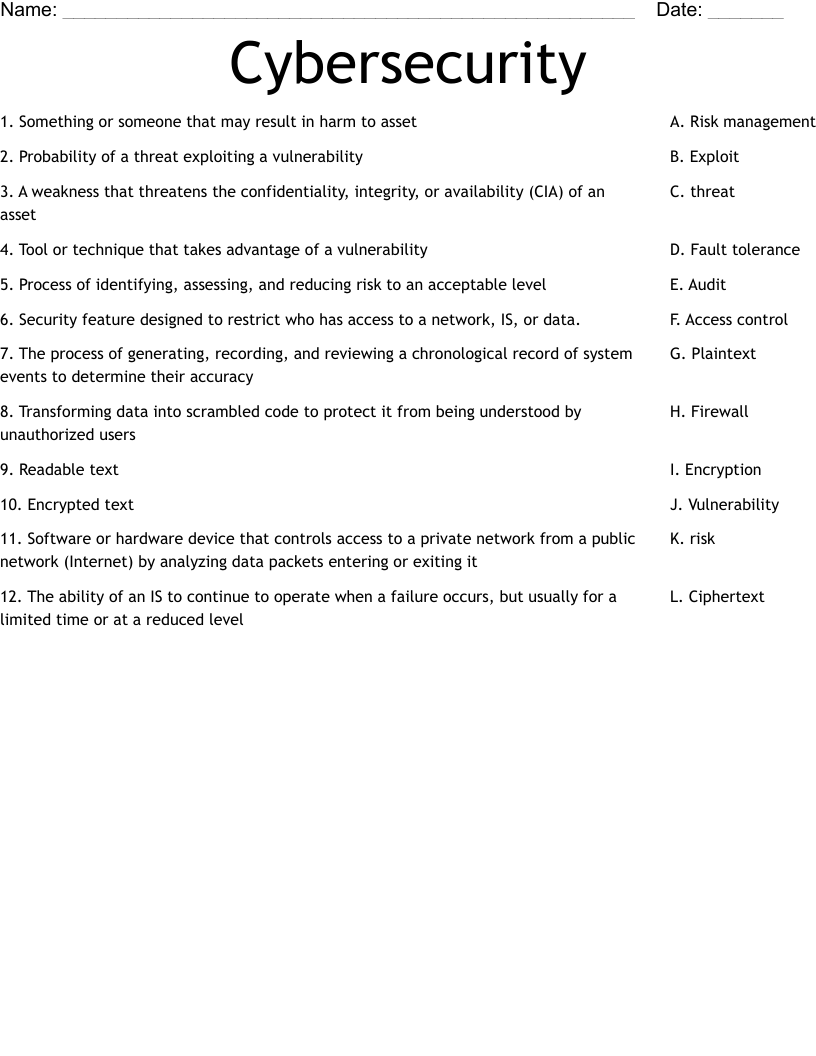
Cybersecurity Worksheet
This printable matching worksheet on the topic of Computer Science & Technology has 12 questions and answers to match. This matching worksheet is also available to download as a Microsoft Word document or a PDF.
Description
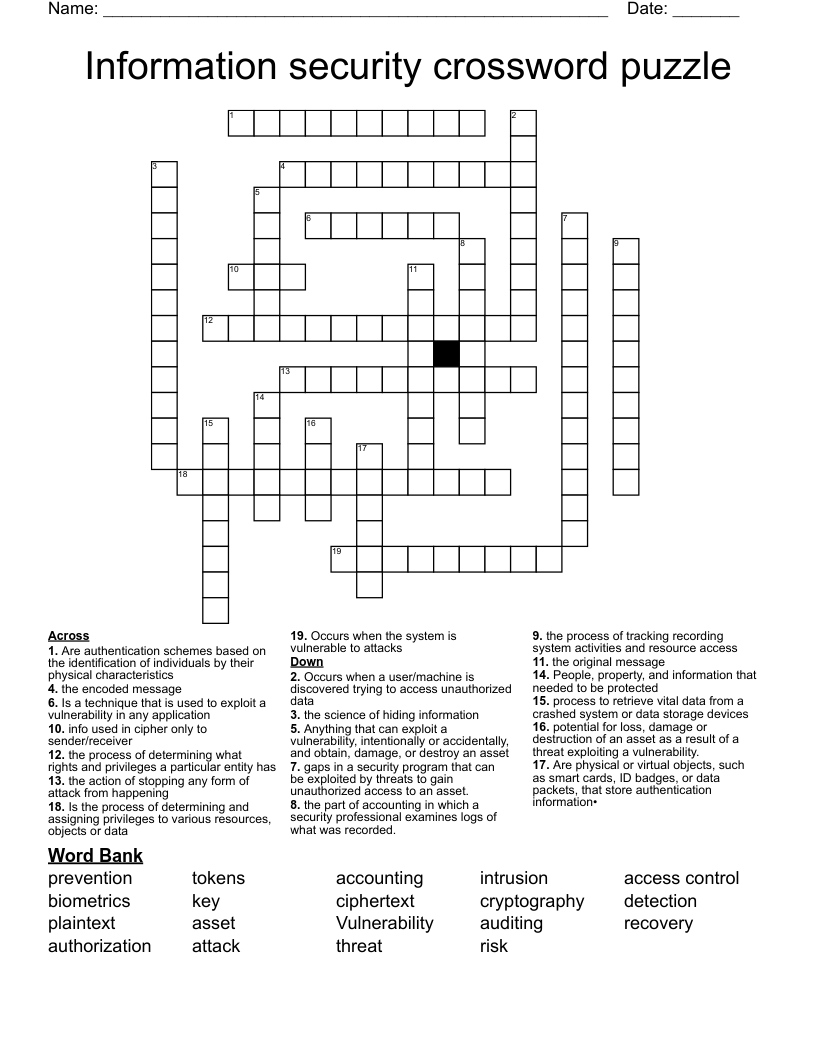
Something or someone that may result in harm to asset
Probability of a threat exploiting a vulnerability
A weakness that threatens the confidentiality, integrity, or availability (CIA) of an asset
Tool or technique that takes advantage of a vulnerability
Process of identifying, assessing, and reducing risk to an acceptable level
Security feature designed to restrict who has access to a network, IS, or data.
The process of generating, recording, and reviewing a chronological record of system events to determine their accuracy
Transforming data into scrambled code to protect it from being understood by unauthorized users
Readable text
Encrypted text
Software or hardware device that controls access to a private network from a public network (Internet) by analyzing data packets entering or exiting it
The ability of an IS to continue to operate when a failure occurs, but usually for a limited time or at a reduced level