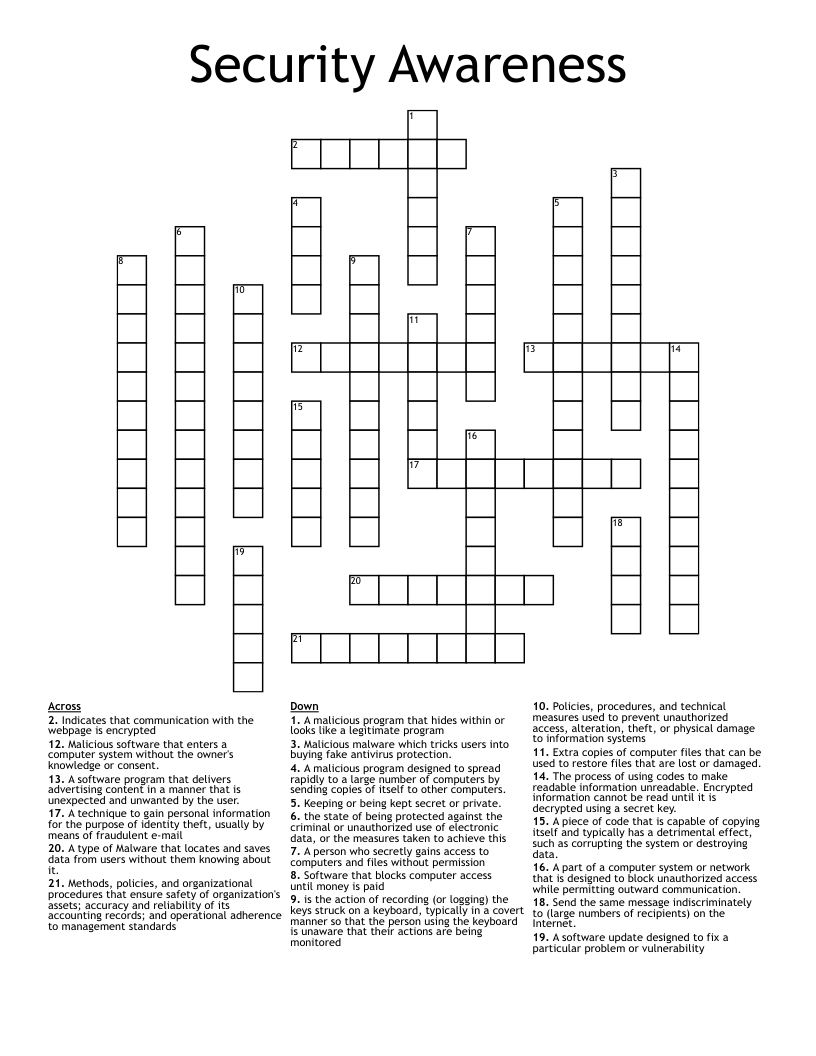
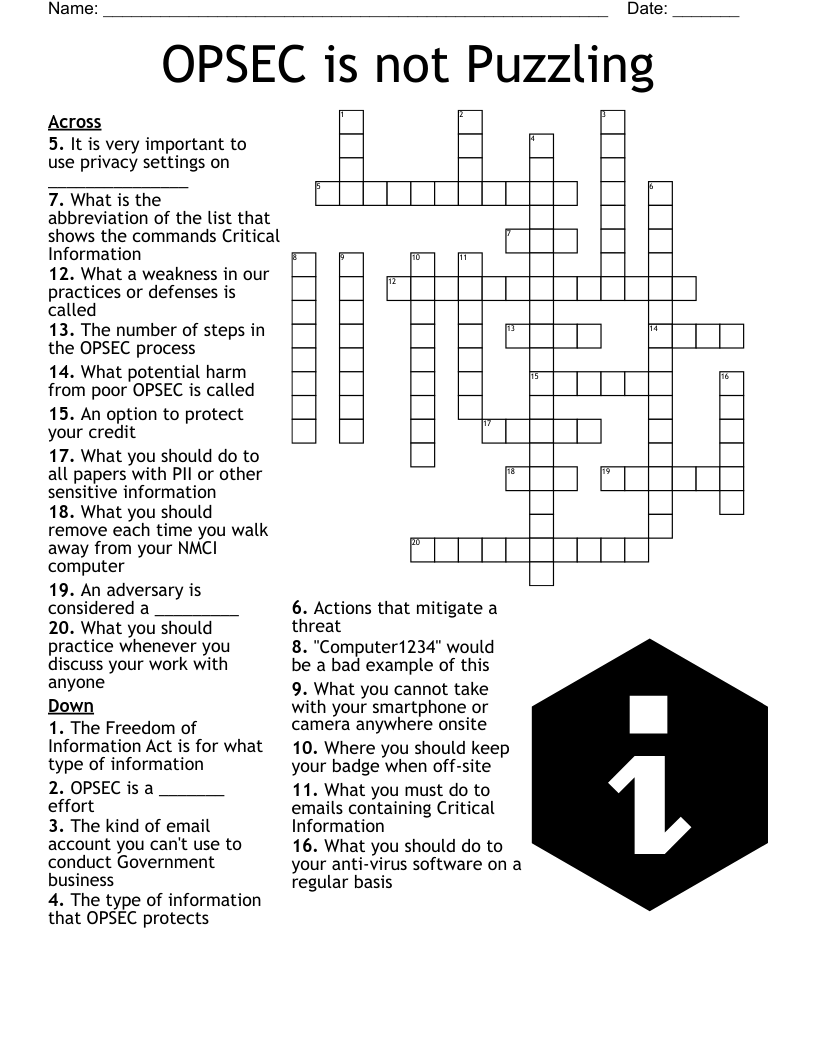
Security Awareness Crossword
This printable crossword puzzle on the topic of Computer Science & Technology has 21 clues. Answers range from 4 to 13 letters long. This crossword is also available to download as a Microsoft Word document or a PDF.
Description
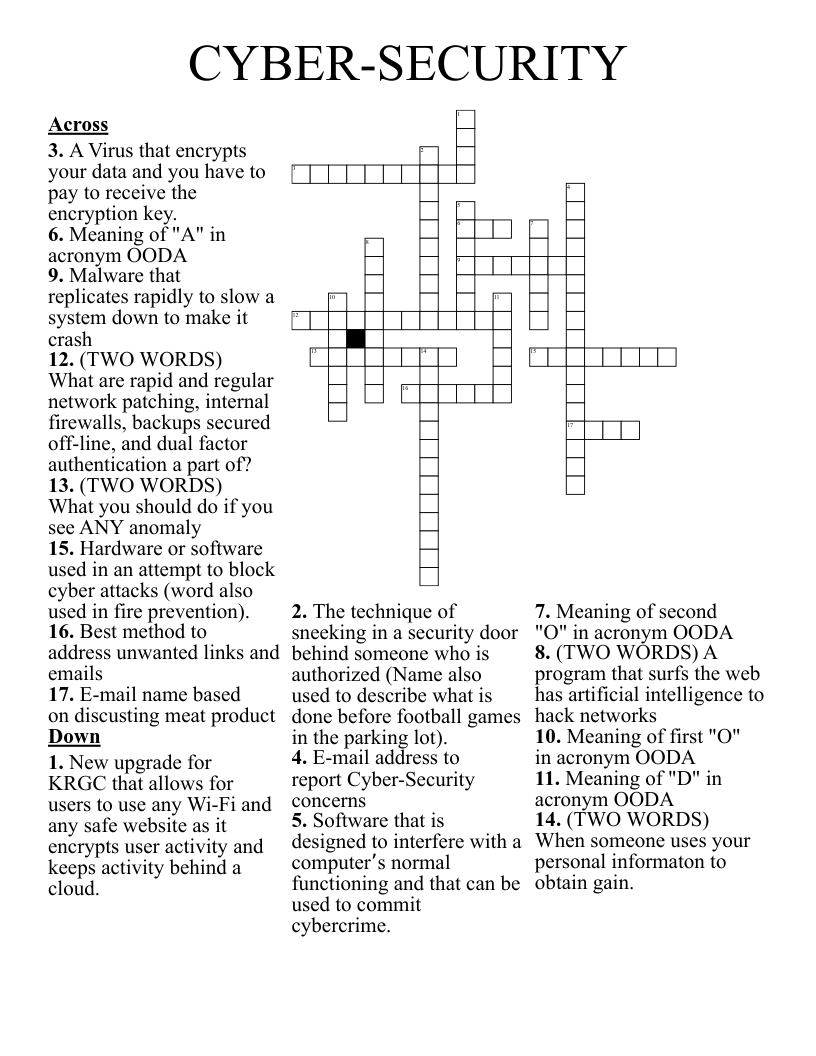
A software update designed to fix a particular problem or vulnerability
Indicates that communication with the webpage is encrypted
A software program that delivers advertising content in a manner that is unexpected and unwanted by the user.
A person who secretly gains access to computers and files without permission
Malicious software that enters a computer system without the owner's knowledge or consent.
A technique to gain personal information for the purpose of identity theft, usually by means of fraudulent e-mail
Send the same message indiscriminately to (large numbers of recipients) on the Internet.
A type of Malware that locates and saves data from users without them knowing about it.
A piece of code that is capable of copying itself and typically has a detrimental effect, such as corrupting the system or destroying data.
is the action of recording (or logging) the keys struck on a keyboard, typically in a covert manner so that the person using the keyboard is unaware that their actions are being monitored
A malicious program that hides within or looks like a legitimate program
A malicious program designed to spread rapidly to a large number of computers by sending copies of itself to other computers.
Policies, procedures, and technical measures used to prevent unauthorized access, alteration, theft, or physical damage to information systems
Methods, policies, and organizational procedures that ensure safety of organization's assets; accuracy and reliability of its accounting records; and operational adherence to management standards
the state of being protected against the criminal or unauthorized use of electronic data, or the measures taken to achieve this
A part of a computer system or network that is designed to block unauthorized access while permitting outward communication.
Extra copies of computer files that can be used to restore files that are lost or damaged.
The process of using codes to make readable information unreadable. Encrypted information cannot be read until it is decrypted using a secret key.
Keeping or being kept secret or private.
Software that blocks computer access until money is paid
Malicious malware which tricks users into buying fake antivirus protection.