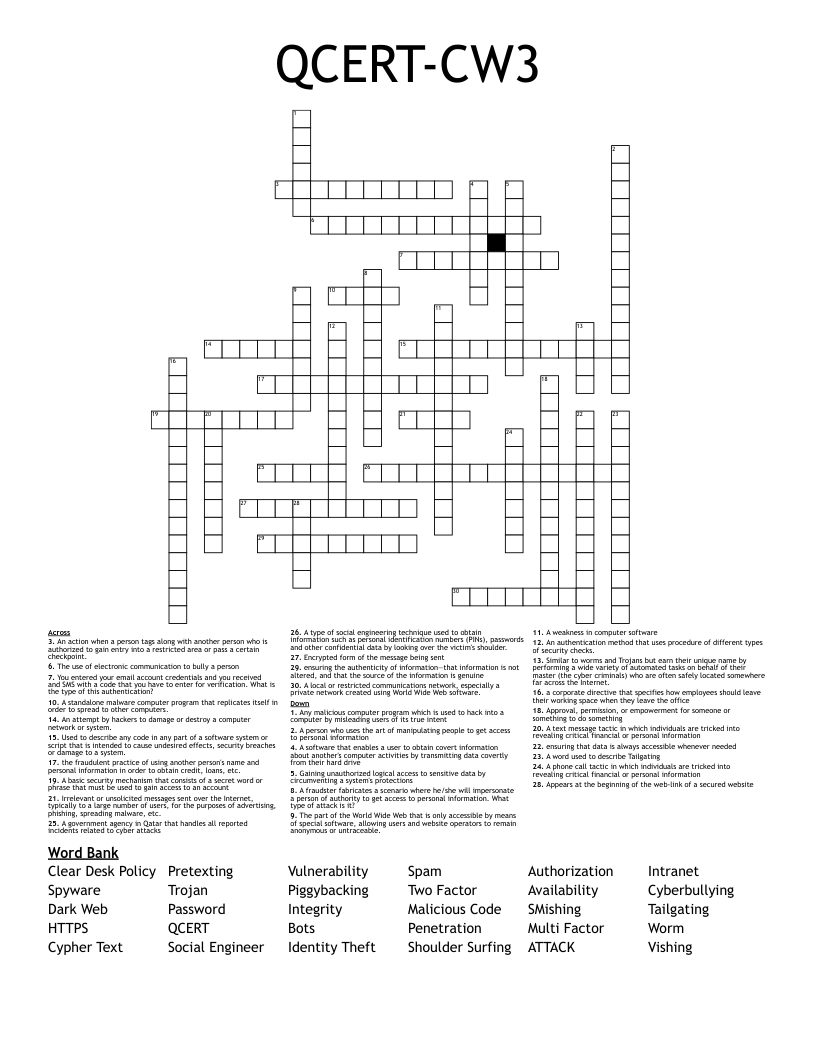
QCERT-CW3 Crossword
This printable crossword puzzle has 30 clues. Answers range from 4 to 15 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
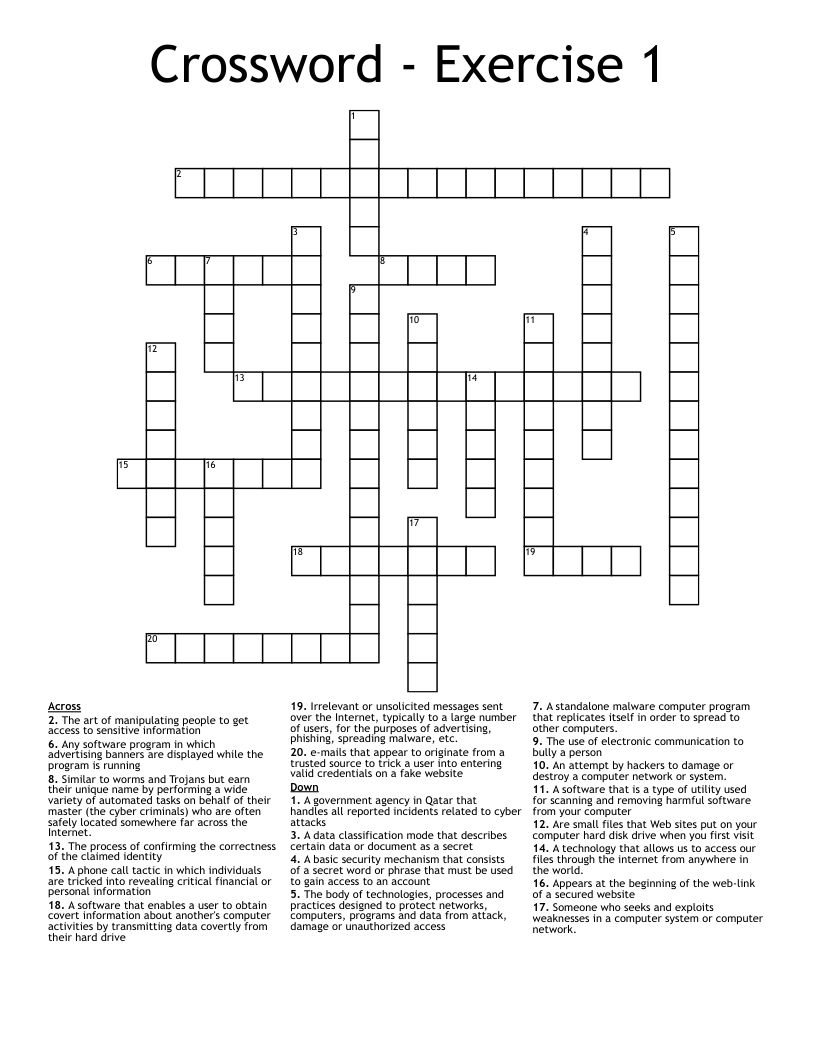
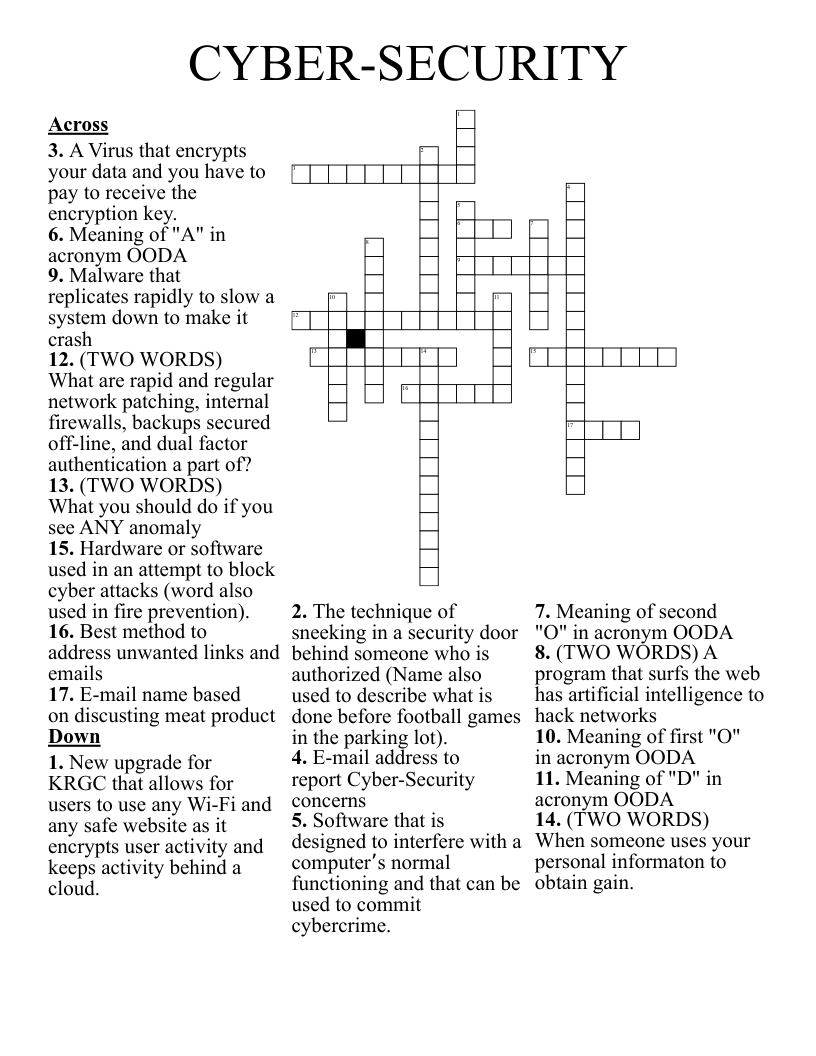
the fraudulent practice of using another person's name and personal information in order to obtain credit, loans, etc.
ensuring the authenticity of information—that information is not altered, and that the source of the information is genuine
A local or restricted communications network, especially a private network created using World Wide Web software.
Used to describe any code in any part of a software system or script that is intended to cause undesired effects, security breaches or damage to a system.
An authentication method that uses procedure of different types of security checks.
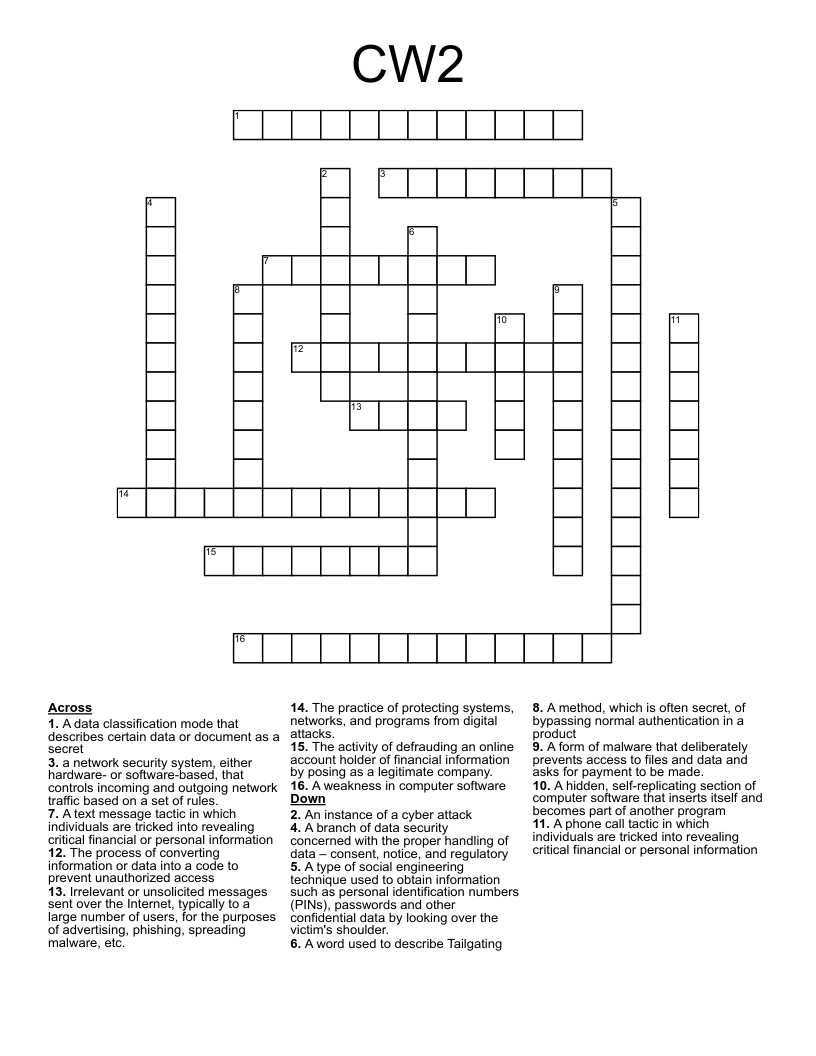
A basic security mechanism that consists of a secret word or phrase that must be used to gain access to an account
Gaining unauthorized logical access to sensitive data by circumventing a system's protections
A word used to describe Tailgating
A fraudster fabricates a scenario where he/she will impersonate a person of authority to get access to personal information. What type of attack is it?
A government agency in Qatar that handles all reported incidents related to cyber attacks
A type of social engineering technique used to obtain information such as personal identification numbers (PINs), passwords and other confidential data by looking over the victim's shoulder.
A text message tactic in which individuals are tricked into revealing critical financial or personal information
A person who uses the art of manipulating people to get access to personal information
Irrelevant or unsolicited messages sent over the Internet, typically to a large number of users, for the purposes of advertising, phishing, spreading malware, etc.
A software that enables a user to obtain covert information about another's computer activities by transmitting data covertly from their hard drive
An action when a person tags along with another person who is authorized to gain entry into a restricted area or pass a certain checkpoint.
Any malicious computer program which is used to hack into a computer by misleading users of its true intent
An attempt by hackers to damage or destroy a computer network or system.
ensuring that data is always accessible whenever needed
Similar to worms and Trojans but earn their unique name by performing a wide variety of automated tasks on behalf of their master (the cyber criminals) who are often safely located somewhere far across the Internet.
Appears at the beginning of the web-link of a secured website
Encrypted form of the message being sent
The use of electronic communication to bully a person
The part of the World Wide Web that is only accessible by means of special software, allowing users and website operators to remain anonymous or untraceable.
Approval, permission, or empowerment for someone or something to do something
A standalone malware computer program that replicates itself in order to spread to other computers.
A weakness in computer software
A phone call tactic in which individuals are tricked into revealing critical financial or personal information
a corporate directive that specifies how employees should leave their working space when they leave the office
You entered your email account credentials and you received and SMS with a code that you have to enter for verification. What is the type of this authentication?