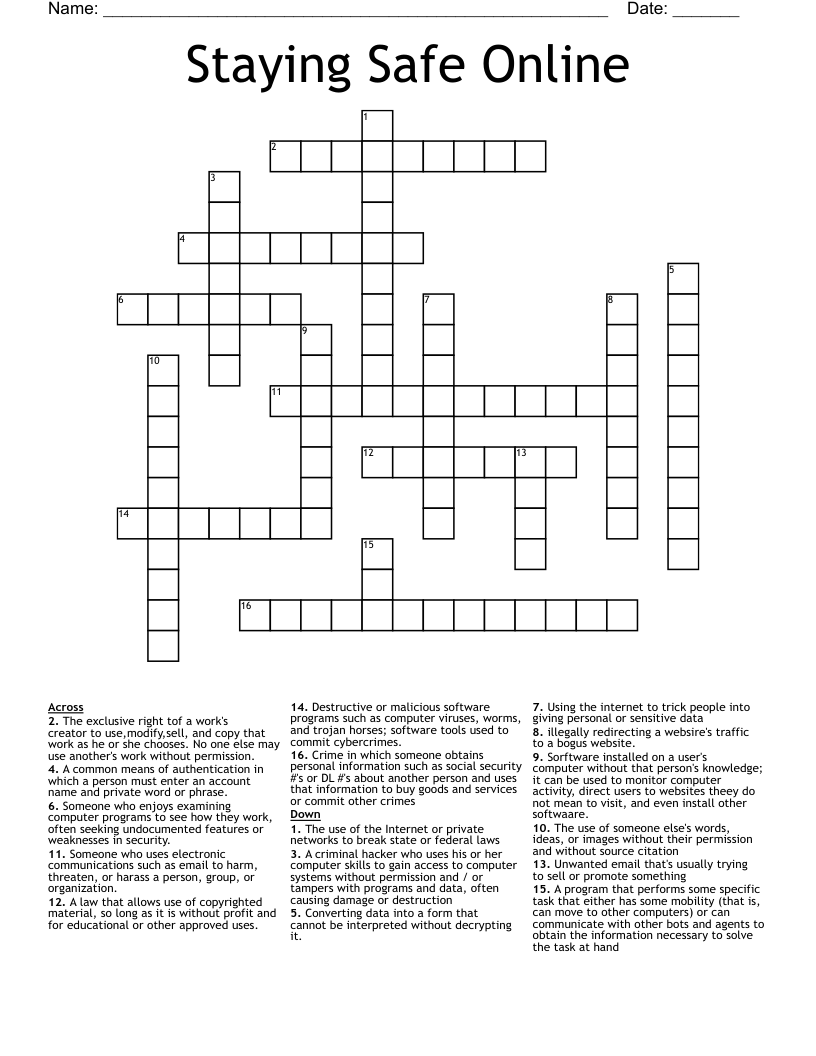
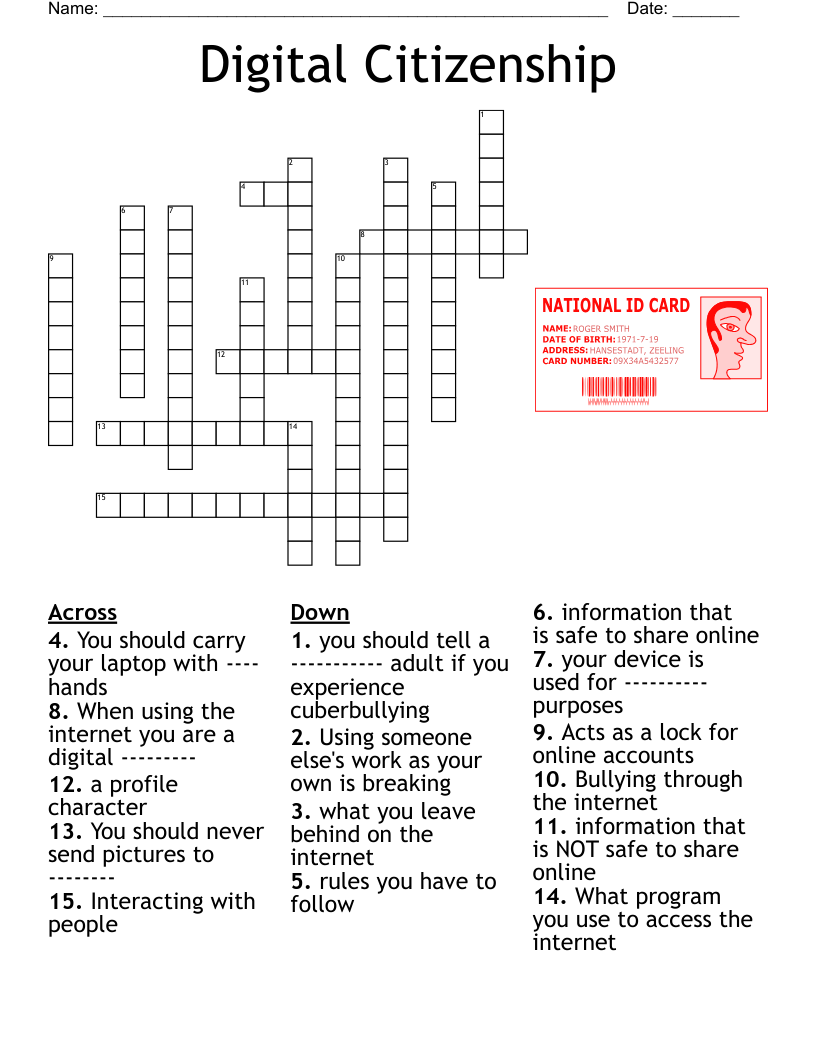
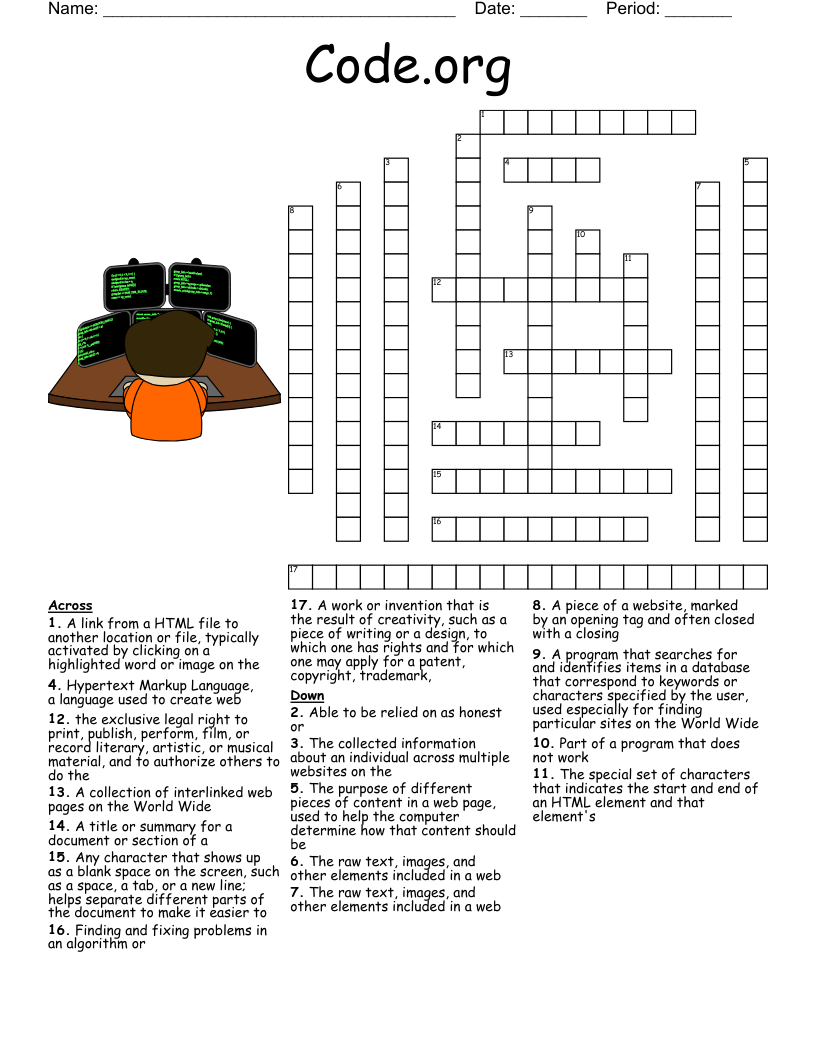
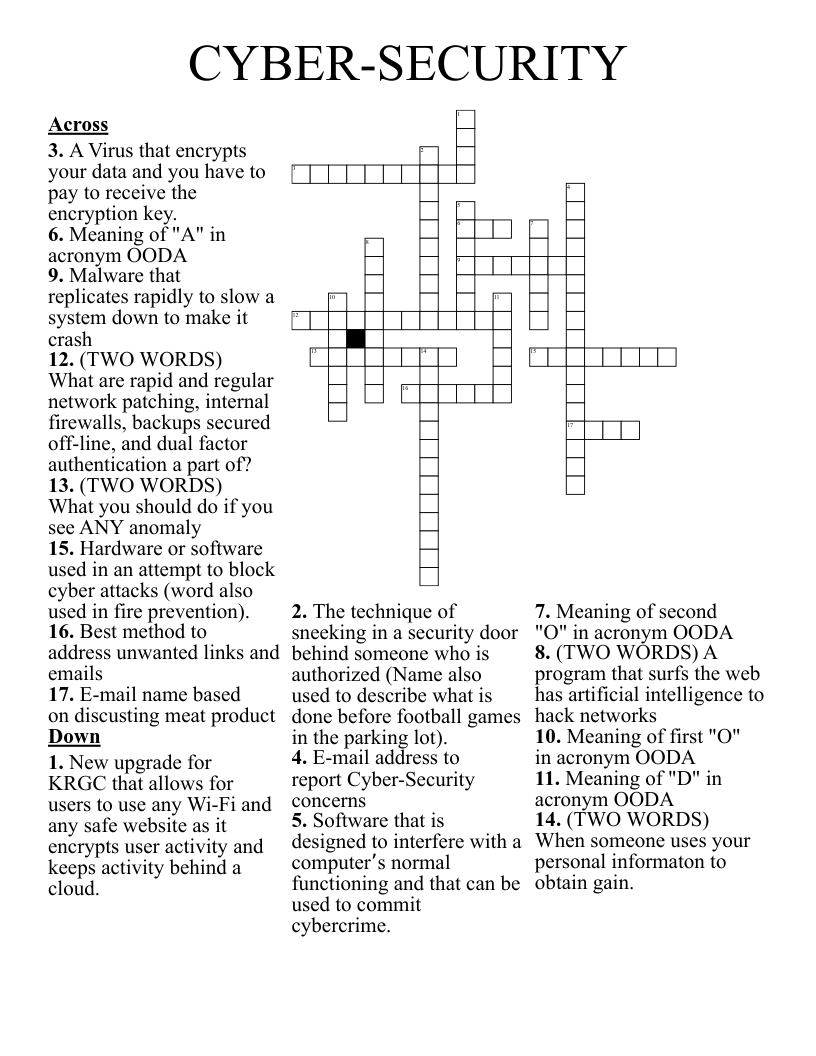
Staying Safe Online Crossword
This printable crossword puzzle on the topic of Computer Science & Technology has 16 clues. Answers range from 3 to 13 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
A program that performs some specific task that either has some mobility (that is, can move to other computers) or can communicate with other bots and agents to obtain the information necessary to solve the task at hand
The exclusive right tof a work's creator to use,modify,sell, and copy that work as he or she chooses. No one else may use another's work without permission.
A criminal hacker who uses his or her computer skills to gain access to computer systems without permission and / or tampers with programs and data, often causing damage or destruction
The use of the Internet or private networks to break state or federal laws
Someone who uses electronic communications such as email to harm, threaten, or harass a person, group, or organization.
Converting data into a form that cannot be interpreted without decrypting it.
A law that allows use of copyrighted material, so long as it is without profit and for educational or other approved uses.
Someone who enjoys examining computer programs to see how they work, often seeking undocumented features or weaknesses in security.
Crime in which someone obtains personal information such as social security #'s or DL #'s about another person and uses that information to buy goods and services or commit other crimes
Destructive or malicious software programs such as computer viruses, worms, and trojan horses; software tools used to commit cybercrimes.
A common means of authentication in which a person must enter an account name and private word or phrase.
illegally redirecting a websire's traffic to a bogus website.
Using the internet to trick people into giving personal or sensitive data
The use of someone else's words, ideas, or images without their permission and without source citation
Unwanted email that's usually trying to sell or promote something
Sorftware installed on a user's computer without that person's knowledge; it can be used to monitor computer activity, direct users to websites theey do not mean to visit, and even install other softwaare.