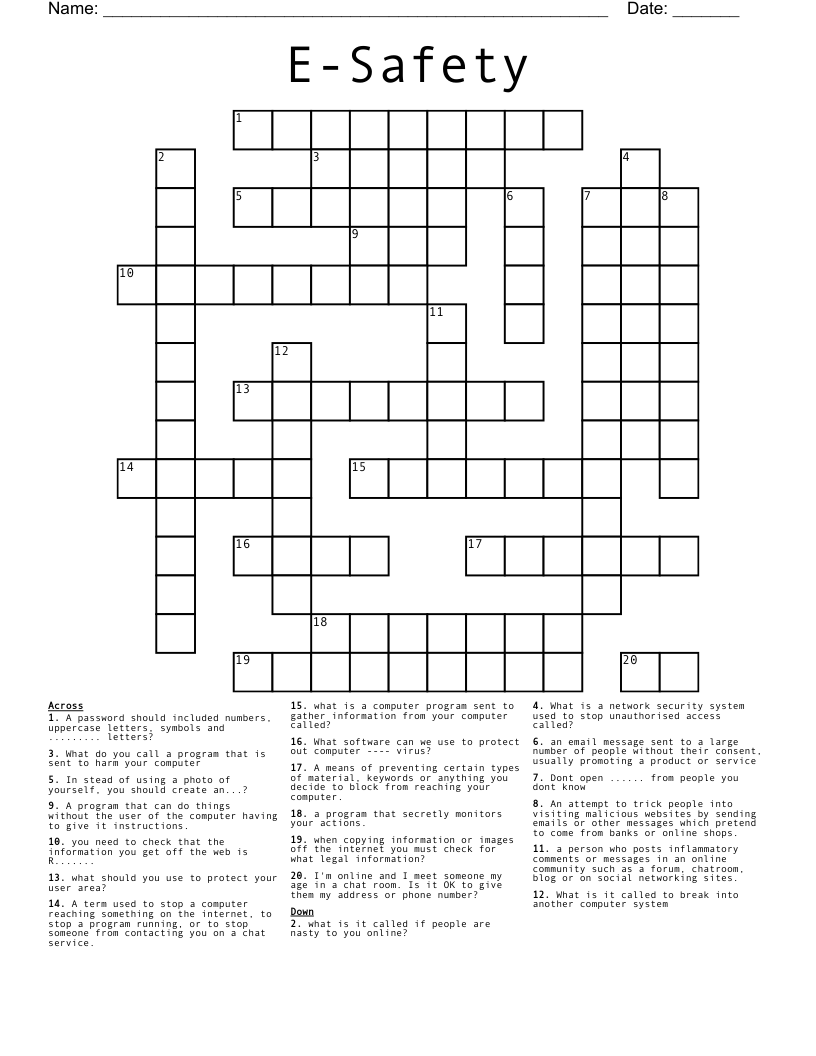
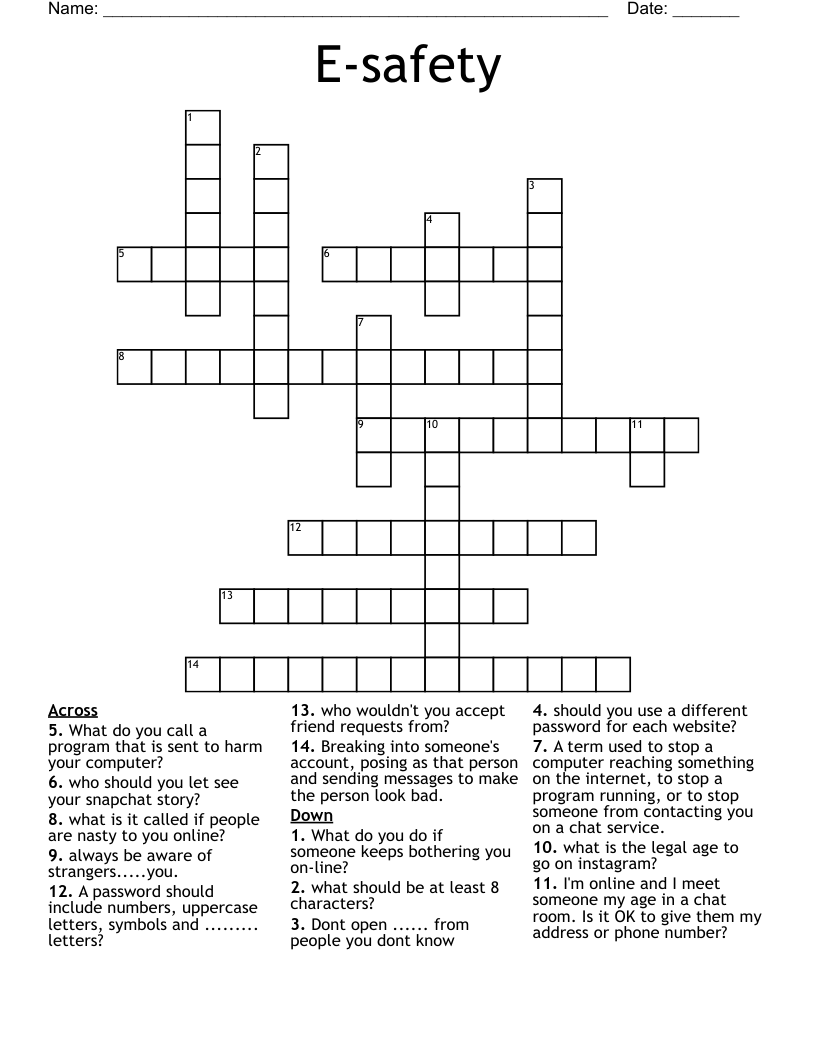
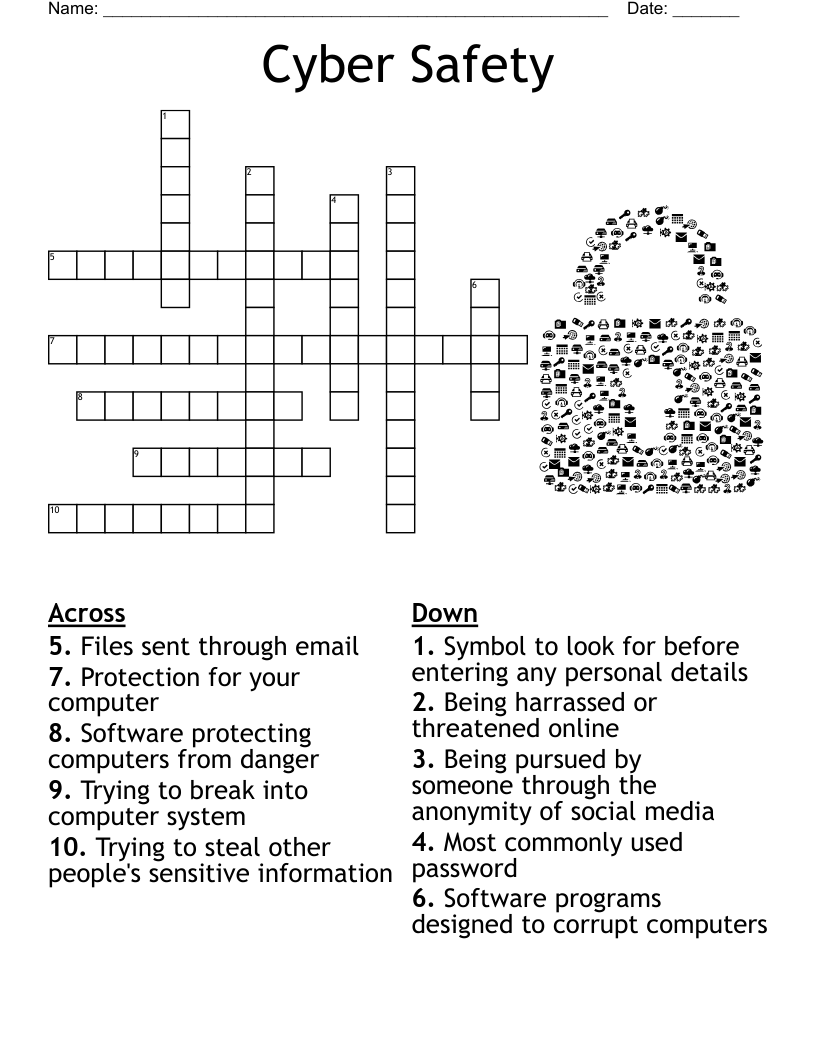
E-Safety Crossword
This printable crossword puzzle on the topic of Computer Science & Technology has 20 clues. Answers range from 2 to 13 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
What do you call a program that is sent to harm your computer
What is it called to break into another computer system
What software can we use to protect out computer ---- virus?
I'm online and I meet someone my age in a chat room. Is it OK to give them my address or phone number?
In stead of using a photo of yourself, you should create an...?
an email message sent to a large number of people without their consent, usually promoting a product or service
what is a computer program sent to gather information from your computer called?
What is a network security system used to stop unauthorised access called?
what should you use to protect your user area?
A password should included numbers, uppercase letters, symbols and ......... letters?
what is it called if people are nasty to you online?
Dont open ...... from people you dont know
A term used to stop a computer reaching something on the internet, to stop a program running, or to stop someone from contacting you on a chat service.
A program that can do things without the user of the computer having to give it instructions.
A means of preventing certain types of material, keywords or anything you decide to block from reaching your computer.
An attempt to trick people into visiting malicious websites by sending emails or other messages which pretend to come from banks or online shops.
a program that secretly monitors your actions.
a person who posts inflammatory comments or messages in an online community such as a forum, chatroom, blog or on social networking sites.
when copying information or images off the internet you must check for what legal information?
you need to check that the information you get off the web is R.......