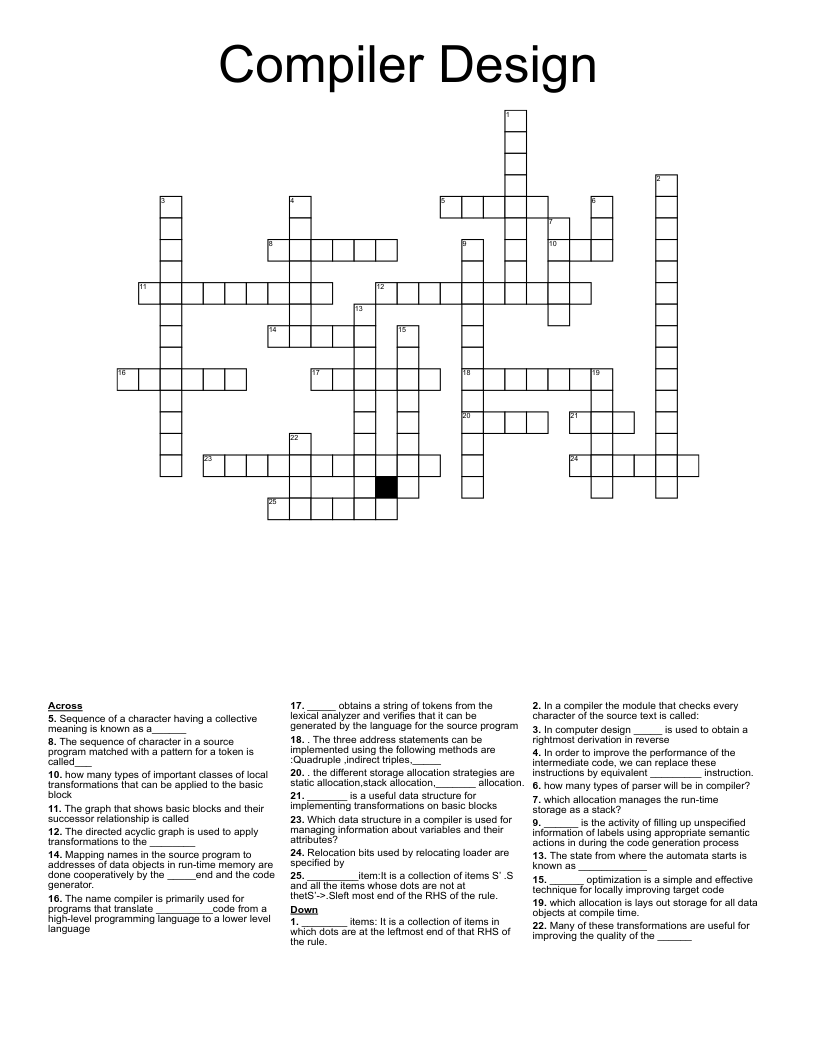
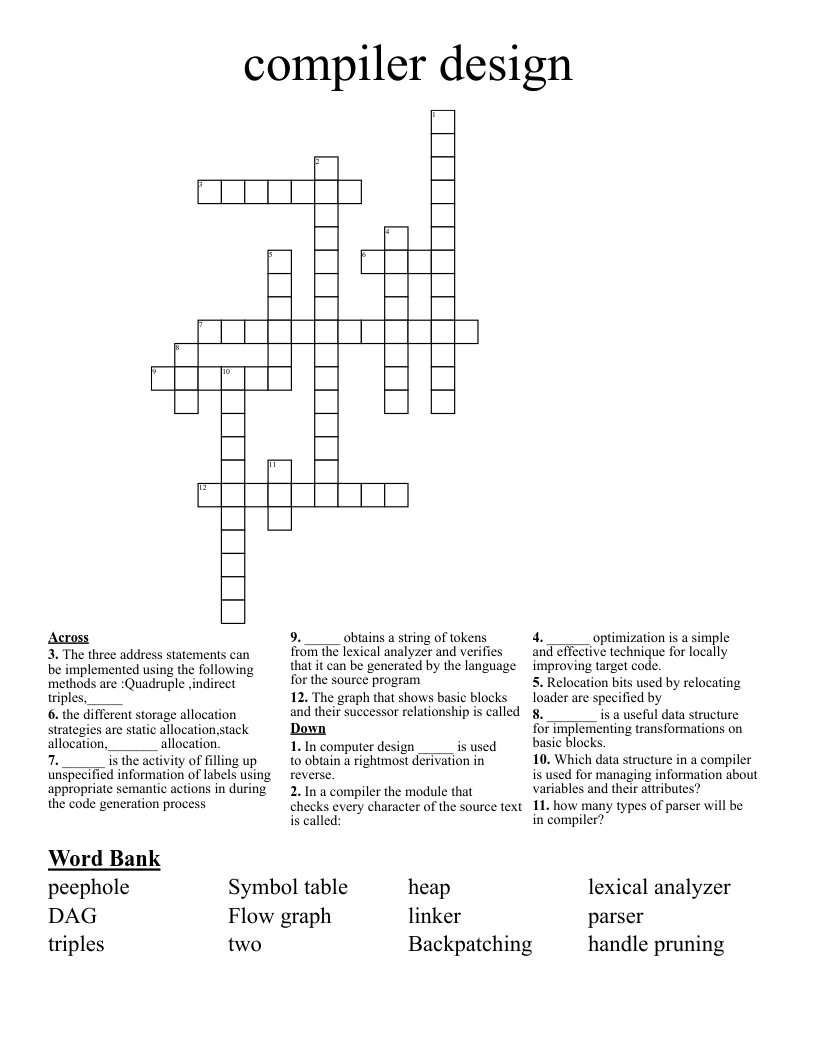
Compiler Design Crossword
This printable crossword puzzle on the topic of Computer Science & Technology has 25 clues. Answers range from 3 to 15 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
. The three address statements can be implemented using the following methods are :Quadruple ,indirect triples,_____
. the different storage allocation strategies are static allocation,stack allocation,_______ allocation.
______ is the activity of filling up unspecified information of labels using appropriate semantic actions in during the code generation process
_____ obtains a string of tokens from the lexical analyzer and verifies that it can be generated by the language for the source program
The graph that shows basic blocks and their successor relationship is called
In computer design _____ is used to obtain a rightmost derivation in reverse
In a compiler the module that checks every character of the source text is called:
______ optimization is a simple and effective technique for locally improving target code
Relocation bits used by relocating loader are specified by
_______ is a useful data structure for implementing transformations on basic blocks
Which data structure in a compiler is used for managing information about variables and their attributes?
how many types of parser will be in compiler?
The name compiler is primarily used for programs that translate __________code from a high-level programming language to a lower level language
The state from where the automata starts is known as ____________
In order to improve the performance of the intermediate code, we can replace these instructions by equivalent _________ instruction.
The directed acyclic graph is used to apply transformations to the ________
which allocation manages the run-time storage as a stack?
which allocation is lays out storage for all data objects at compile time.
how many types of important classes of local transformations that can be applied to the basic block
Many of these transformations are useful for improving the quality of the ______
Mapping names in the source program to addresses of data objects in run-time memory are done cooperatively by the _____end and the code generator.
Sequence of a character having a collective meaning is known as a______
The sequence of character in a source program matched with a pattern for a token is called___
_________item:It is a collection of items S’ .S and all the items whose dots are not at thetS’->.Sleft most end of the RHS of the rule.
________ items: It is a collection of items in which dots are at the leftmost end of that RHS of the rule.