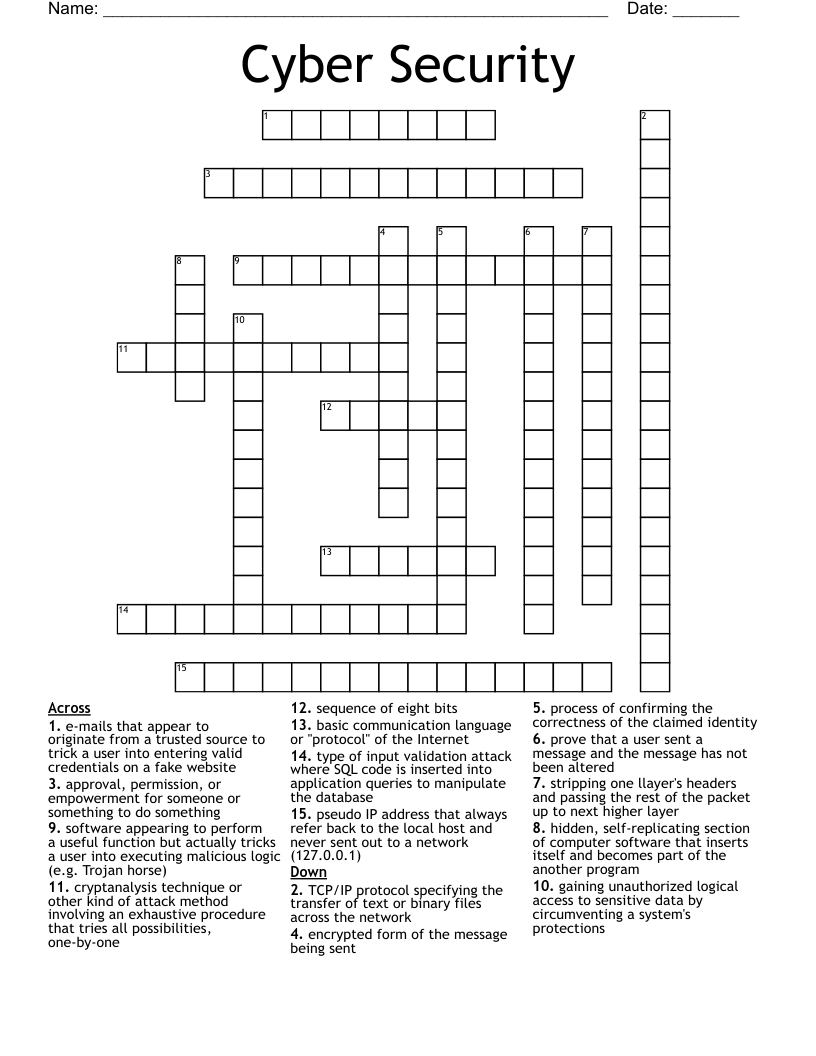
Cyber Security Crossword
This printable crossword puzzle on the topic of Computer Science & Technology has 15 clues. Answers range from 5 to 20 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
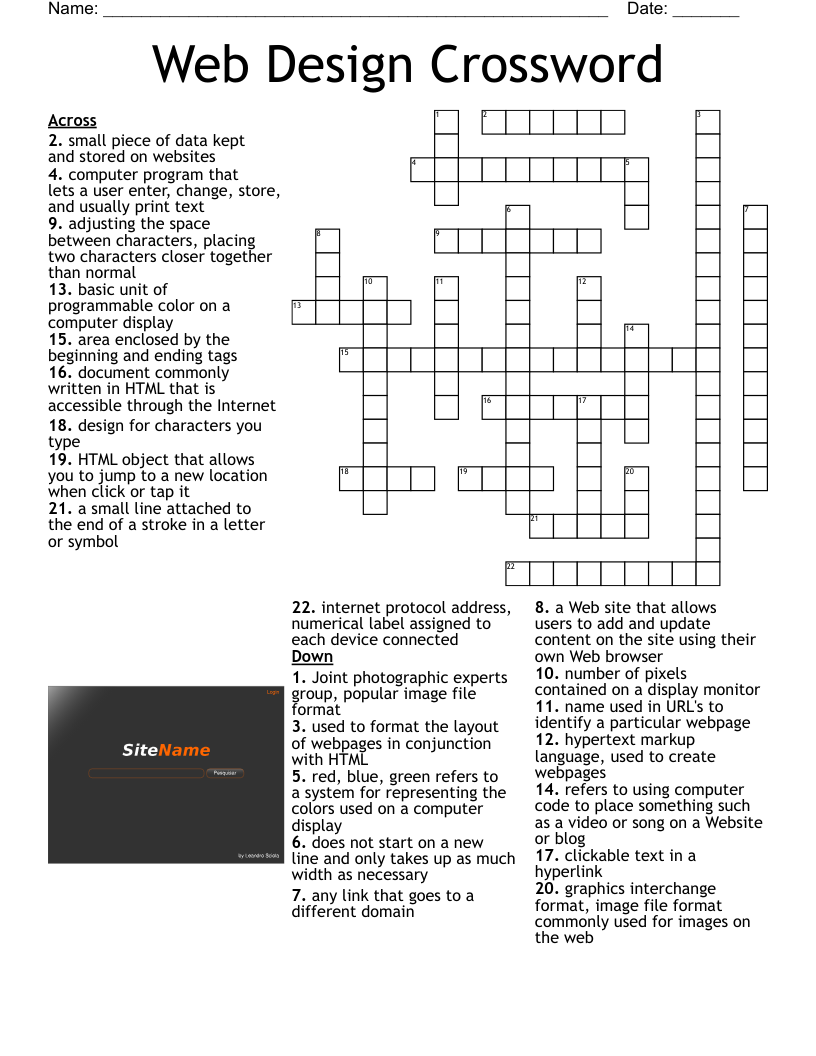
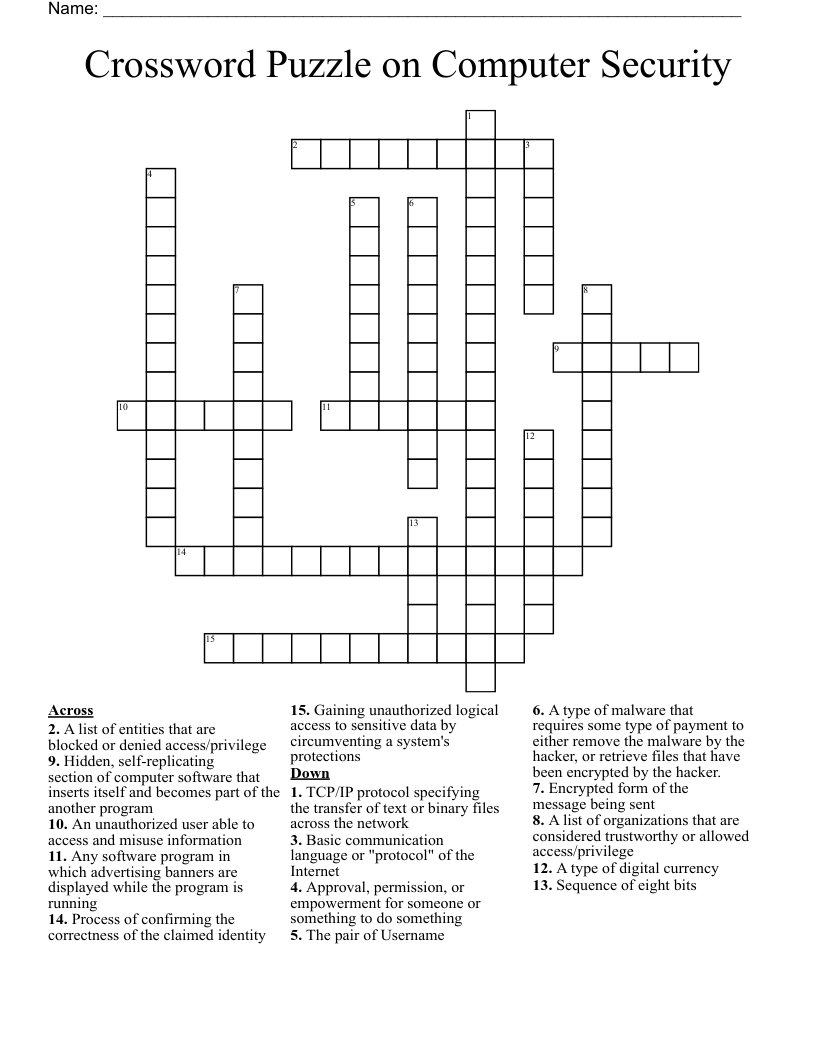
process of confirming the correctness of the claimed identity
approval, permission, or empowerment for someone or something to do something
cryptanalysis technique or other kind of attack method involving an exhaustive procedure that tries all possibilities, one-by-one
encrypted form of the message being sent
stripping one llayer's headers and passing the rest of the packet up to next higher layer
TCP/IP protocol specifying the transfer of text or binary files across the network
pseudo IP address that always refer back to the local host and never sent out to a network (127.0.0.1)
software appearing to perform a useful function but actually tricks a user into executing malicious logic (e.g. Trojan horse)
prove that a user sent a message and the message has not been altered
sequence of eight bits
e-mails that appear to originate from a trusted source to trick a user into entering valid credentials on a fake website
gaining unauthorized logical access to sensitive data by circumventing a system's protections
type of input validation attack where SQL code is inserted into application queries to manipulate the database
basic communication language or "protocol" of the Internet
hidden, self-replicating section of computer software that inserts itself and becomes part of the another program