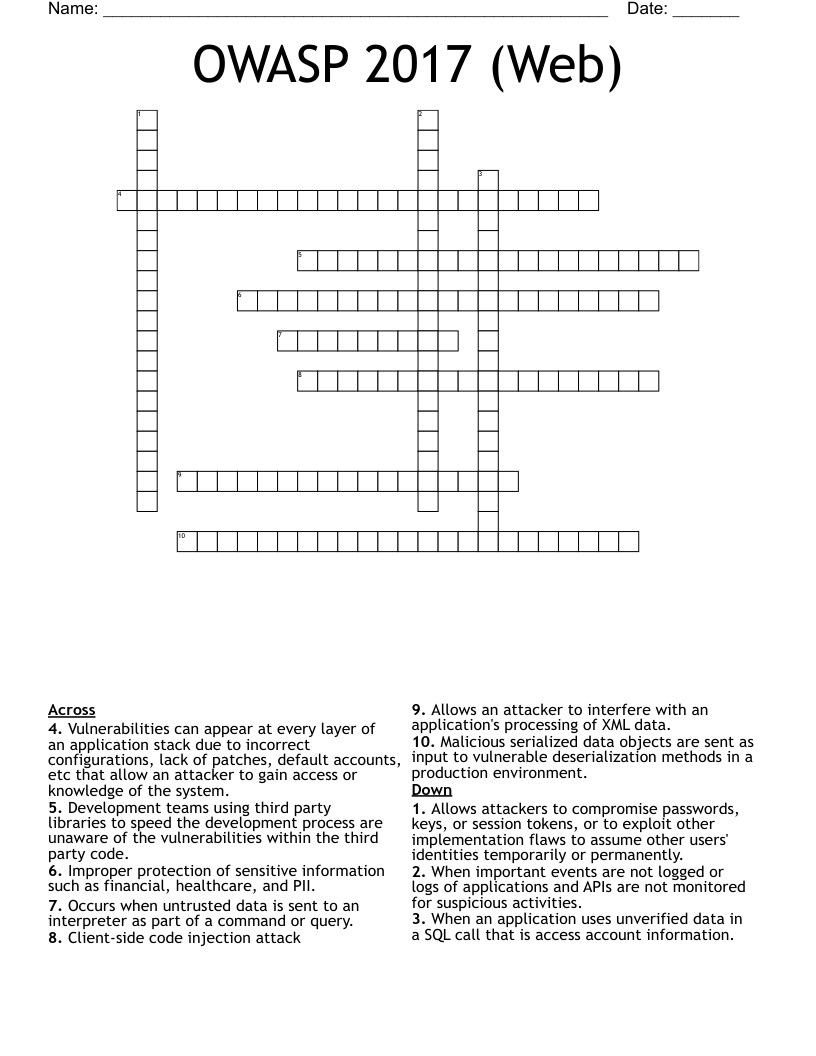
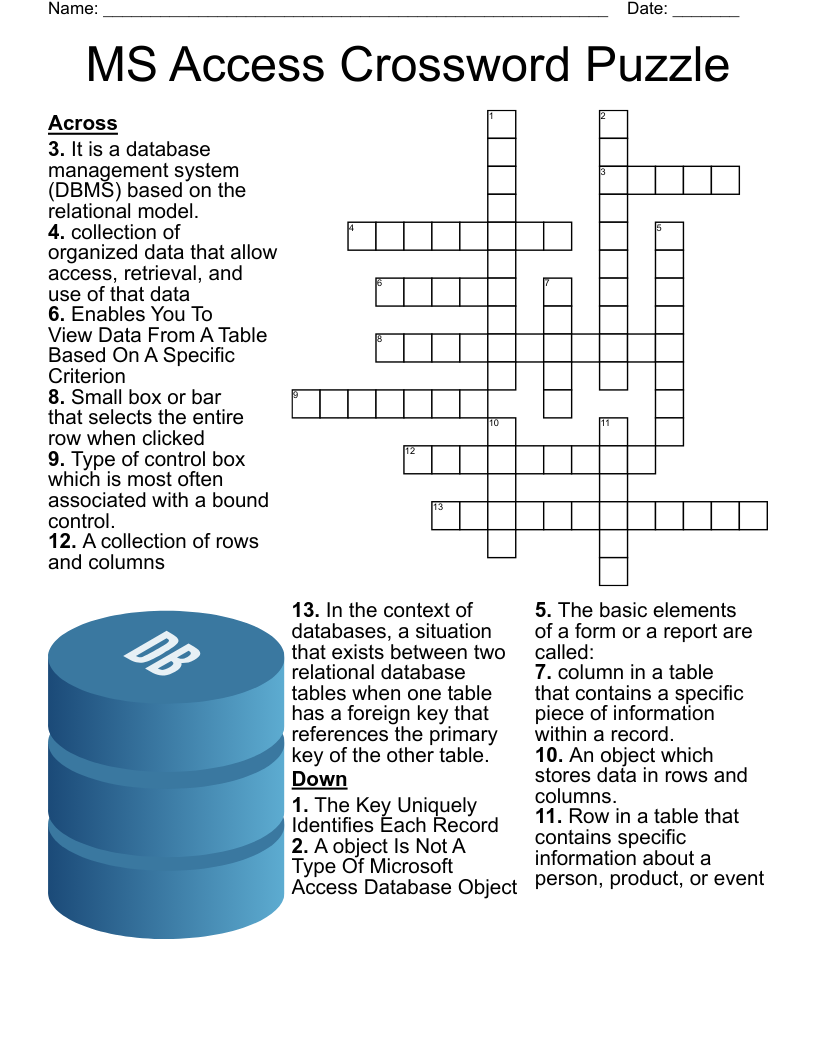
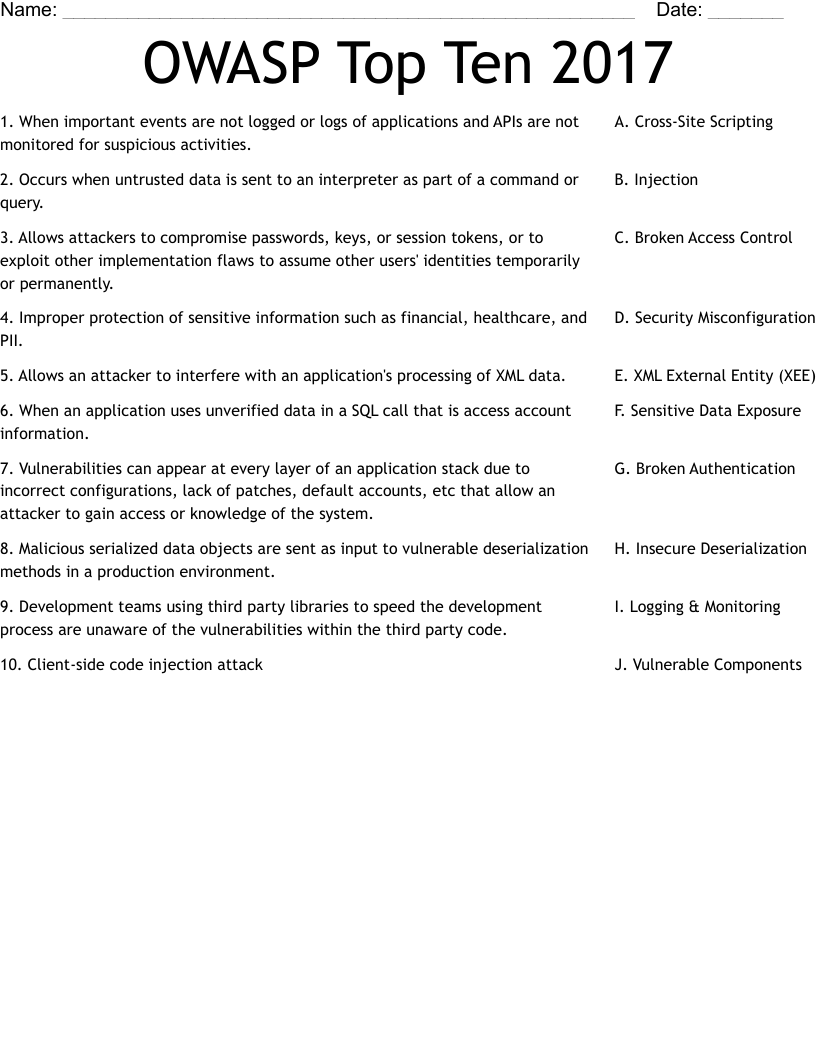
OWASP 2017 (Web) Crossword
This printable crossword puzzle on the topic of Computer Science & Technology has 10 clues. Answers range from 9 to 24 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
Occurs when untrusted data is sent to an interpreter as part of a command or query.
Allows attackers to compromise passwords, keys, or session tokens, or to exploit other implementation flaws to assume other users' identities temporarily or permanently.
Improper protection of sensitive information such as financial, healthcare, and PII.
Allows an attacker to interfere with an application's processing of XML data.
When an application uses unverified data in a SQL call that is access account information.
Vulnerabilities can appear at every layer of an application stack due to incorrect configurations, lack of patches, default accounts, etc that allow an attacker to gain access or knowledge of the system.
Malicious serialized data objects are sent as input to vulnerable deserialization methods in a production environment.
Development teams using third party libraries to speed the development process are unaware of the vulnerabilities within the third party code.
Client-side code injection attack
When important events are not logged or logs of applications and APIs are not monitored for suspicious activities.