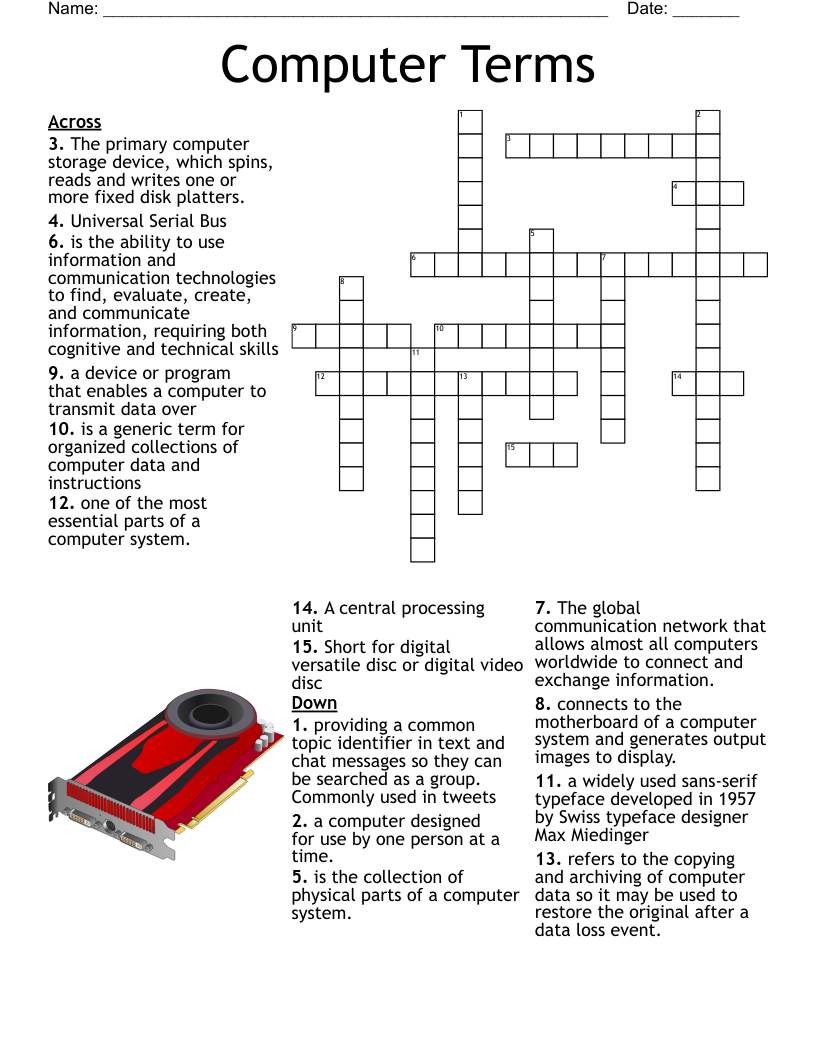
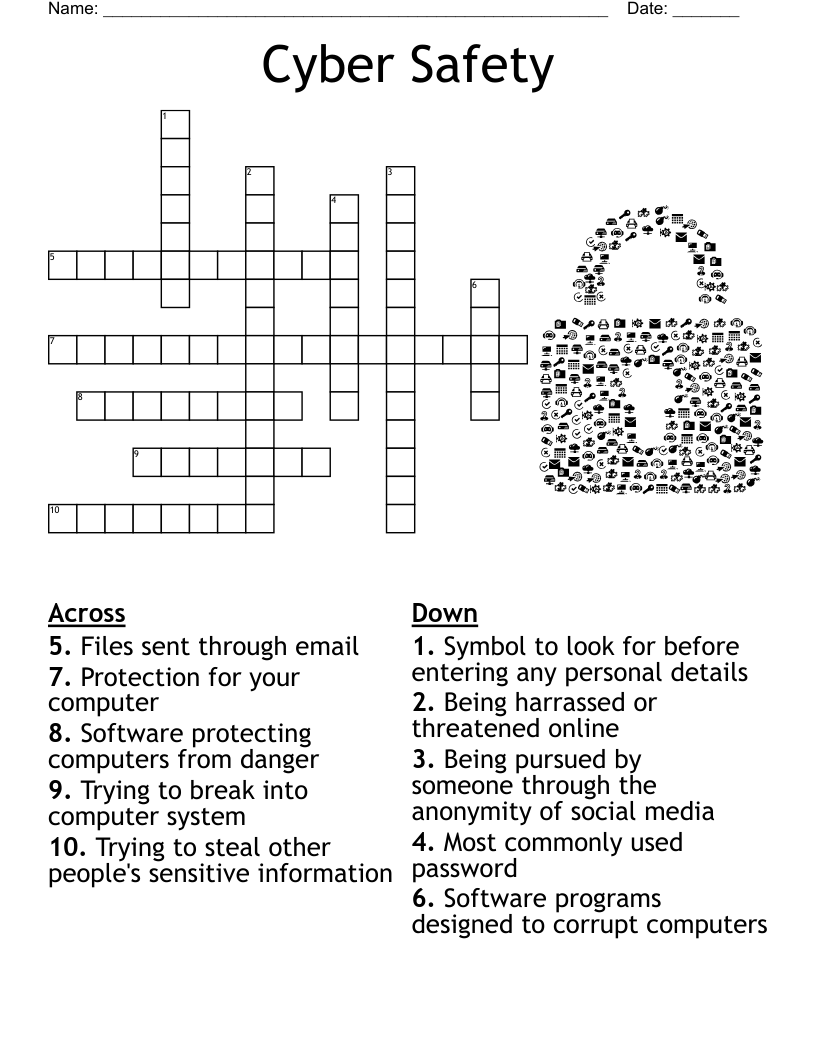
Internet Safety Crossword
This printable crossword puzzle on the topic of Computer Science & Technology has 15 clues. Answers range from 4 to 20 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
controlled by or connected to another computer or network
working surface of a desk
legal right given to an originator to print, publish, perform, film, or record the originator's work.
any message passed through digital devices.
where computer networkers where users can communicate.
regularly updated website or web page, typically one run by an individual or small group
capable of copying itself and destroying data.
electronic communication used to bully a person or a group of people.
applications that enable users to create and share content or to participate in social networking.
set of rules you should follow in order to make the internet better for others, and better for you.
acquisition and use of a person's private identifying information
A hostile, strongly worded message that may contain obscene language.
specific features or software that parents manage the online activities of children
any device used to communicate provocative messages and/or sexual images
A program, or set of instructions, that runs on a computer.