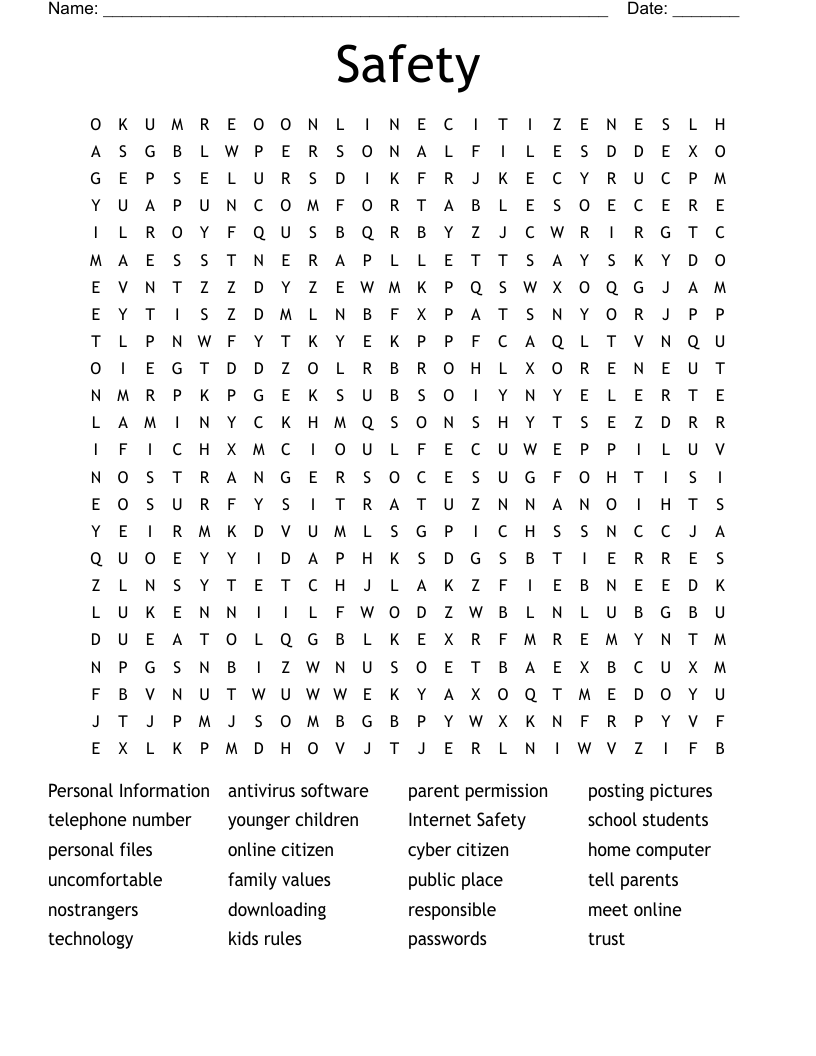
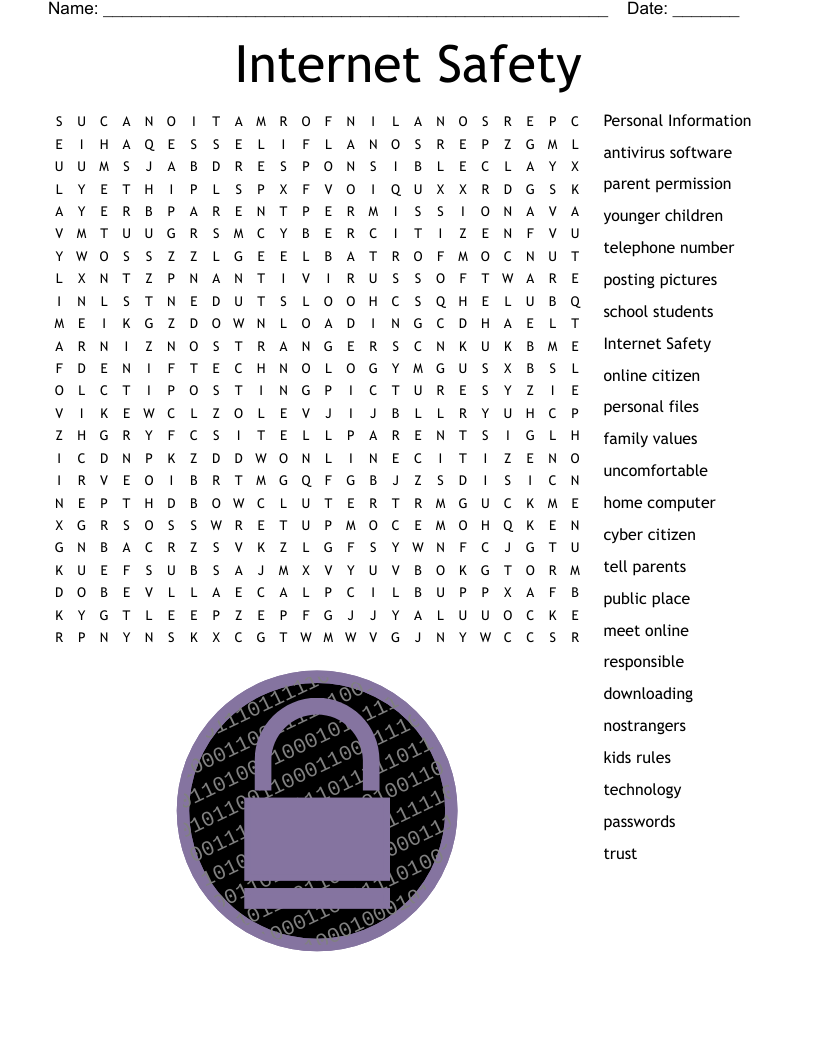
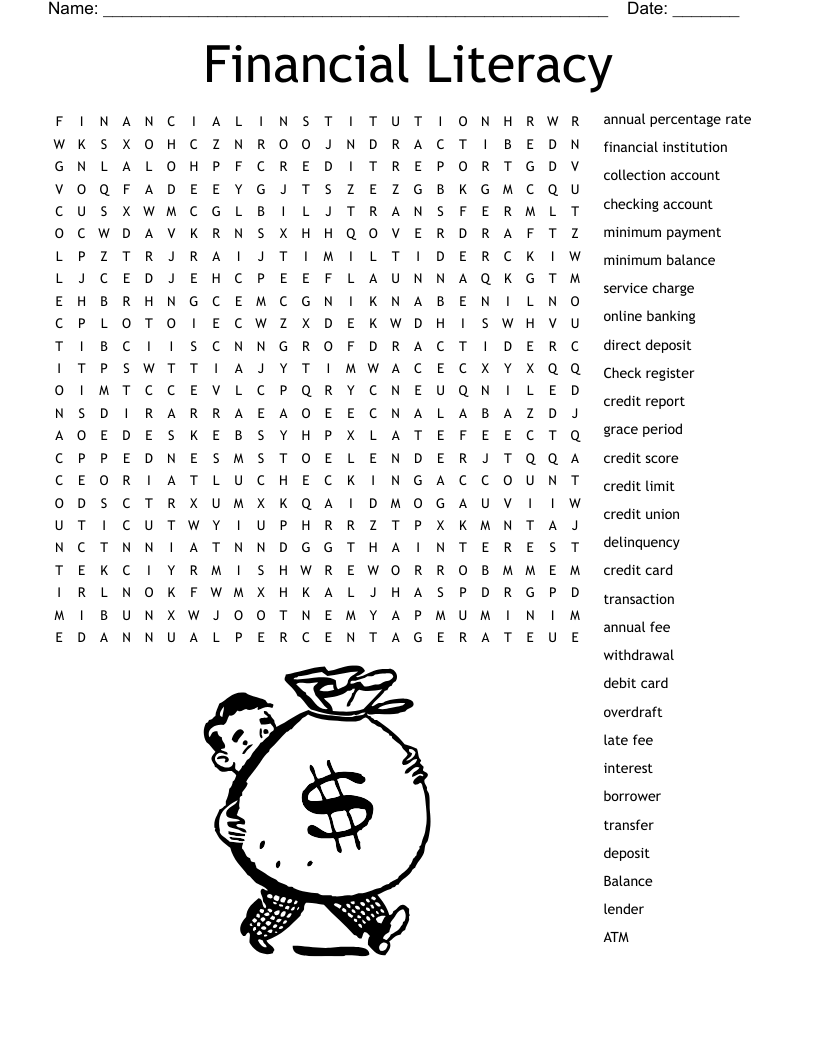
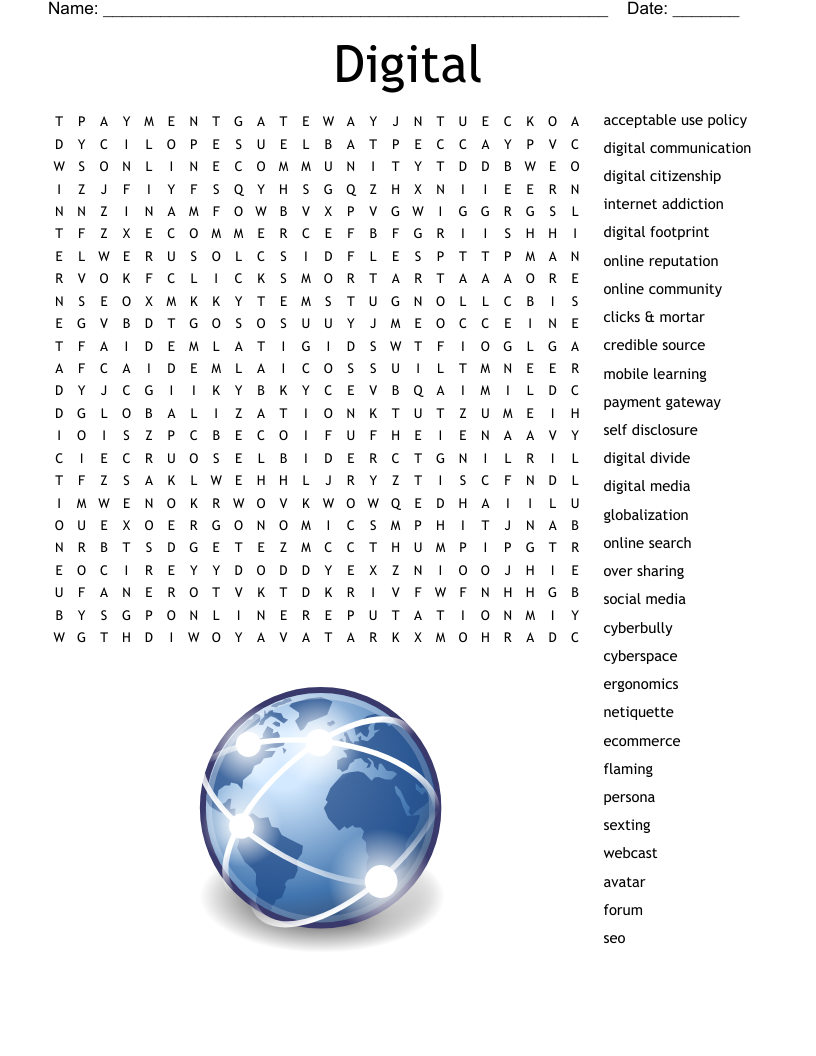
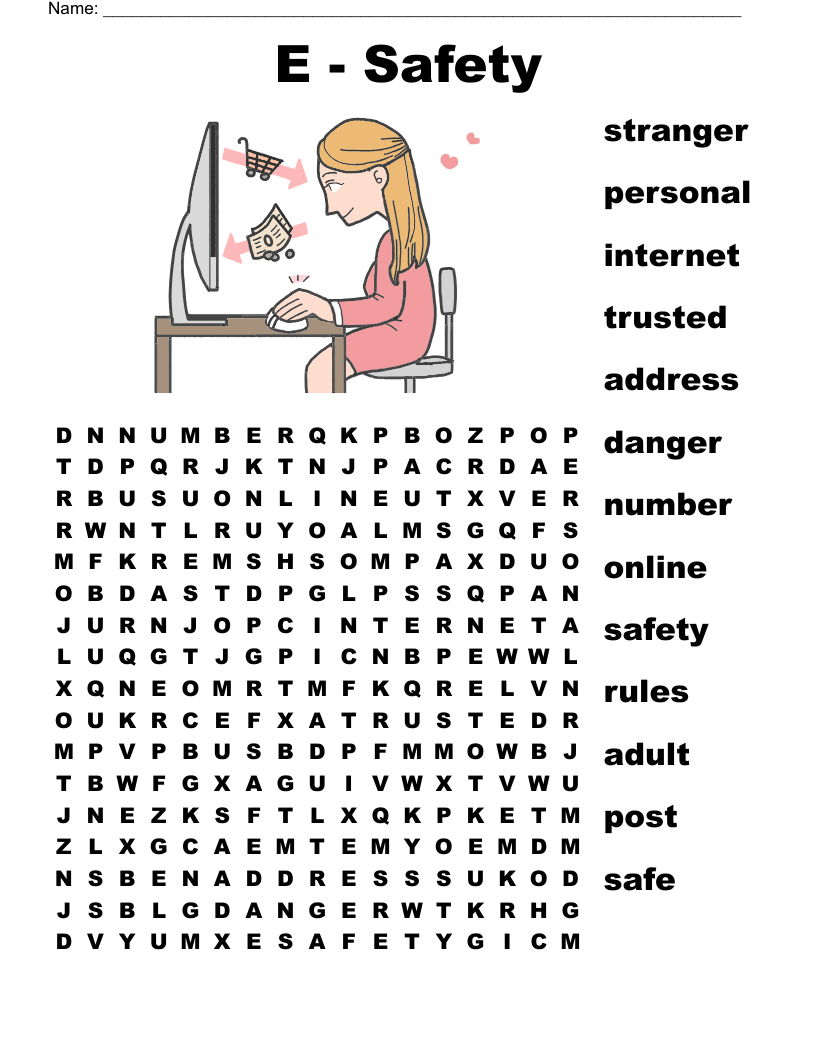
Safety Word Search
This printable word search puzzle on the topic of Computer Science & Technology contains 24 hidden words in a 24x24 letter grid. Words go horizontally, vertically, backwards, and diagonally. This word search is also available to download as a Microsoft Word document or a PDF.
Description
Personal Information
antivirus software
parent permission
posting pictures
telephone number
younger children
Internet Safety
school students
personal files
online citizen
cyber citizen
home computer
uncomfortable
family values
public place
tell parents
nostrangers
downloading
responsible
meet online
technology
kids rules
passwords
trust
Customize
Add, edit, delete clues, and customize this puzzle. Print copies for an entire class.