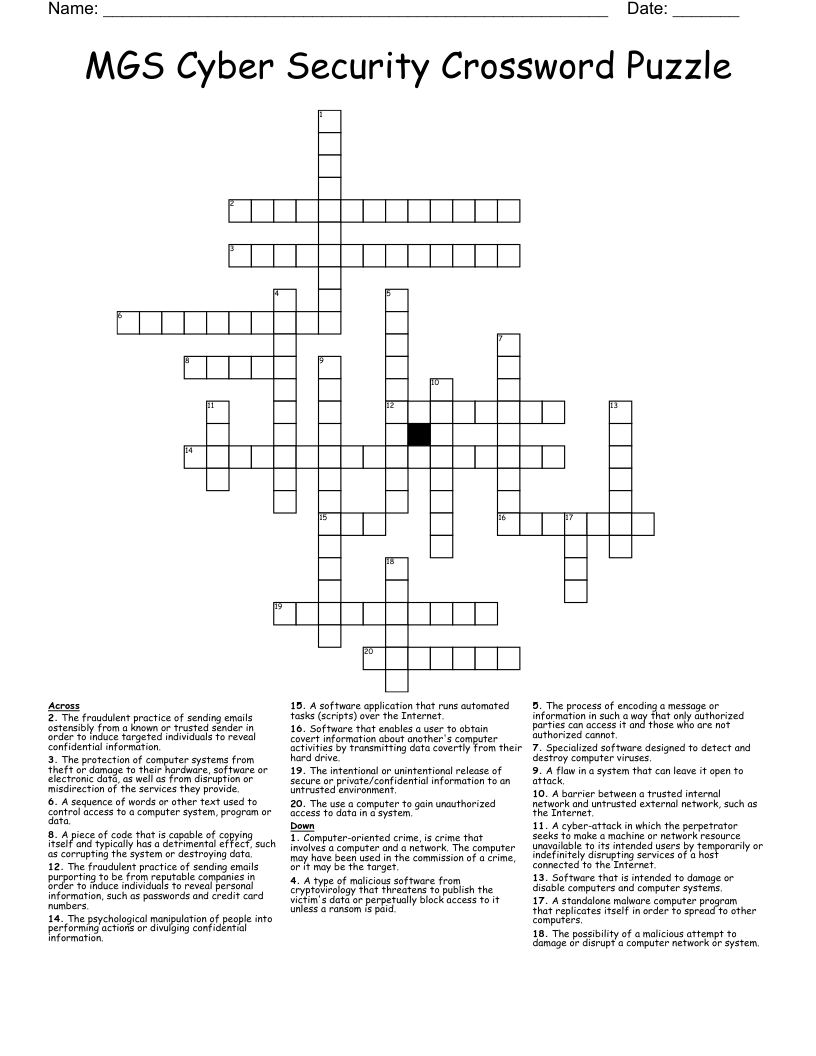
MGS Cyber Security Crossword Puzzle
This printable crossword puzzle on the topic of Computer Science & Technology has 20 clues. Answers range from 3 to 18 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
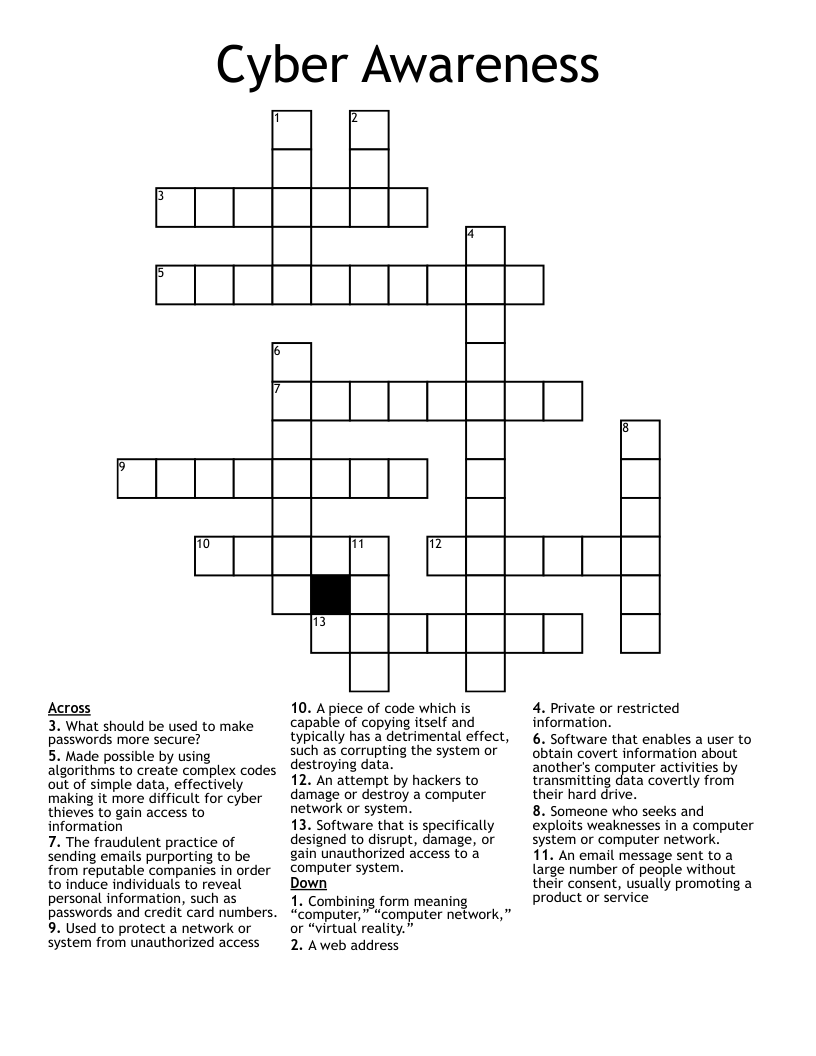
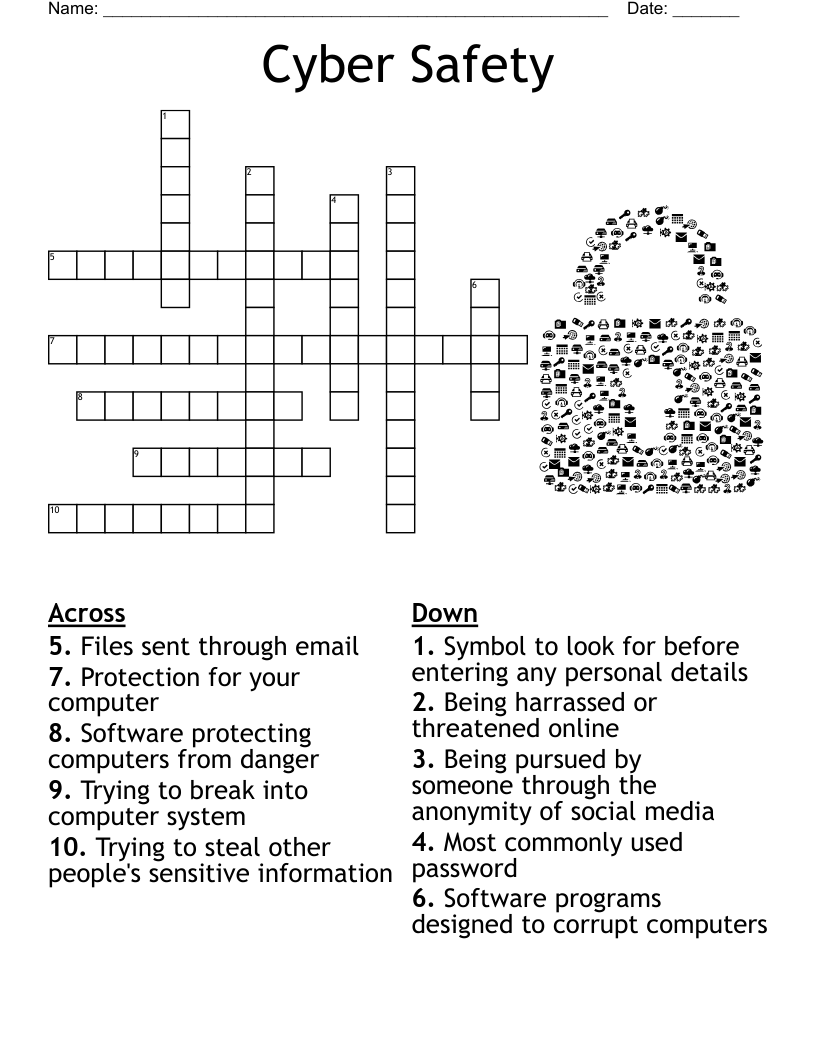
The fraudulent practice of sending emails purporting to be from reputable companies in order to induce individuals to reveal personal information, such as passwords and credit card numbers.
The psychological manipulation of people into performing actions or divulging confidential information.
Software that is intended to damage or disable computers and computer systems.
A sequence of words or other text used to control access to a computer system, program or data.
The use a computer to gain unauthorized access to data in a system.
A software application that runs automated tasks (scripts) over the Internet.
The possibility of a malicious attempt to damage or disrupt a computer network or system.
A piece of code that is capable of copying itself and typically has a detrimental effect, such as corrupting the system or destroying data.
The process of encoding a message or information in such a way that only authorized parties can access it and those who are not authorized cannot.
Software that enables a user to obtain covert information about another's computer activities by transmitting data covertly from their hard drive.
Specialized software designed to detect and destroy computer viruses.
A barrier between a trusted internal network and untrusted external network, such as the Internet.
A type of malicious software from cryptovirology that threatens to publish the victim's data or perpetually block access to it unless a ransom is paid.
Computer-oriented crime, is crime that involves a computer and a network. The computer may have been used in the commission of a crime, or it may be the target.
The protection of computer systems from theft or damage to their hardware, software or electronic data, as well as from disruption or misdirection of the services they provide.
The intentional or unintentional release of secure or private/confidential information to an untrusted environment.
The fraudulent practice of sending emails ostensibly from a known or trusted sender in order to induce targeted individuals to reveal confidential information.
A cyber-attack in which the perpetrator seeks to make a machine or network resource unavailable to its intended users by temporarily or indefinitely disrupting services of a host connected to the Internet.
A standalone malware computer program that replicates itself in order to spread to other computers.
A flaw in a system that can leave it open to attack.