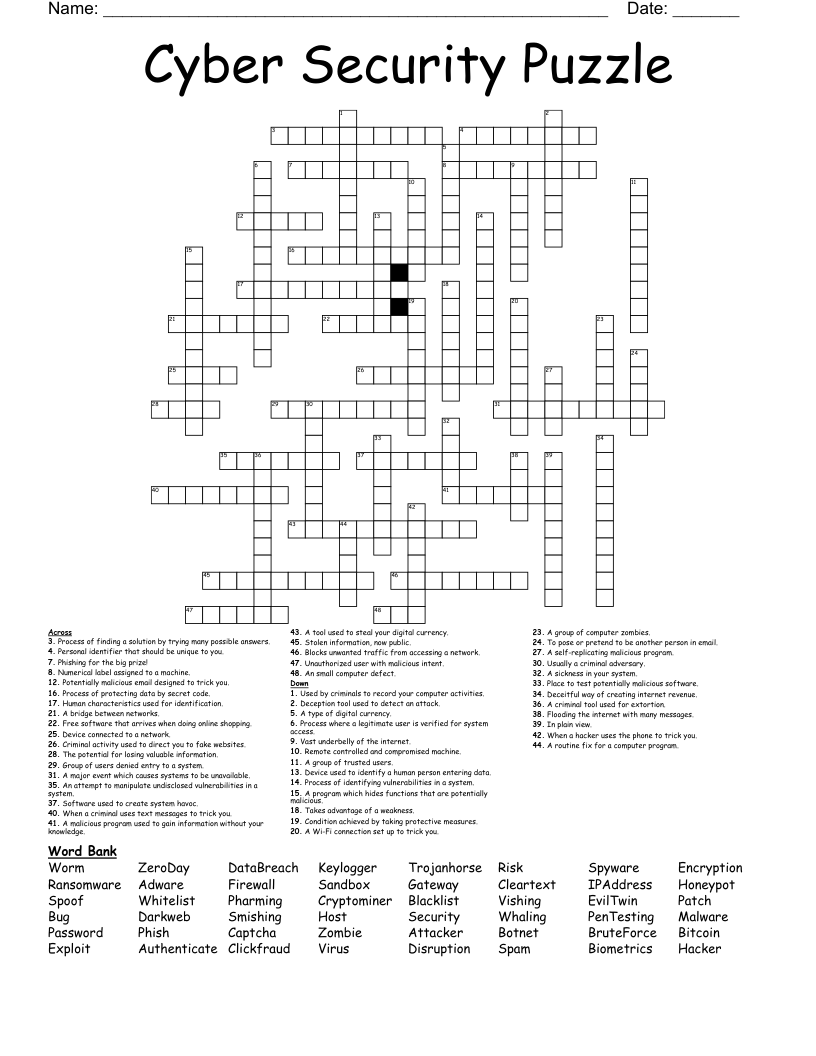
Cyber Security Puzzle Crossword
This printable crossword puzzle on the topic of Computer Science & Technology has 48 clues. Answers range from 3 to 12 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
Takes advantage of a weakness.
Free software that arrives when doing online shopping.
A major event which causes systems to be unavailable.
A program which hides functions that are potentially malicious.
Unauthorized user with malicious intent.
A criminal tool used for extortion.
Software used to create system havoc.
The potential for losing valuable information.
Blocks unwanted traffic from accessing a network.
A sickness in your system.
Deception tool used to detect an attack.
Process of protecting data by secret code.
Process where a legitimate user is verified for system access.
Human characteristics used for identification.
Process of finding a solution by trying many possible answers.
In plain view.
Device connected to a network.
Numerical label assigned to a machine.
Potentially malicious email designed to trick you.
A self-replicating malicious program.
Personal identifier that should be unique to you.
A routine fix for a computer program.
Process of identifying vulnerabilities in a system.
Place to test potentially malicious software.
Condition achieved by taking protective measures.
Flooding the internet with many messages.
To pose or pretend to be another person in email.
Remote controlled and compromised machine.
A group of computer zombies.
An attempt to manipulate undisclosed vulnerabilities in a system.
Deceitful way of creating internet revenue.
Vast underbelly of the internet.
A Wi-Fi connection set up to trick you.
Used by criminals to record your computer activities.
Criminal activity used to direct you to fake websites.
When a hacker uses the phone to trick you.
When a criminal uses text messages to trick you.
A bridge between networks.
Device used to identify a human person entering data.
Phishing for the big prize!
Usually a criminal adversary.
Group of users denied entry to a system.
A type of digital currency.
An small computer defect.
Stolen information, now public.
A group of trusted users.
A tool used to steal your digital currency.
A malicious program used to gain information without your knowledge.