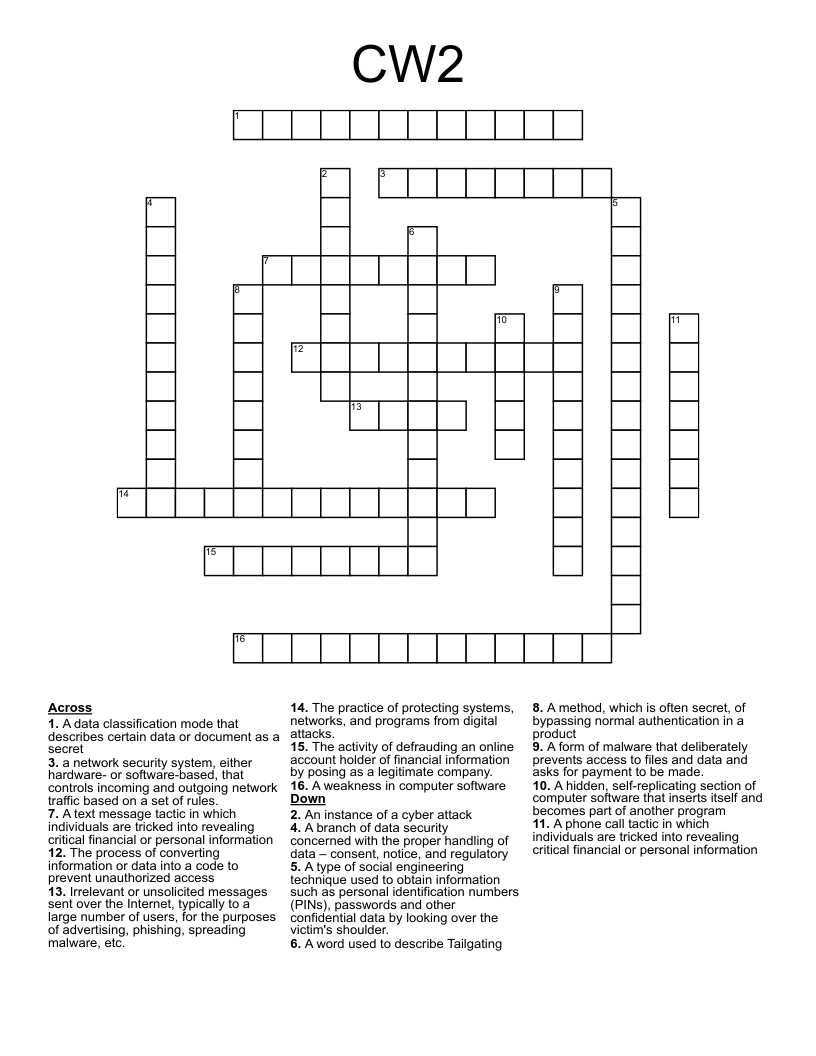
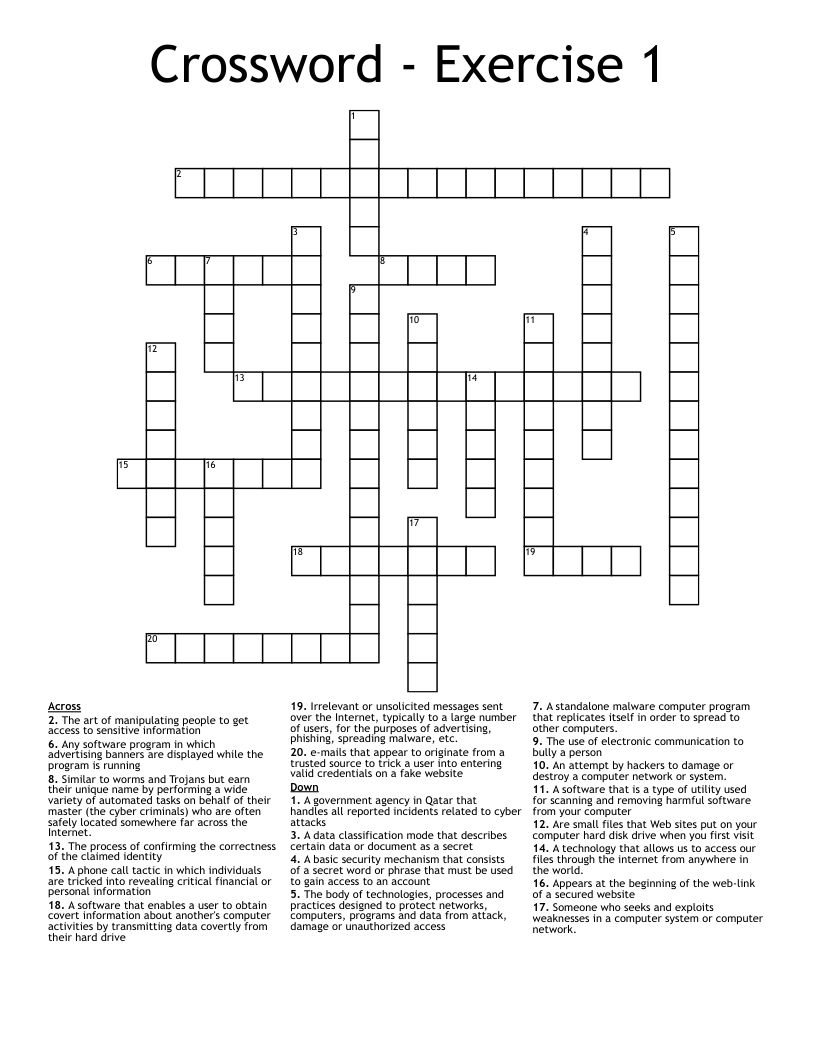
CW2 Crossword
This printable crossword puzzle has 16 clues. Answers range from 4 to 15 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
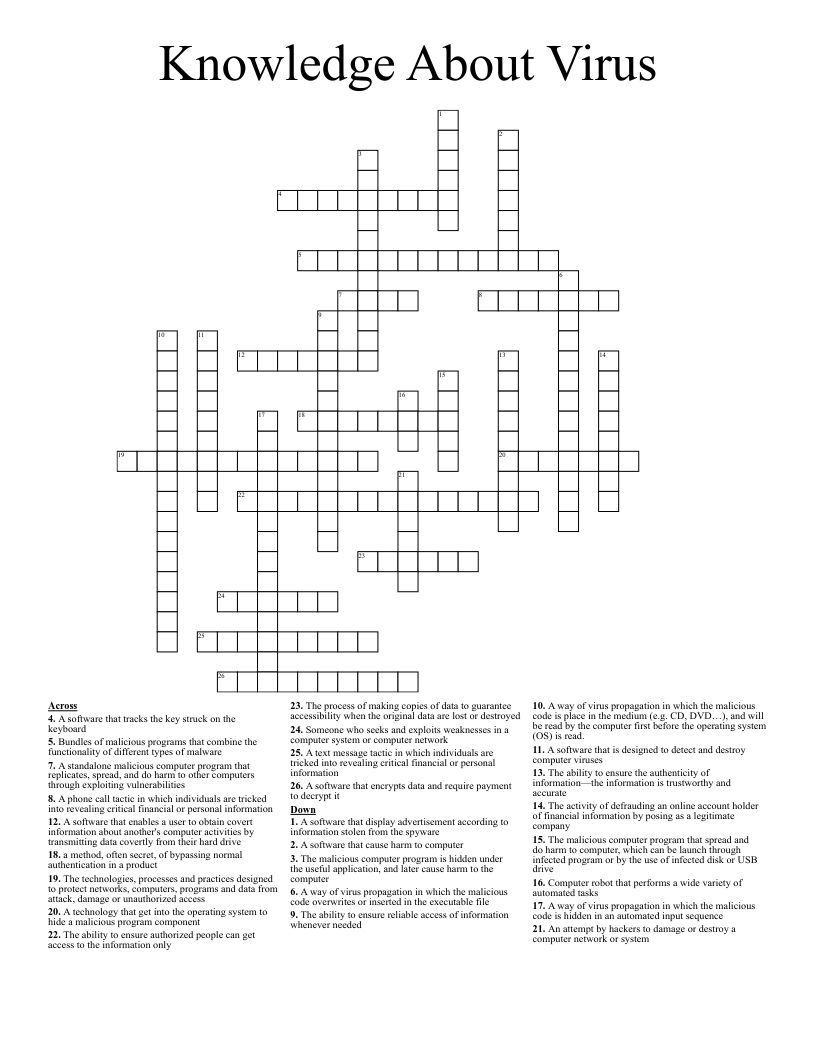
A method, which is often secret, of bypassing normal authentication in a product
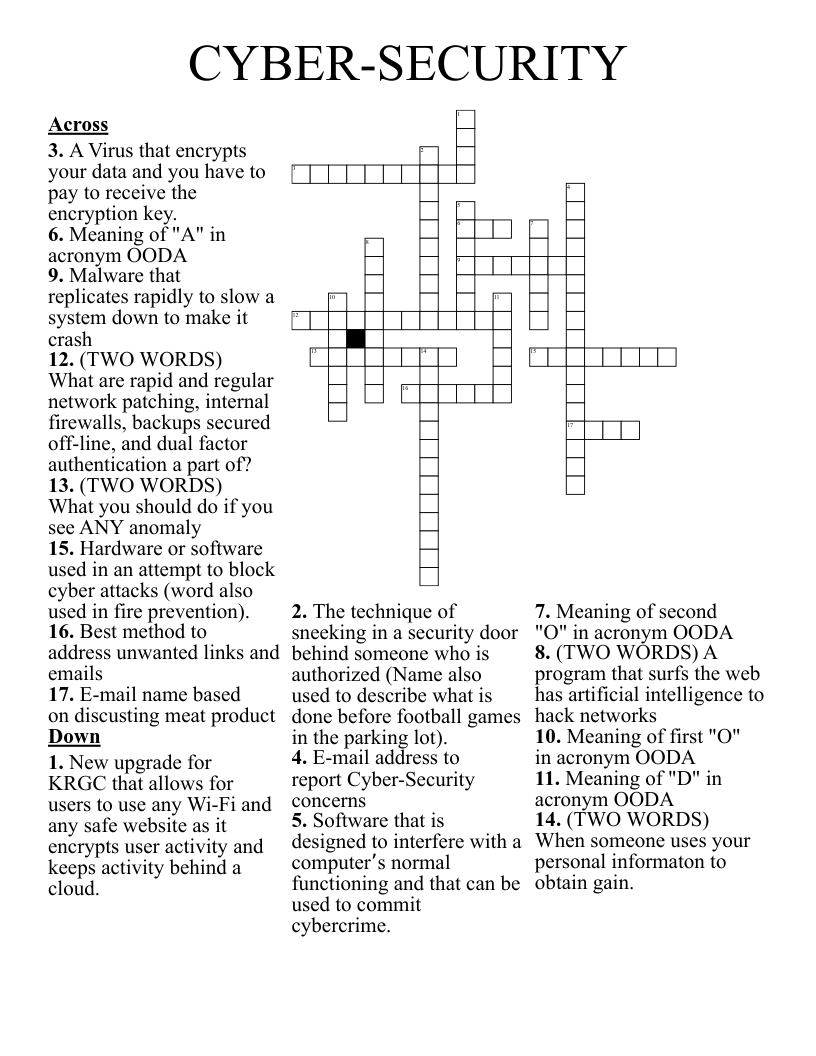
a network security system, either hardware- or software-based, that controls incoming and outgoing network traffic based on a set of rules.
A hidden, self-replicating section of computer software that inserts itself and becomes part of another program
A word used to describe Tailgating
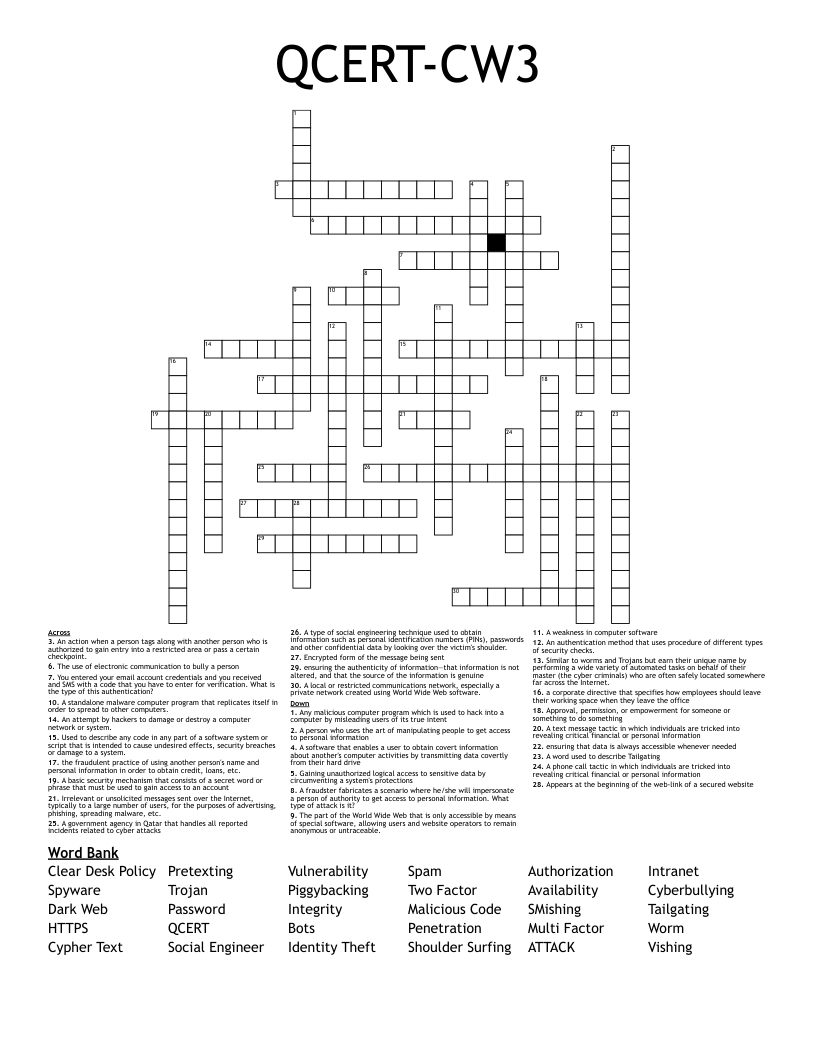
A type of social engineering technique used to obtain information such as personal identification numbers (PINs), passwords and other confidential data by looking over the victim's shoulder.
A branch of data security concerned with the proper handling of data – consent, notice, and regulatory
A form of malware that deliberately prevents access to files and data and asks for payment to be made.
A weakness in computer software
An instance of a cyber attack
A data classification mode that describes certain data or document as a secret
A text message tactic in which individuals are tricked into revealing critical financial or personal information
The process of converting information or data into a code to prevent unauthorized access
The activity of defrauding an online account holder of financial information by posing as a legitimate company.
The practice of protecting systems, networks, and programs from digital attacks.
Irrelevant or unsolicited messages sent over the Internet, typically to a large number of users, for the purposes of advertising, phishing, spreading malware, etc.
A phone call tactic in which individuals are tricked into revealing critical financial or personal information