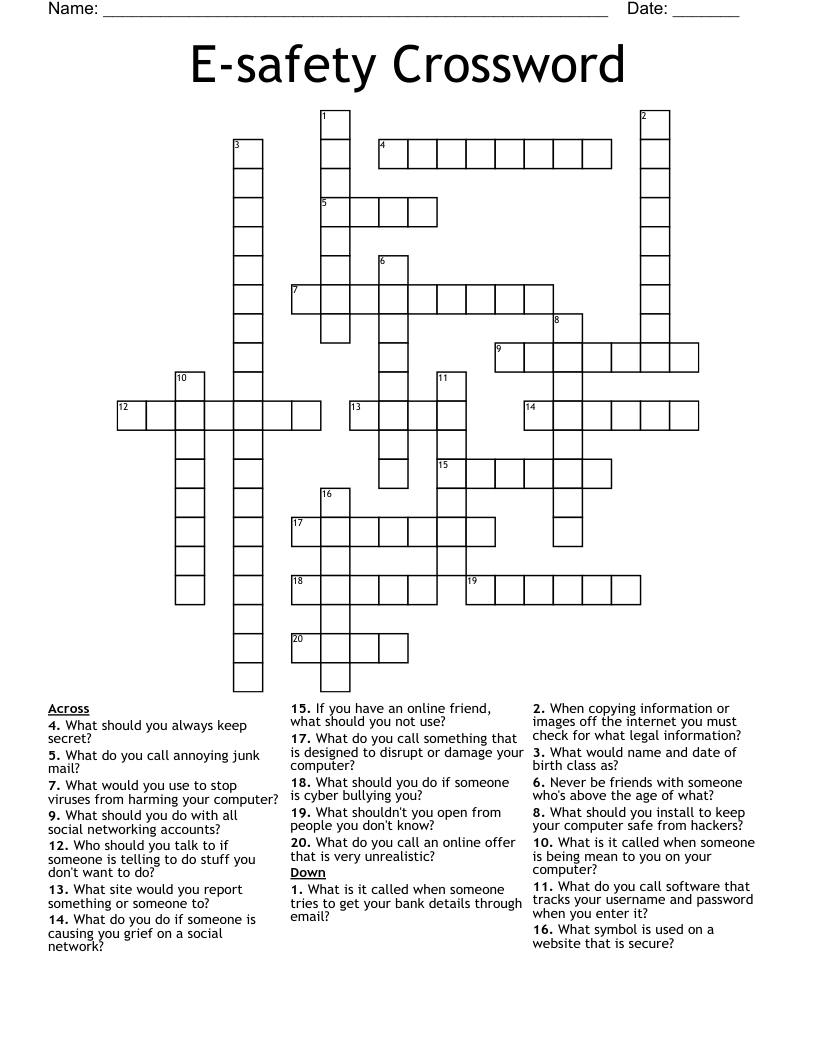
E-safety Crossword
This printable crossword puzzle on the topic of Computer Science & Technology has 20 clues. Answers range from 4 to 19 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
What is it called when someone tries to get your bank details through email?
What would you use to stop viruses from harming your computer?
What is it called when someone is being mean to you on your computer?
What do you call annoying junk mail?
What do you call something that is designed to disrupt or damage your computer?
Who should you talk to if someone is telling to do stuff you don't want to do?
What do you do if someone is causing you grief on a social network?
What would name and date of birth class as?
What should you do if someone is cyber bullying you?
If you have an online friend, what should you not use?
What should you do with all social networking accounts?
Never be friends with someone who's above the age of what?
What site would you report something or someone to?
What should you always keep secret?
What should you install to keep your computer safe from hackers?
What symbol is used on a website that is secure?
What do you call an online offer that is very unrealistic?
What do you call software that tracks your username and password when you enter it?
When copying information or images off the internet you must check for what legal information?
What shouldn't you open from people you don't know?