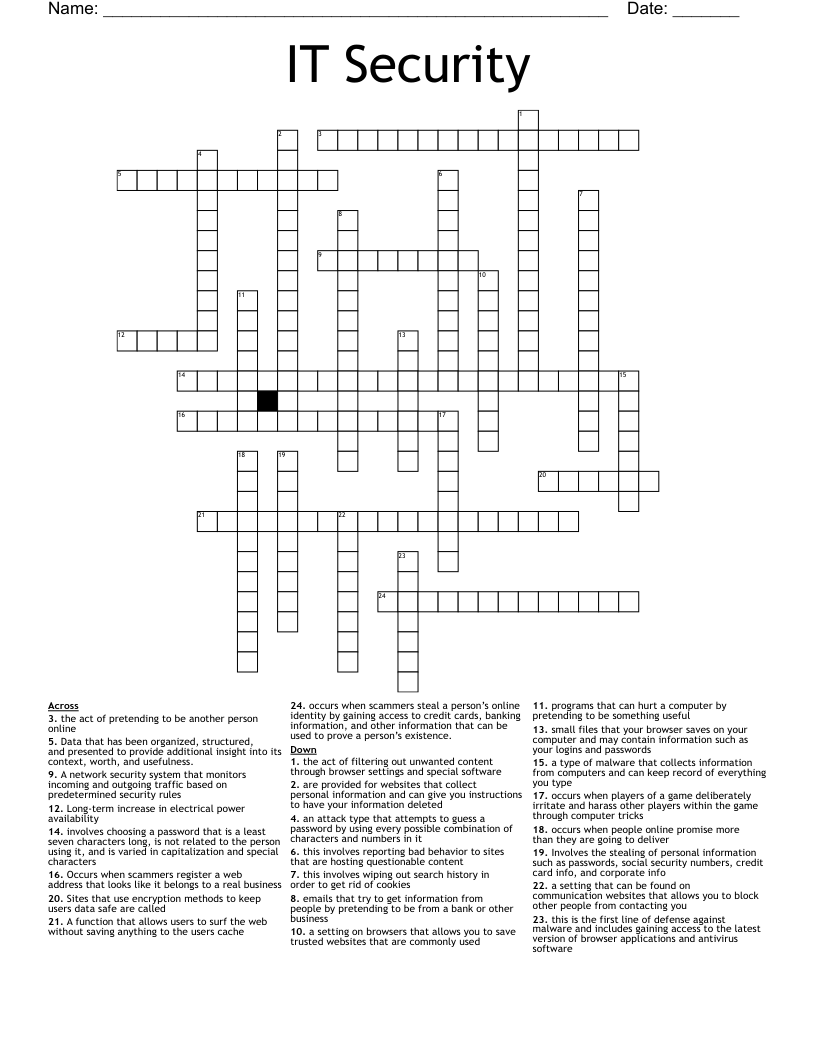
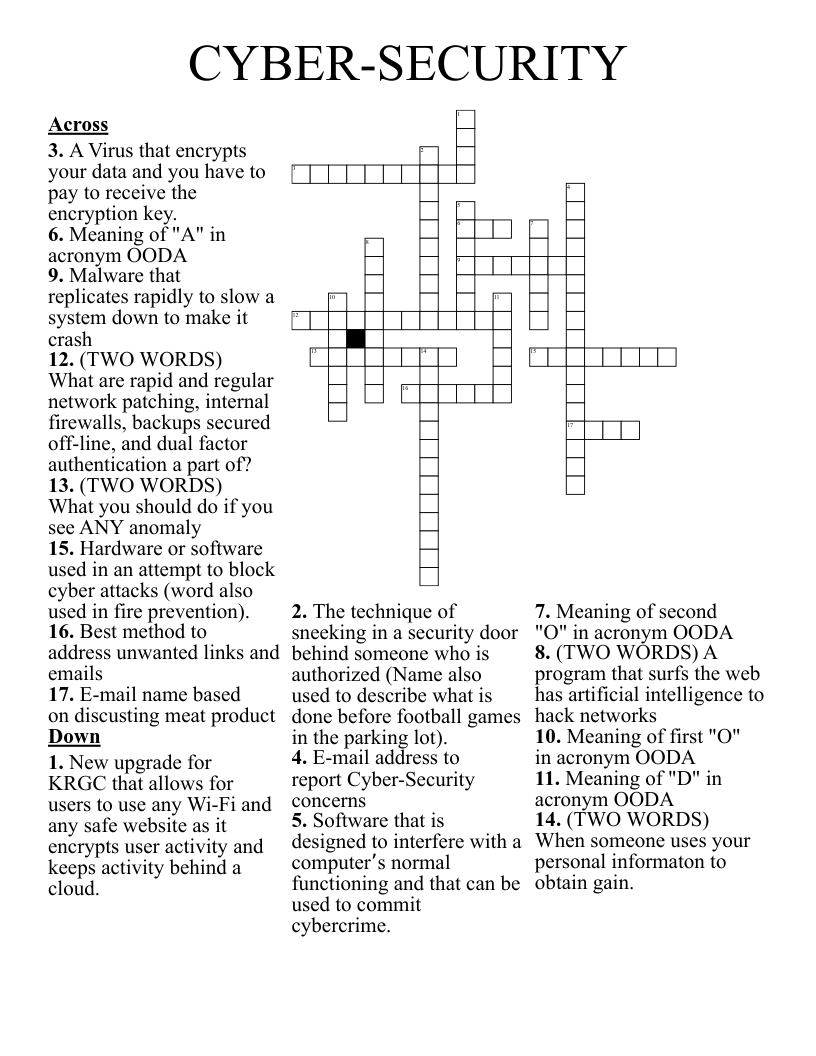
IT Security Crossword
This printable crossword puzzle on the topic of Computer Science & Technology has 24 clues. Answers range from 5 to 23 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
Occurs when scammers register a web address that looks like it belongs to a real business
small files that your browser saves on your computer and may contain information such as your logins and passwords
Involves the stealing of personal information such as passwords, social security numbers, credit card info, and corporate info
occurs when players of a game deliberately irritate and harass other players within the game through computer tricks
the act of pretending to be another person online
occurs when scammers steal a person’s online identity by gaining access to credit cards, banking information, and other information that can be used to prove a person’s existence.
programs that can hurt a computer by pretending to be something useful
occurs when people online promise more than they are going to deliver
emails that try to get information from people by pretending to be from a bank or other business
a type of malware that collects information from computers and can keep record of everything you type
a setting on browsers that allows you to save trusted websites that are commonly used
a setting that can be found on communication websites that allows you to block other people from contacting you
this is the first line of defense against malware and includes gaining access to the latest version of browser applications and antivirus software
this involves wiping out search history in order to get rid of cookies
this involves reporting bad behavior to sites that are hosting questionable content
the act of filtering out unwanted content through browser settings and special software
involves choosing a password that is a least seven characters long, is not related to the person using it, and is varied in capitalization and special characters
A network security system that monitors incoming and outgoing traffic based on predetermined security rules
are provided for websites that collect personal information and can give you instructions to have your information deleted
A function that allows users to surf the web without saving anything to the users cache
Sites that use encryption methods to keep users data safe are called
Data that has been organized, structured, and presented to provide additional insight into its context, worth, and usefulness.
Long-term increase in electrical power availability
an attack type that attempts to guess a password by using every possible combination of characters and numbers in it