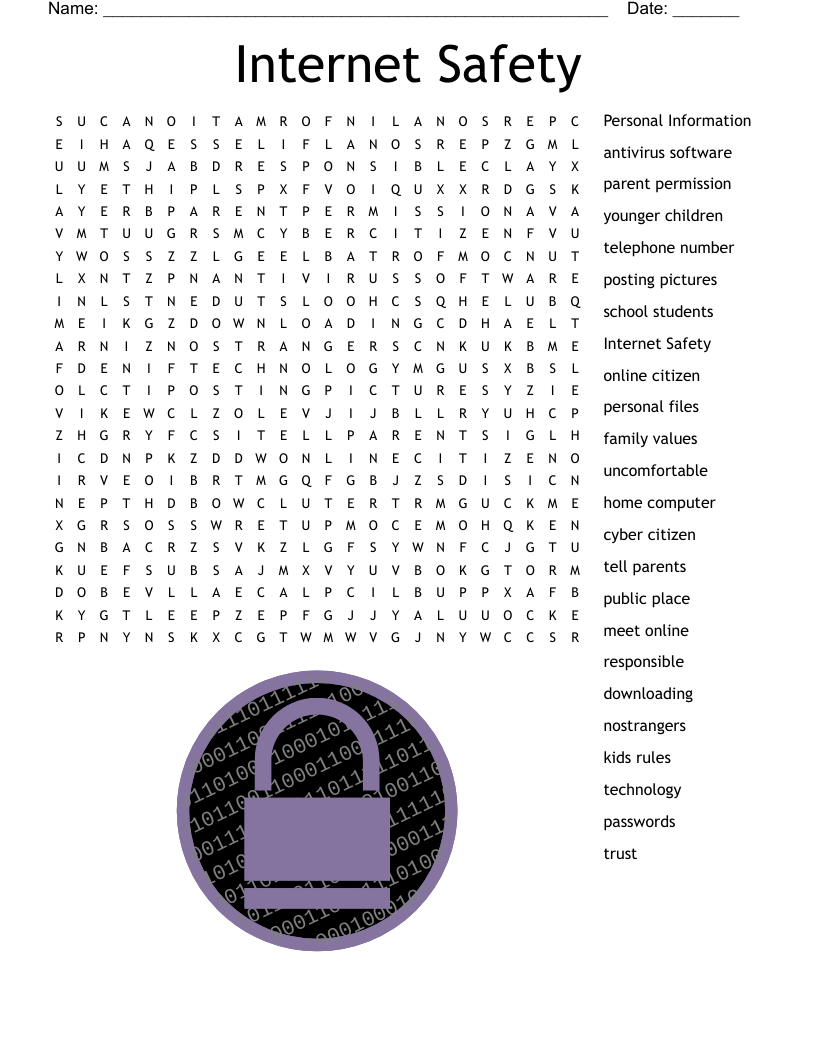
Internet Safety Crossword
This printable crossword puzzle on the topic of Computer Science & Technology has 10 clues. Answers range from 5 to 17 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
Trying to steal other people's sensitive information
Trying to break into computer systems
Software programs designed to corrupt computers
Software protecting computers from danger
Being pursued by someone through the anonymity of social media
Symbol to look for before entering ANY personal details
Being harrassed or threatened online
Most commonly used password
Protection for your computer
Files sent through email
Customize
Add, edit, delete clues, and customize this puzzle. Print copies for an entire class.