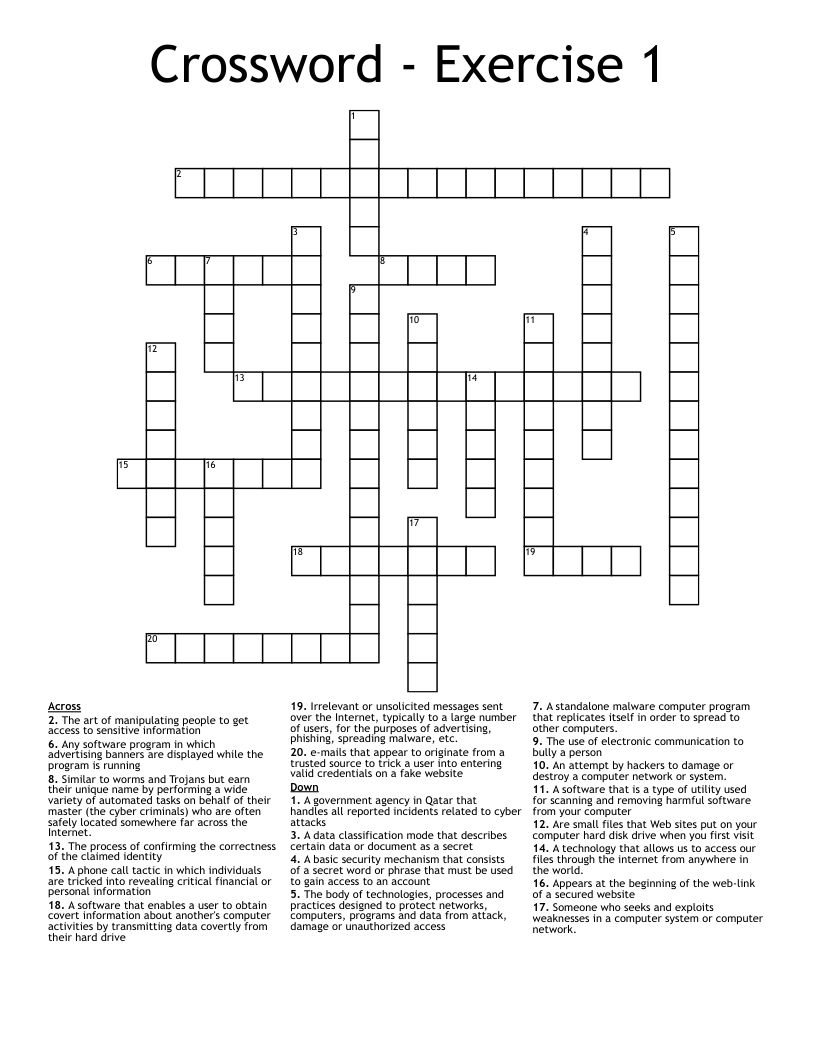
Crossword - Exercise 1
This printable crossword puzzle has 20 clues. Answers range from 4 to 17 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
A basic security mechanism that consists of a secret word or phrase that must be used to gain access to an account
An attempt by hackers to damage or destroy a computer network or system.
Someone who seeks and exploits weaknesses in a computer system or computer network.
The process of confirming the correctness of the claimed identity
e-mails that appear to originate from a trusted source to trick a user into entering valid credentials on a fake website
The body of technologies, processes and practices designed to protect networks, computers, programs and data from attack, damage or unauthorized access
A standalone malware computer program that replicates itself in order to spread to other computers.
Are small files that Web sites put on your computer hard disk drive when you first visit
A technology that allows us to access our files through the internet from anywhere in the world.
Appears at the beginning of the web-link of a secured website
Irrelevant or unsolicited messages sent over the Internet, typically to a large number of users, for the purposes of advertising, phishing, spreading malware, etc.
A data classification mode that describes certain data or document as a secret
A government agency in Qatar that handles all reported incidents related to cyber attacks
The art of manipulating people to get access to sensitive information
A software that is a type of utility used for scanning and removing harmful software from your computer
Any software program in which advertising banners are displayed while the program is running
The use of electronic communication to bully a person
A phone call tactic in which individuals are tricked into revealing critical financial or personal information
A software that enables a user to obtain covert information about another's computer activities by transmitting data covertly from their hard drive
Similar to worms and Trojans but earn their unique name by performing a wide variety of automated tasks on behalf of their master (the cyber criminals) who are often safely located somewhere far across the Internet.