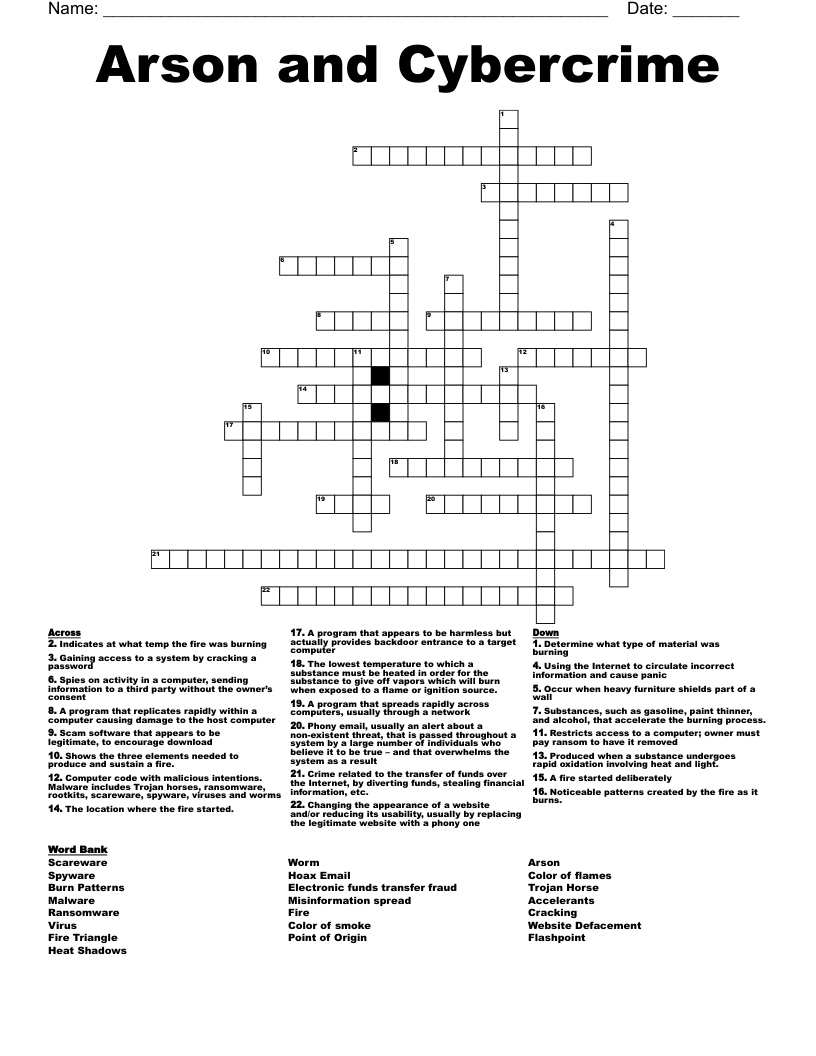
Arson and Cybercrime Crossword
This printable crossword puzzle on the topic of Law & Legal has 22 clues. Answers range from 4 to 28 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
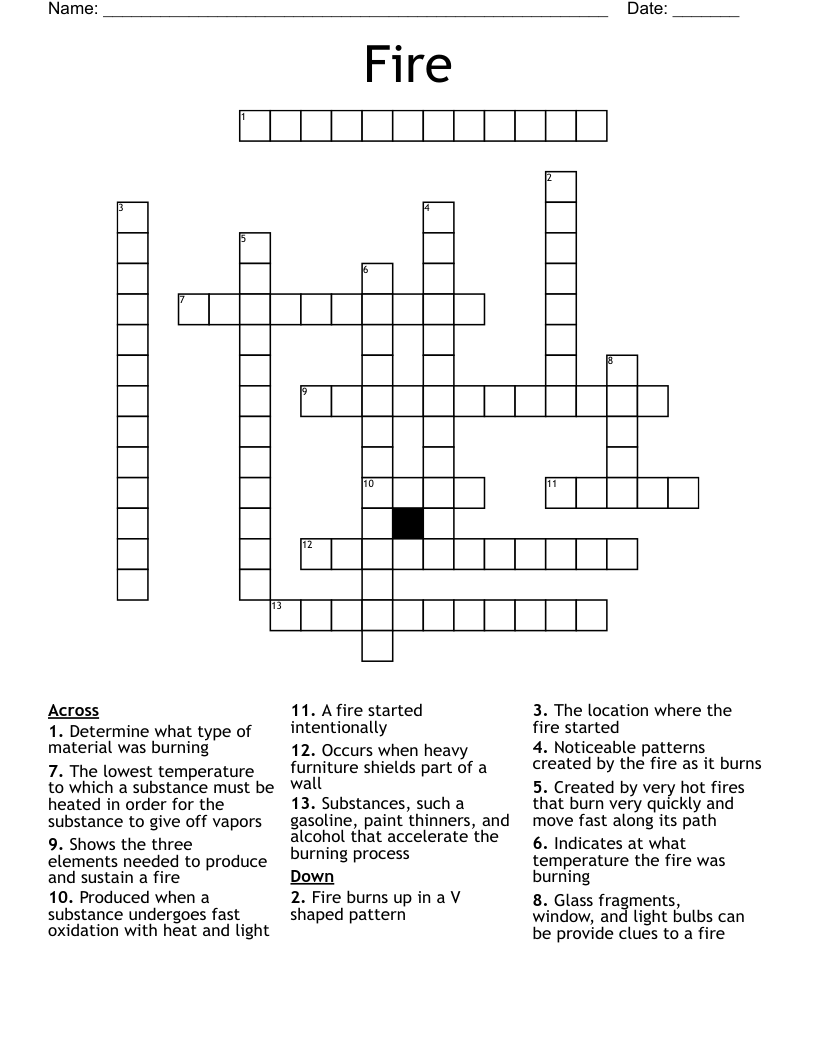
Indicates at what temp the fire was burning
Produced when a substance undergoes rapid oxidation involving heat and light.
The lowest temperature to which a substance must be heated in order for the substance to give off vapors which will burn when exposed to a flame or ignition source.
The location where the fire started.
A fire started deliberately
Substances, such as gasoline, paint thinner, and alcohol, that accelerate the burning process.
Noticeable patterns created by the fire as it burns.
Shows the three elements needed to produce and sustain a fire.
Determine what type of material was burning
Occur when heavy furniture shields part of a wall
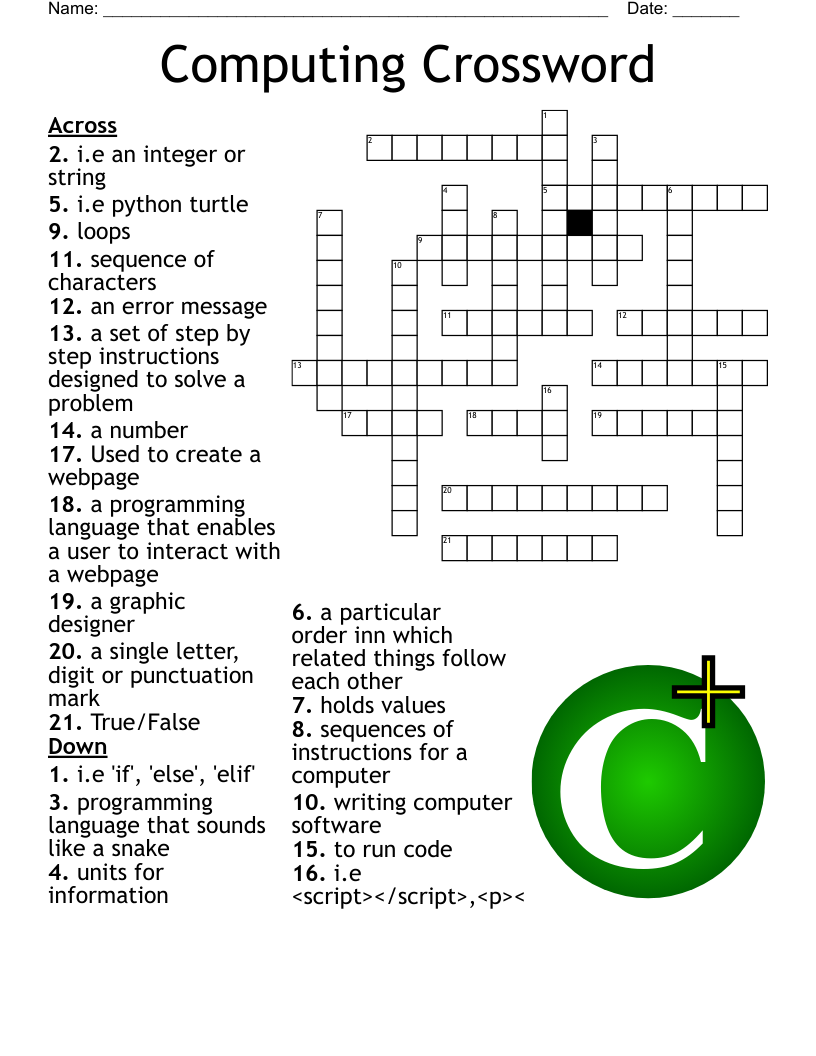
Gaining access to a system by cracking a password
A program that appears to be harmless but actually provides backdoor entrance to a target computer
Computer code with malicious intentions. Malware includes Trojan horses, ransomware, rootkits, scareware, spyware, viruses and worms
Scam software that appears to be legitimate, to encourage download
A program that replicates rapidly within a computer causing damage to the host computer
A program that spreads rapidly across computers, usually through a network
Spies on activity in a computer, sending information to a third party without the owner’s consent
Changing the appearance of a website and/or reducing its usability, usually by replacing the legitimate website with a phony one
Restricts access to a computer; owner must pay ransom to have it removed
Using the Internet to circulate incorrect information and cause panic
Phony email, usually an alert about a non-existent threat, that is passed throughout a system by a large number of individuals who believe it to be true – and that overwhelms the system as a result
Crime related to the transfer of funds over the Internet, by diverting funds, stealing financial information, etc.