing Word Search
This printable word search puzzle on the topic of Computer Science & Technology contains 15 hidden words in a 24x24 letter grid. Words go horizontally, vertically, backwards, and diagonally. This word search is also available to download as a Microsoft Word document or a PDF.
Description
social engineering
man-in-the-middle
url redirection
misspellings
social media
prevention
awareness
detection
response
spoofing
targeted
vishing
whaling
spear
spam
Customize
Add, edit, delete clues, and customize this puzzle. Print copies for an entire class.