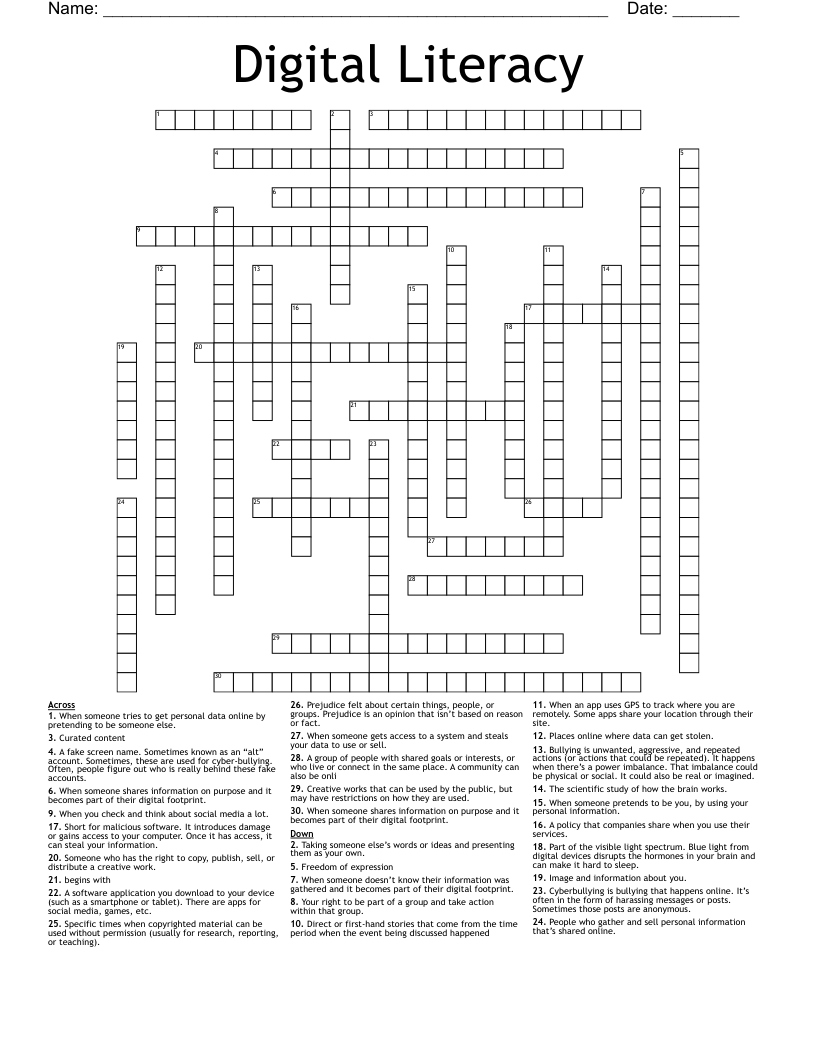
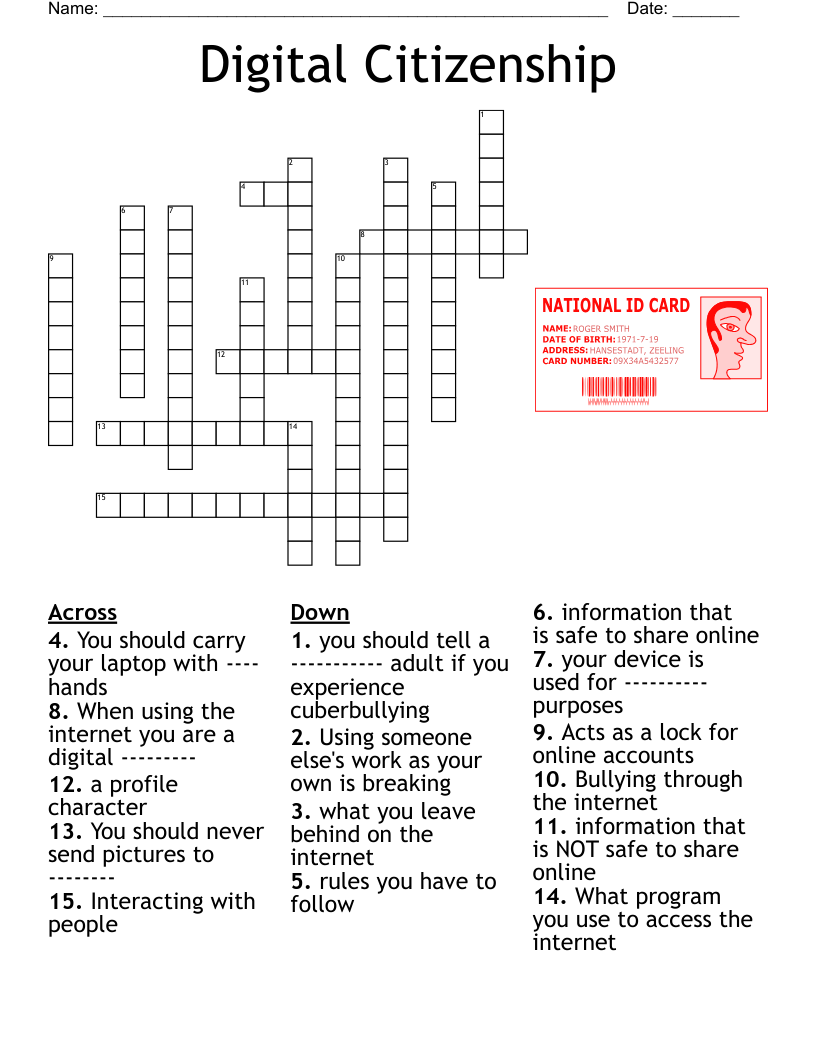
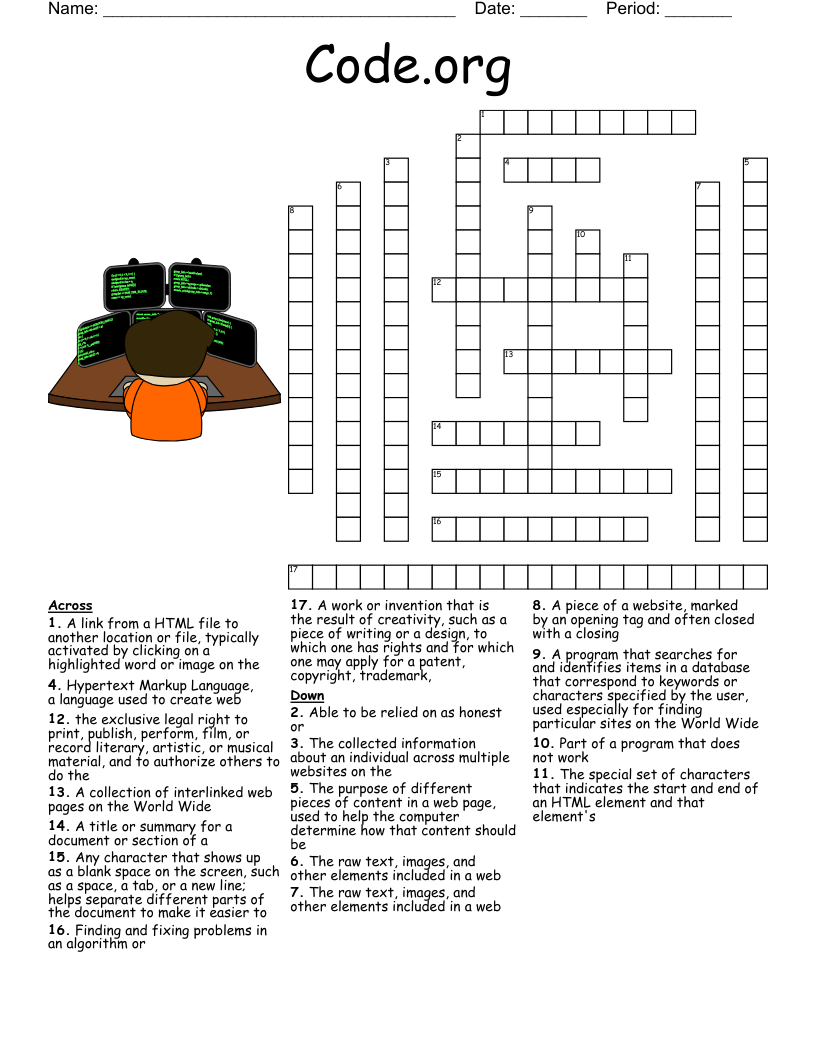
Digital Literacy Crossword
This printable crossword puzzle on the topic of Computer Science & Technology has 30 clues. Answers range from 4 to 27 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
When someone shares information on purpose and it becomes part of their digital footprint.
A fake screen name. Sometimes known as an “alt” account. Sometimes, these are used for cyber-bullying. Often, people figure out who is really behind these fake accounts.
When someone shares information on purpose and it becomes part of their digital footprint.
A software application you download to your device (such as a smartphone or tablet). There are apps for social media, games, etc.
Prejudice felt about certain things, people, or groups. Prejudice is an opinion that isn’t based on reason or fact.
Part of the visible light spectrum. Blue light from digital devices disrupts the hormones in your brain and can make it hard to sleep.
The scientific study of how the brain works.
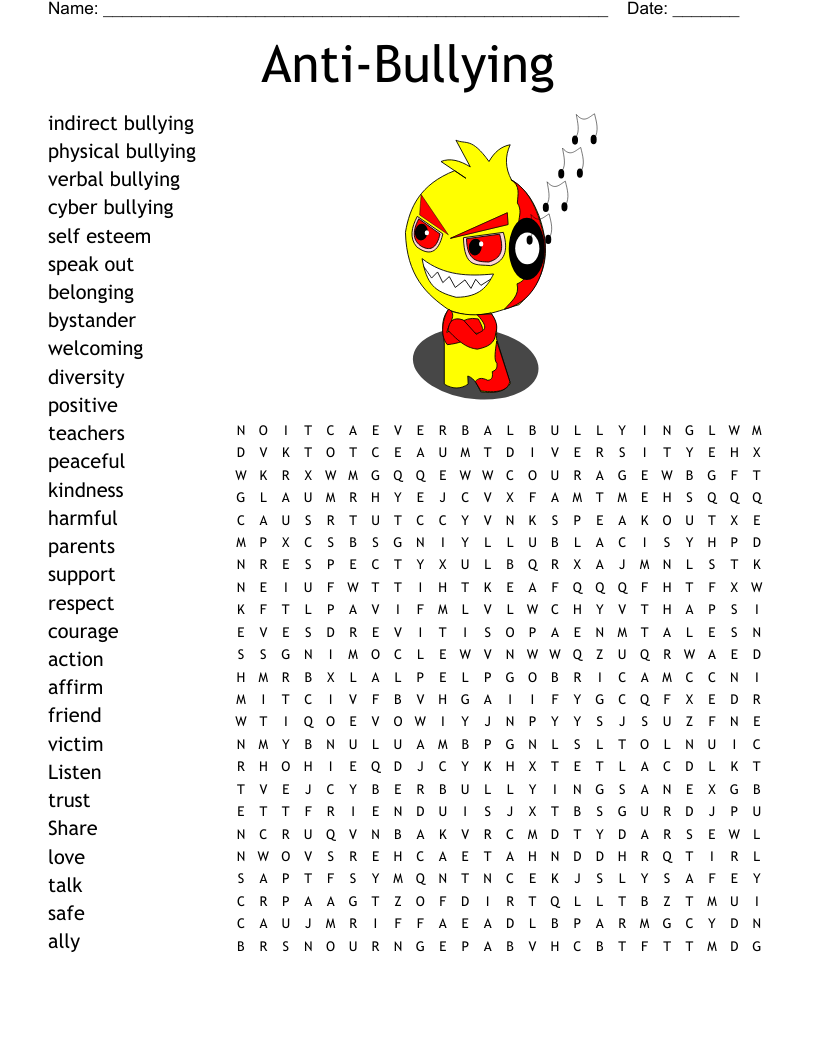
Bullying is unwanted, aggressive, and repeated actions (or actions that could be repeated). It happens when there’s a power imbalance. That imbalance could be physical or social. It could also be real or imagined.
A group of people with shared goals or interests, or who live or connect in the same place. A community can also be onli
Someone who has the right to copy, publish, sell, or distribute a creative work.
Creative works that can be used by the public, but may have restrictions on how they are used.
Curated content
Cyberbullying is bullying that happens online. It’s often in the form of harassing messages or posts. Sometimes those posts are anonymous.
People who gather and sell personal information that’s shared online.
begins with
Specific times when copyrighted material can be used without permission (usually for research, reporting, or teaching).
Your right to be part of a group and take action within that group.
Freedom of expression
When someone gets access to a system and steals your data to use or sell.
When you check and think about social media a lot.
When someone pretends to be you, by using your personal information.
When an app uses GPS to track where you are remotely. Some apps share your location through their site.
Short for malicious software. It introduces damage or gains access to your computer. Once it has access, it can steal your information.
When someone doesn’t know their information was gathered and it becomes part of their digital footprint.
When someone tries to get personal data online by pretending to be someone else.
Taking someone else’s words or ideas and presenting them as your own.
Places online where data can get stolen.
Direct or first-hand stories that come from the time period when the event being discussed happened
A policy that companies share when you use their services.
Image and information about you.