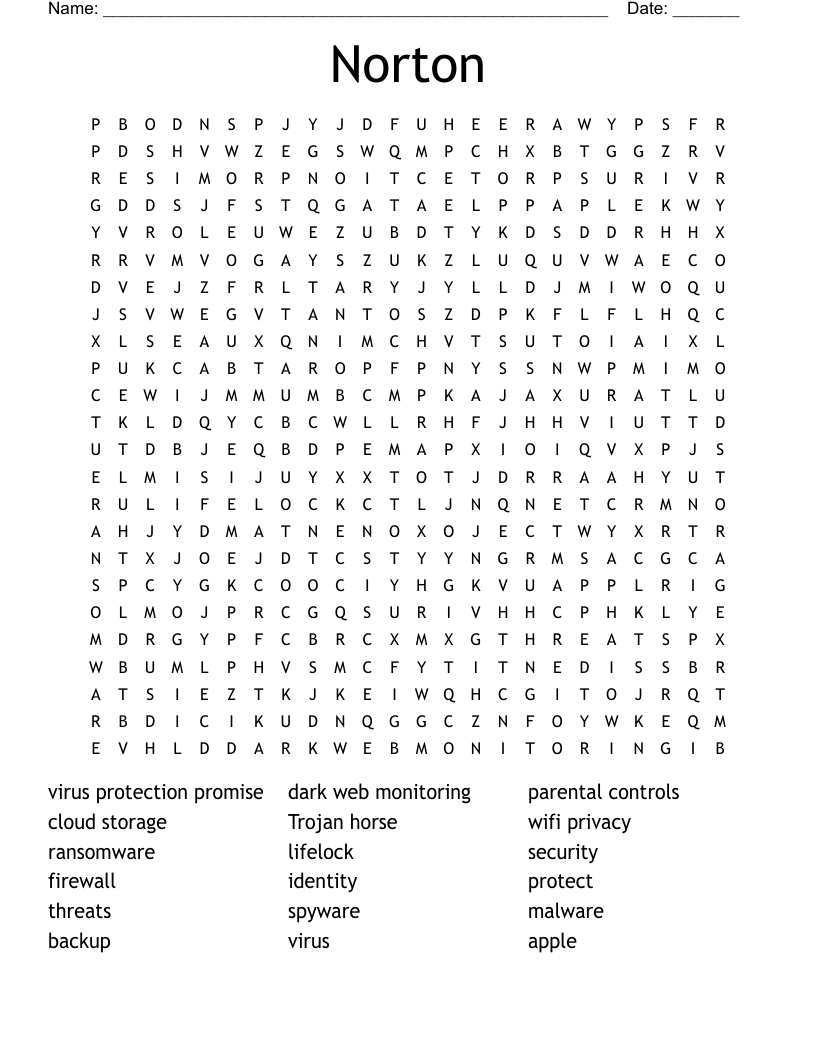
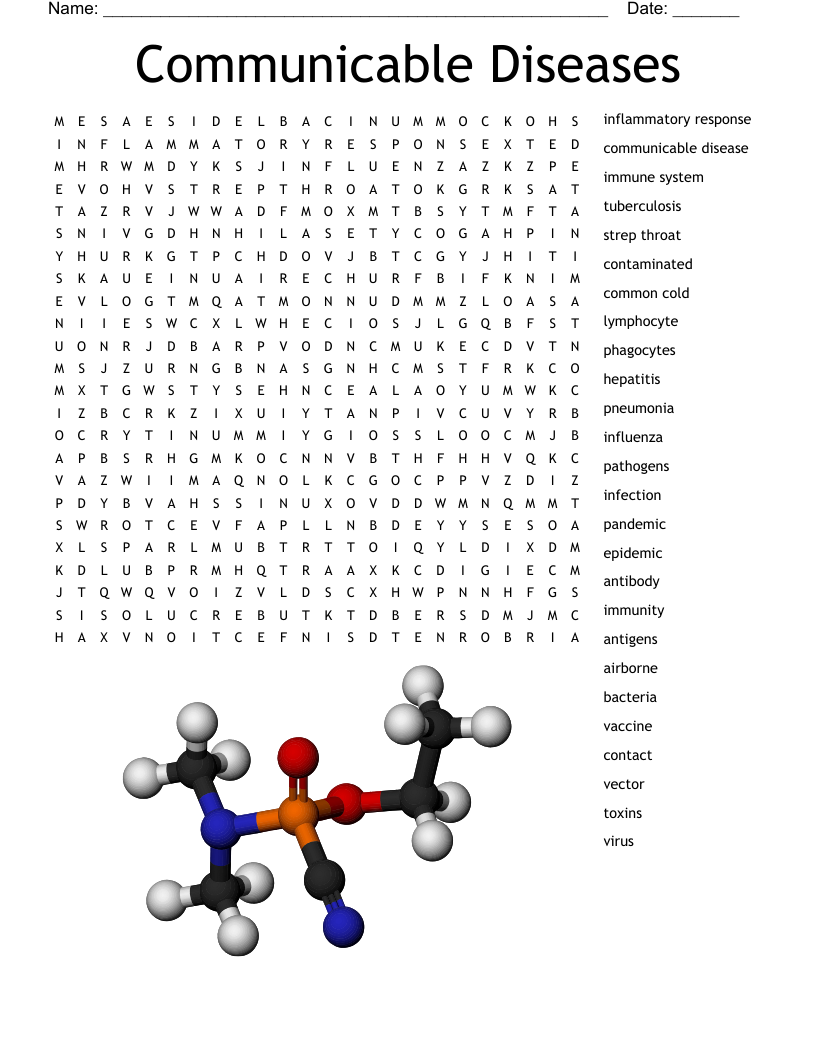
Norton Word Search
This printable word search puzzle contains 18 hidden words in a 24x24 letter grid. Words go horizontally, vertically, backwards, and diagonally. This word search is also available to download as a Microsoft Word document or a PDF.
Description
virus protection promise
dark web monitoring
parental controls
cloud storage
Trojan horse
wifi privacy
ransomware
lifelock
security
firewall
identity
protect
threats
spyware
malware
backup
virus
apple
Customize
Add, edit, delete clues, and customize this puzzle. Print copies for an entire class.