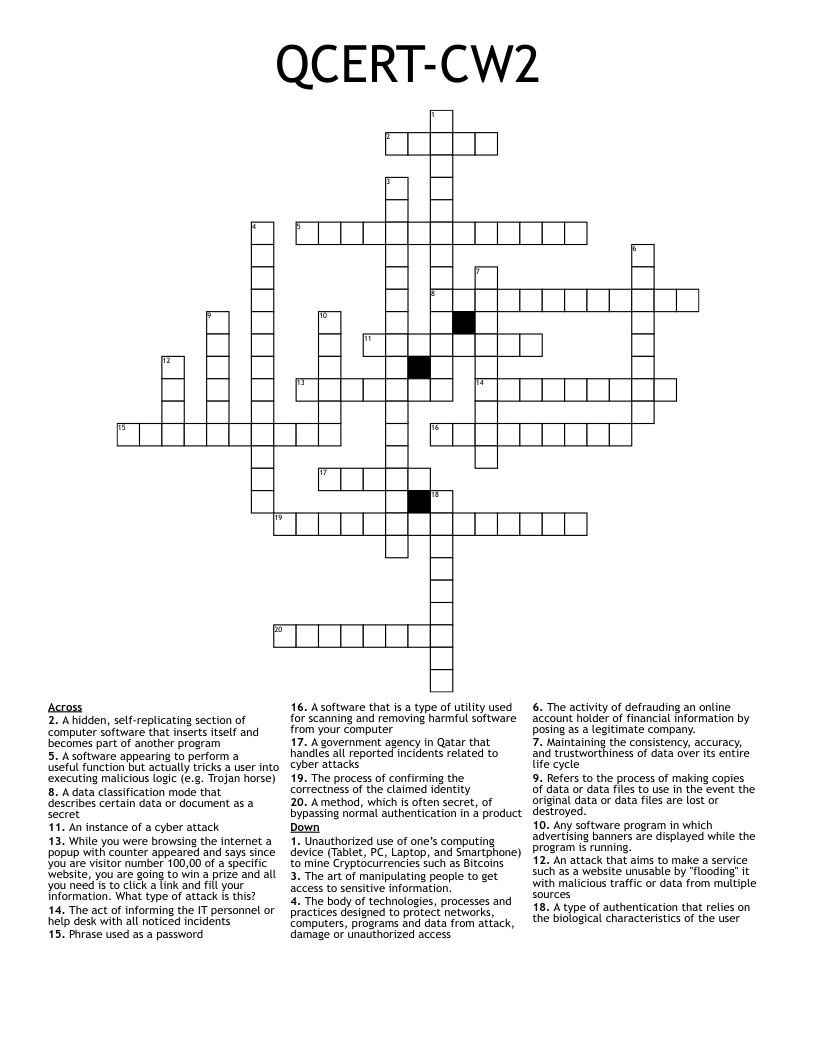
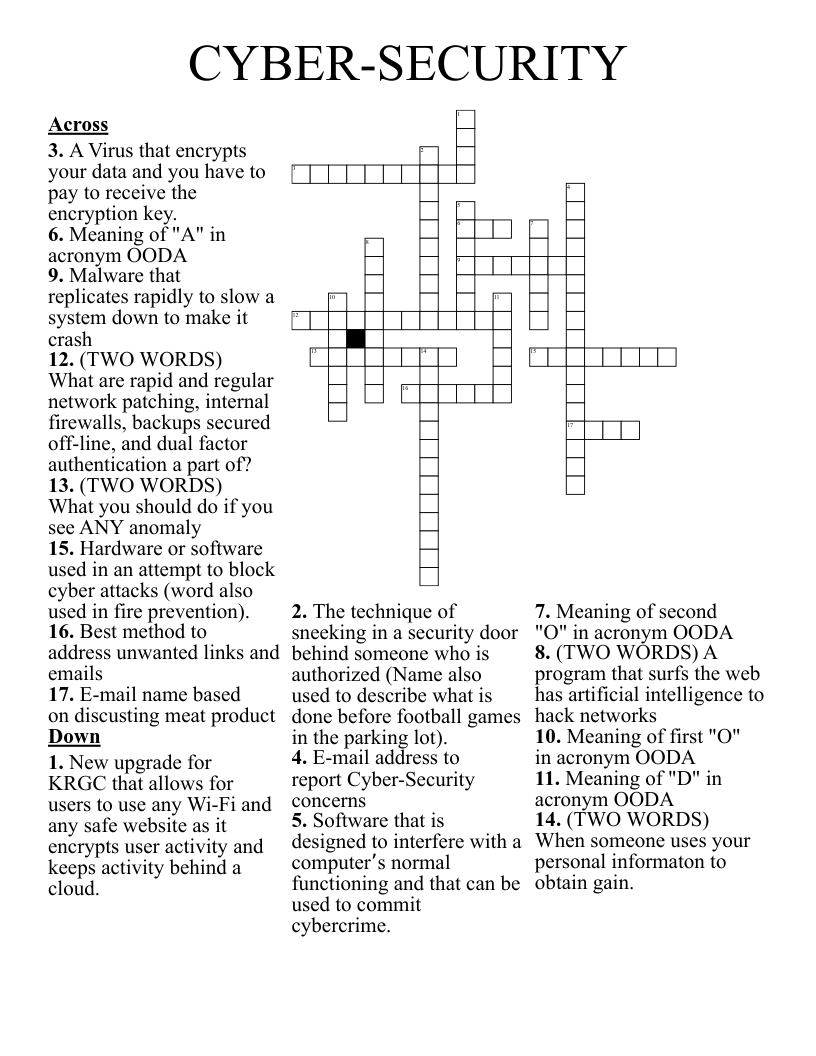
QCERT-CW2 Crossword
This printable crossword puzzle has 20 clues. Answers range from 4 to 17 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
Any software program in which advertising banners are displayed while the program is running.
A software that is a type of utility used for scanning and removing harmful software from your computer
The process of confirming the correctness of the claimed identity
A method, which is often secret, of bypassing normal authentication in a product
Refers to the process of making copies of data or data files to use in the event the original data or data files are lost or destroyed.
While you were browsing the internet a popup with counter appeared and says since you are visitor number 100,00 of a specific website, you are going to win a prize and all you need is to click a link and fill your information. What type of attack is this?
A type of authentication that relies on the biological characteristics of the user
A data classification mode that describes certain data or document as a secret
Unauthorized use of one’s computing device (Tablet, PC, Laptop, and Smartphone) to mine Cryptocurrencies such as Bitcoins
The body of technologies, processes and practices designed to protect networks, computers, programs and data from attack, damage or unauthorized access
An attack that aims to make a service such as a website unusable by "flooding" it with malicious traffic or data from multiple sources
An instance of a cyber attack
Maintaining the consistency, accuracy, and trustworthiness of data over its entire life cycle
A software appearing to perform a useful function but actually tricks a user into executing malicious logic (e.g. Trojan horse)
Phrase used as a password
The activity of defrauding an online account holder of financial information by posing as a legitimate company.
A government agency in Qatar that handles all reported incidents related to cyber attacks
The act of informing the IT personnel or help desk with all noticed incidents
The art of manipulating people to get access to sensitive information.
A hidden, self-replicating section of computer software that inserts itself and becomes part of another program