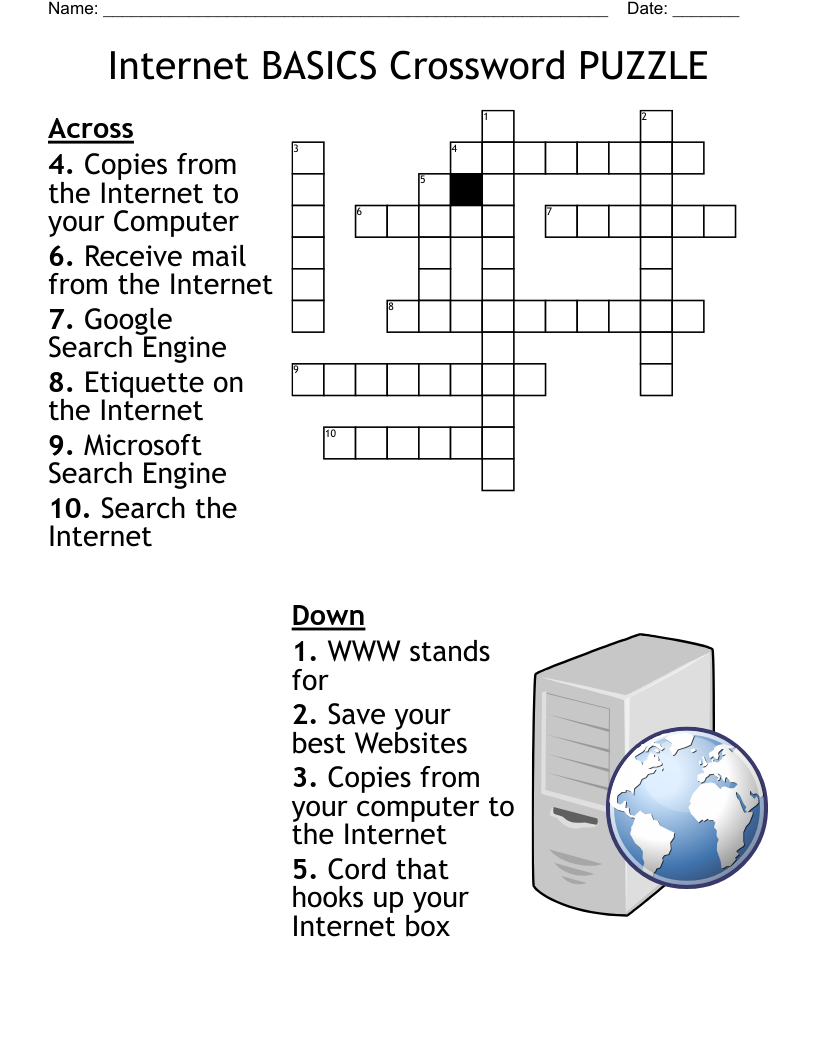
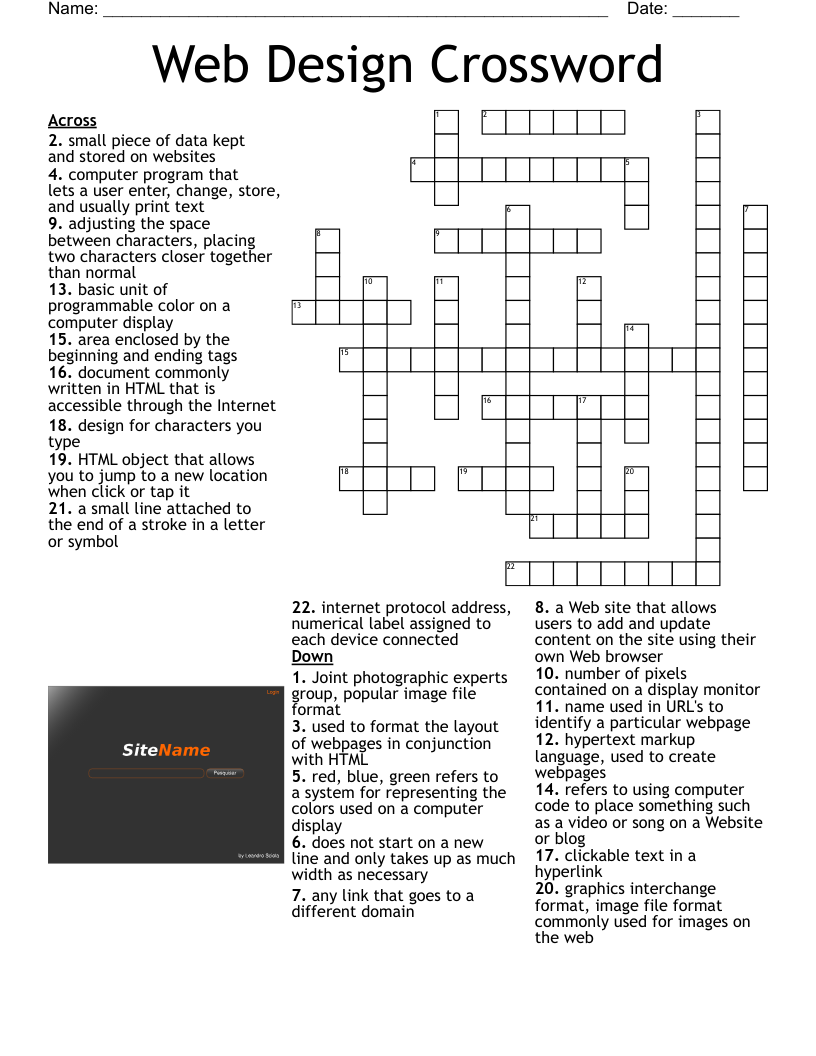
S.6 Internet and WWW Puzzle Crossword
This printable crossword puzzle on the topic of Computer Science & Technology has 13 clues. Answers range from 3 to 12 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
the global interconnection of computer networks
a private network inside a company or organization
messages distributed by electronic means from one computer user to one or more recipients via a network.
devices used to process, host and transmit data on a network
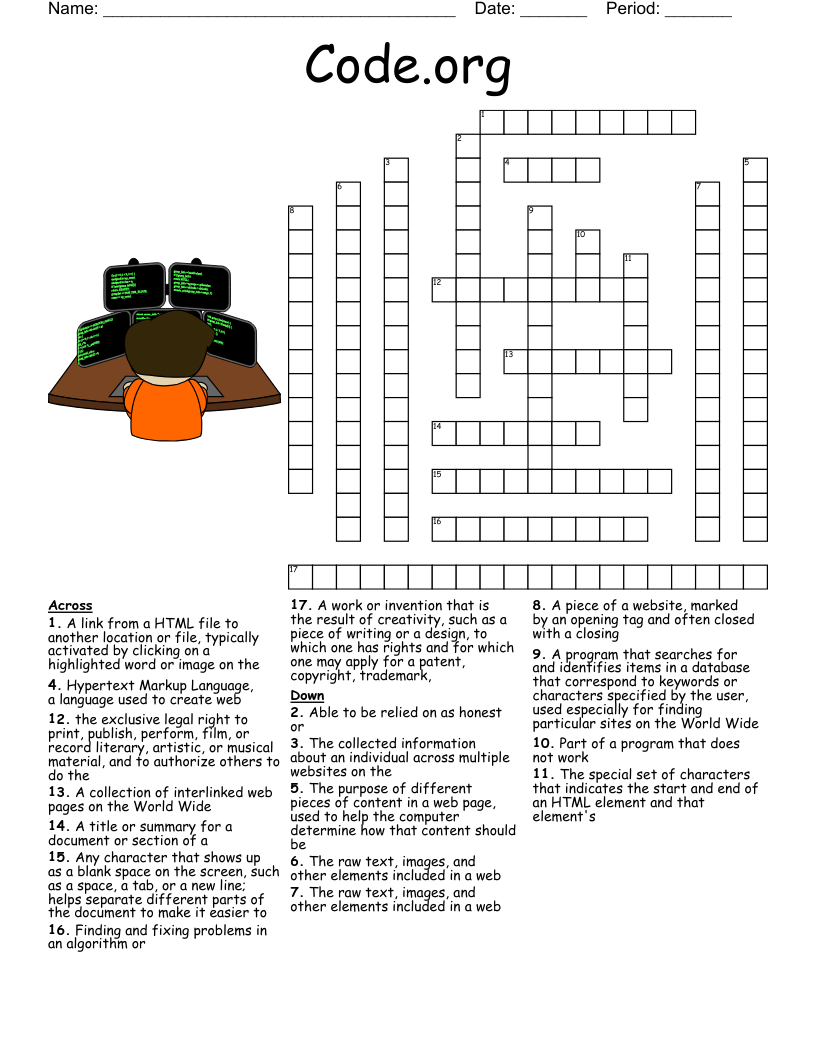
a program that lets the user surf the internet
programs that allows the user to easily search and retrieve information on the internet
a website containing personal information which can easily be updated
a set of rules governing communication on a network
links used to navigate from one web page to another
the web address that connects the user to a particular website.
a physical location where people may obtain Internet access, typically using Wi-Fi technology
to enable copies of e-mail to be sent to a third party while acknowledging other recipients.
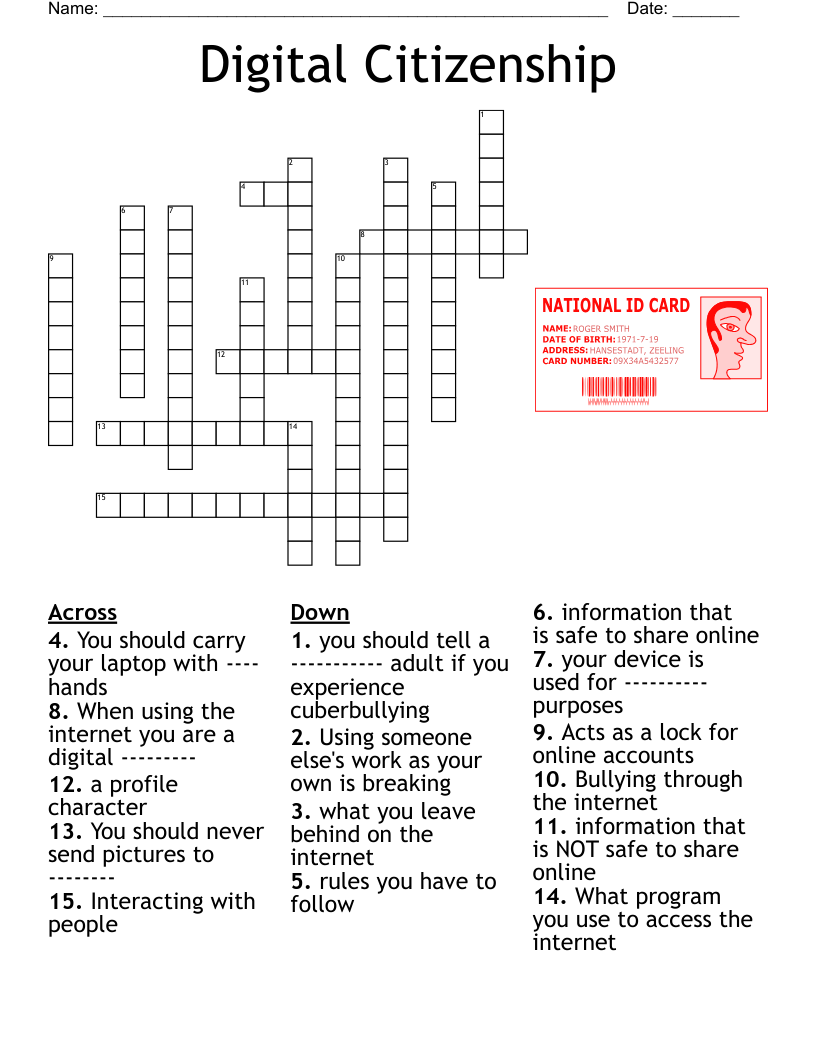
a set of rules for acceptable online conduct and behavior