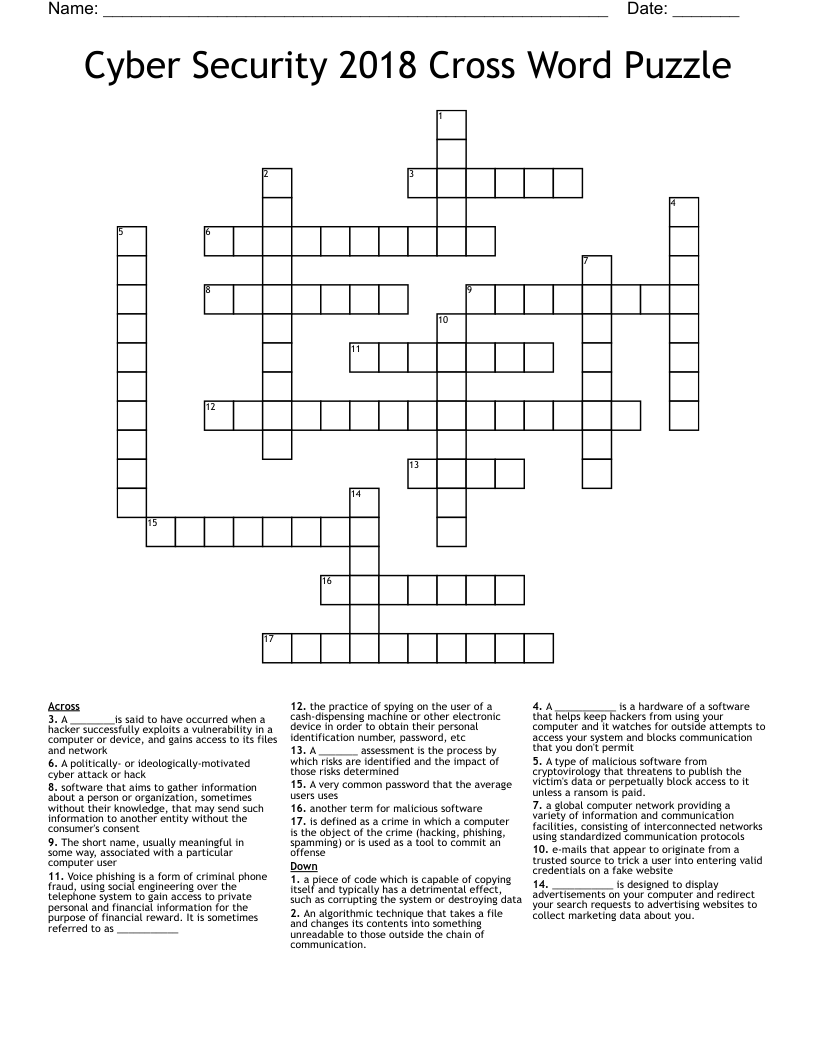
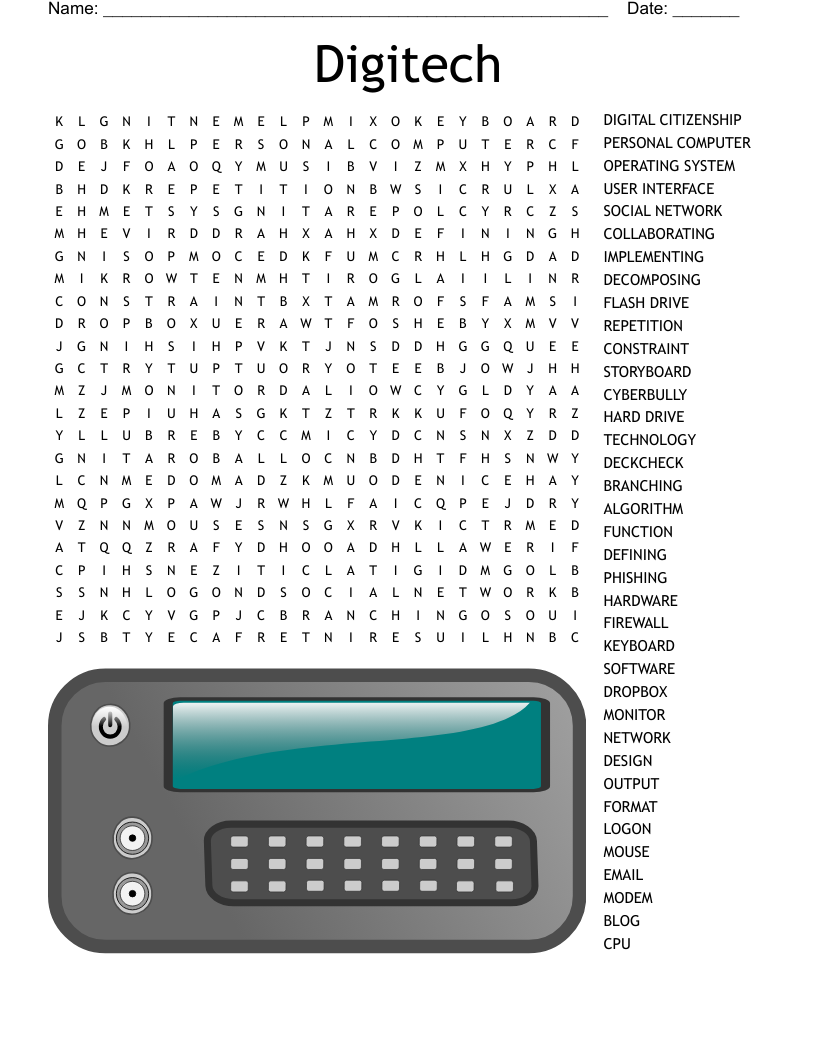
Cyber Security 2018 Cross Word Puzzle
This printable crossword puzzle on the topic of Computer Science & Technology has 17 clues. Answers range from 4 to 15 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
e-mails that appear to originate from a trusted source to trick a user into entering valid credentials on a fake website
A _______ assessment is the process by which risks are identified and the impact of those risks determined
Voice phishing is a form of criminal phone fraud, using social engineering over the telephone system to gain access to private personal and financial information for the purpose of financial reward. It is sometimes referred to as ___________
A type of malicious software from cryptovirology that threatens to publish the victim's data or perpetually block access to it unless a ransom is paid.
A ___________ is a hardware of a software that helps keep hackers from using your computer and it watches for outside attempts to access your system and blocks communication that you don't permit
the practice of spying on the user of a cash-dispensing machine or other electronic device in order to obtain their personal identification number, password, etc
a piece of code which is capable of copying itself and typically has a detrimental effect, such as corrupting the system or destroying data
A very common password that the average users uses
a global computer network providing a variety of information and communication facilities, consisting of interconnected networks using standardized communication protocols
is defined as a crime in which a computer is the object of the crime (hacking, phishing, spamming) or is used as a tool to commit an offense
software that aims to gather information about a person or organization, sometimes without their knowledge, that may send such information to another entity without the consumer's consent
A ________is said to have occurred when a hacker successfully exploits a vulnerability in a computer or device, and gains access to its files and network
The short name, usually meaningful in some way, associated with a particular computer user
An algorithmic technique that takes a file and changes its contents into something unreadable to those outside the chain of communication.
another term for malicious software
___________ is designed to display advertisements on your computer and redirect your search requests to advertising websites to collect marketing data about you.
A politically- or ideologically-motivated cyber attack or hack