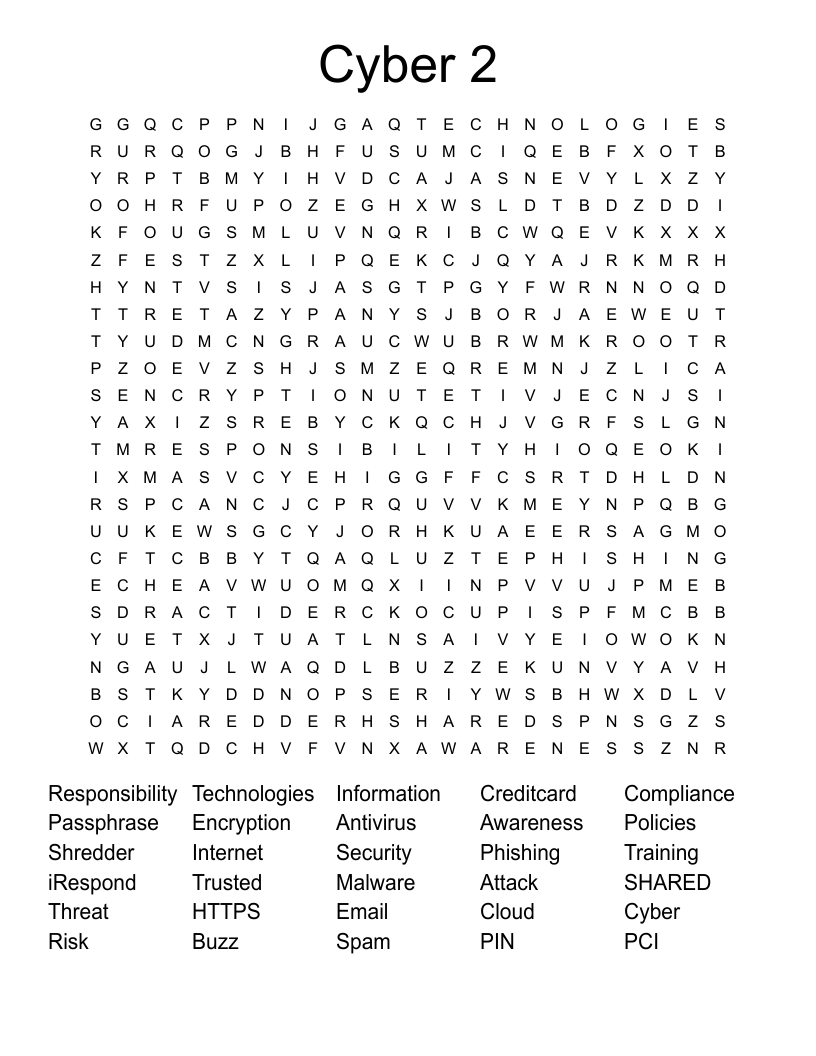
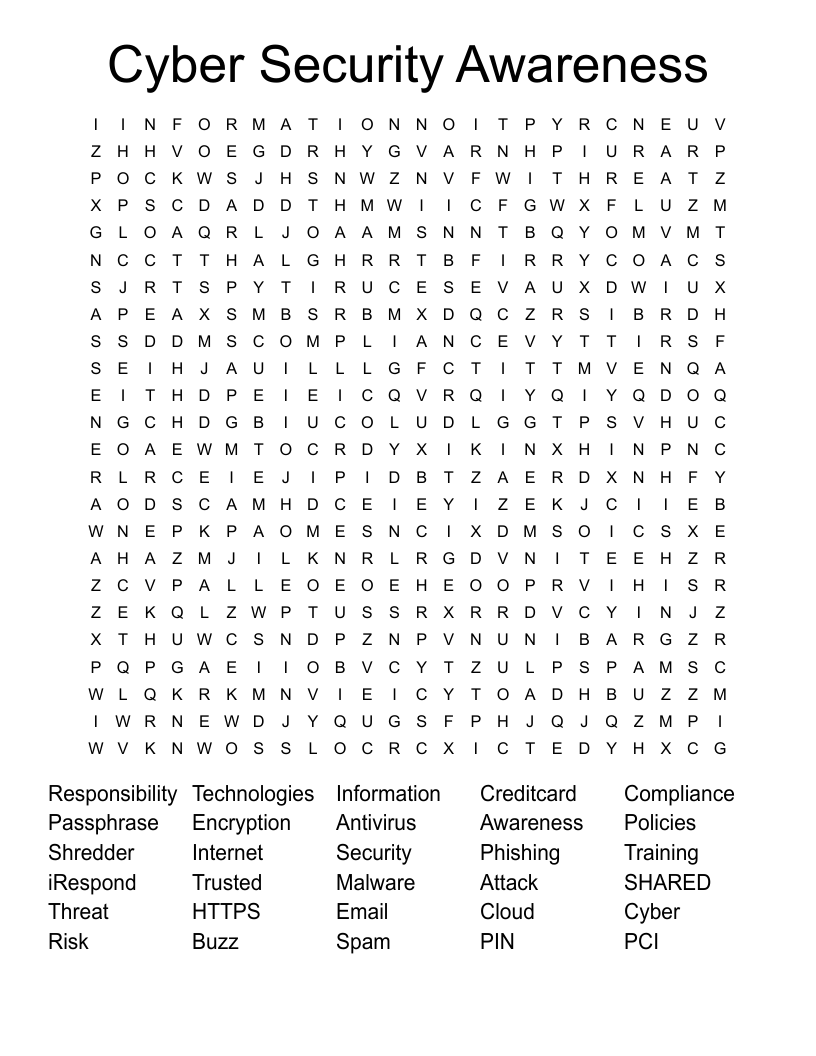
Cyber 2 Word Search
This printable word search puzzle on the topic of Computer Science & Technology contains 30 hidden words in a 24x24 letter grid. Words go horizontally, vertically, backwards, and diagonally. This word search is also available to download as a Microsoft Word document or a PDF.
Description
Responsibility
Technologies
Information
Creditcard
Compliance
Passphrase
Encryption
Antivirus
Awareness
Policies
Shredder
Internet
Security
Phishing
Training
iRespond
Trusted
Malware
Attack
SHARED
Threat
HTTPS
Email
Cloud
Cyber
Risk
Buzz
Spam
PIN
PCI
Customize
Add, edit, delete clues, and customize this puzzle. Print copies for an entire class.