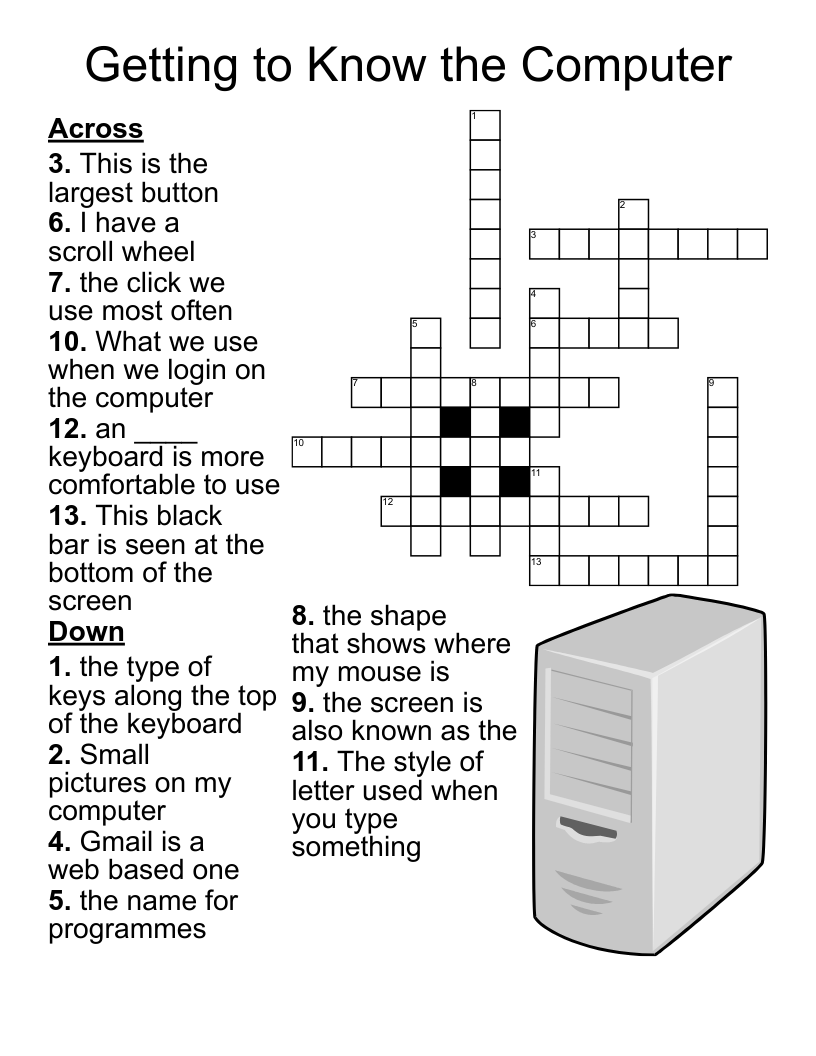
IT&S Cyber Security Crossword Puzzle
This printable crossword puzzle on the topic of Computer Science & Technology has 16 clues. Answers range from 4 to 10 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
A software that is designed and destroy computer viruses
Do not leave your laptop or computer ___________________
A ___________ is a hardware of a software that helps keep hackers from using your computer and it watches for outside attempts to access your system and blocks communication that you don't permit
Email scam or attempt to trick you into giving your password or personal information
The state of being free from danger and threat
A ___________ is often an email that gets mailed in chain letter fashion describing some devasting. highly unlikely type of virus.
Choose a password that is easy for you _______________ but hard for you someone to guess.
Also known as malicious software any; any program or file that is harmful to a computer user
Passwords should should always be at least this many characters long.
A _______ assessment is the process by which risks are identified and the impact of those risks determined
Applied to data to protect it from unauthorized use in case of theft or loss.
Always _______your computer when you leave your desk
To protect personal information, avoid sending it via
_________________ is a software that gathers computer user information and transmits it to the creator of the software without the explicit knowledge or informed consent of the user
A collection of information that is organized so that it can easily be accessed, managed and updated
Never share your _________ with another person